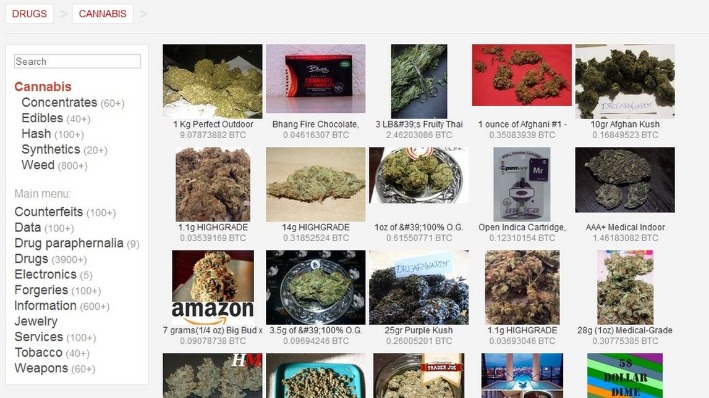
As a result, the trading of illegal goods online has become more commonplace, and vast dark web marketplaces have been created. At KELA, we help you identify and mitigate risks by providing actionable intelligence from the darknet. Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation. Cybersecurity companies and researchers monitoring darknet markets face legal and ethical restrictions.
Classification Of Sellers And Buyers
Using TAILS is yet another security measure that protects your online identity on the dark web. It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer. It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance. A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops. These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private. Vice City Market is a new and cutting-edge dark web marketplace where you can find a range of products and vendors at an affordable price (compared to the damage they do to the victims).

3 Financial Security
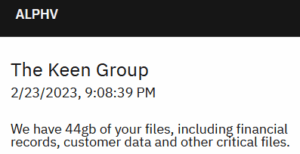
These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”. There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks. A study, Into the Web of Profit, conducted by Dr. Michael McGuires at the University of Surrey, shows that things have become worse. The number of dark web listings that could harm an enterprise has risen by 20% from 2016 to 2019.
Easy – Extremely Simple How To Use Monero (Video Tutorial)
They are followed by market-U2U sellers, then market-only sellers, and lastly U2U-only sellers. Therefore, although larger in number, U2U-only sellers typically make the smallest income. This suggests that sellers with more diverse sources of income, such as multisellers and market-U2U sellers, are able to produce a higher income. Additionally, we observe that, except for U2U-only sellers, the median income of the other types of sellers drops after the major shock caused by operation Bayonet (see Supplementary Information Section S4).
As these platforms grow more secure, decentralized, and integrated into broader digital ecosystems, their influence expands. Dark web operators use mainstream social media platforms to promote illicit goods. Advertisements for fake passports, stolen credit card dumps, and malware appear in private groups, often disguised with coded language. Once contact is made, vendors transition discussions to secure messaging apps to complete the transaction.
Vendors on Hydra also offered services such as “Hacking for Hire,” “Ransomware as a Service” (“RaaS”), and a myriad of money laundering features. Though the drug transactions were limited to Russia and its geographic neighbors, the cyber and money laundering tools were available to anyone in the world willing to pay. The darknet is used for anonymous communication, accessing censored information, and protecting privacy. Journalists and activists use it to communicate securely in oppressive regimes. You can access it for legitimate purposes like whistleblowing and freedom of expression. However, it’s also used for illegal activities like drug trafficking, weapon sales, and stolen data trading.
Treasury Designates Cryptocurrency Exchange Chatex
The market frequently makes headlines for releasing massive troves of stolen data, often as a way to advertise its services. Transactions are conducted through Bitcoin and Monero which provides anonymity for both buyers and sellers. A Canadian market established in 2021, WTN offers over 9,000 products, including narcotics, fake goods, and digital services. It operates in both French and English and has built a reputation for ease-of-use.
Risks And Dangers
- Temporal network of multisellers (top) and multibuyers (bottom) between markets for each year.
- David is a programmer and writer who has worked as a software developer at MIT.
- That said, the social network’s data collection and tracking practices may seem at odds with many of the principles motivating dark web users.
- That’s “a special-use top level domain suffix designating an anonymous hidden service reachable via the Tor network,” according to Wikipedia.
- We find that trading properties of buyers and sellers reflect the dominance of DWMs in the ecosystem.
These innovations challenge law enforcement and raise new questions about regulation and control. Venture deeper into the underbelly of the dark web, where bustling marketplaces hum with activity and cryptic figures pull the strings. This article unveils the prominent players, explores the vendor ecosystem, and delves into the security measures employed in this digital Wild West.
The Dark Web As A Platform For Crime: An Exploration Of Illicit Drug, Firearm, CSAM, And Cybercrime Markets
The lifeblood of these virtual bazaars pulsates through the veins of its vendors. These individuals or groups offer the goods and services on underground dark web markets, shaping the marketplace’s appeal and attracting customers. Building trust is paramount in this anonymous environment, and most marketplaces have robust reputation systems based on customer feedback and ratings. However, beware the alluring facade – fake reviews and fraudulent vendors lurk in the shadows, eager to exploit the unwary. Law enforcement agencies and international coalitions play a critical role in countering dark web activities. Operations such as the takedown of the Silk Road and AlphaBay marketplaces demonstrate the global effort required to dismantle these illicit networks.
We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal. The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech. “A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said.
To track the transactions of markets and users as entities, the data need to be pre-processed in order to map groups of addresses into entities. You face significant risks when using dark markets, including scams where vendors take payment without delivering goods. There’s high exposure to malware and cybersecurity threats that can steal your personal information. Law enforcement agencies actively monitor these markets and can track users despite anonymity measures. You risk legal consequences if caught participating in illegal transactions. Financial fraud is common, and you have no recourse if transactions go wrong since these markets operate outside legal frameworks.
These groups use dark web platforms to sell stolen secrets, acquire hacking tools, or coordinate with other criminal organizations. Decentralized marketplaces, powered by blockchain technology, aim to eliminate central authorities and enhance anonymity. Multi-signature wallets boost security by requiring multiple parties to authorize transactions.
That push led to the arrest of Ross Ulbricht, the founder of Silk Road, after a long and intense investigation. While you could find all sorts of products on Silk Road, drug sales quickly became prevalent because of the profits it raked in. In fact, by 2013, a Guardian article revealed that about 70% of listings were drug-related. So, what even is this dark web, and why are these marketplaces present there?