However, if you’re communicating with state intelligence agencies, you should use Tor alongside a VPN for maximum...
websites
It’s alleged that the strange noises and voices are actually coded messages, probably sent by secret operatives....
It uses TrustedServer technology on the entire server network to wipe out your data after every session....
Founded in 1998 as Ixquick.com, we later changed the name to Startpage.com. If you’re not using Tor,...
Since the Hidden Wiki can be a hotbed for scams, explain best practices for verifying links before...
The platform’s popularity continues to grow, attracting both new and returning customers. It has built a reputation...
Your activities on the dark web are not entirely shielded from tracking, and relying solely on anonymity...
The internet’s favorite alternative to Google made a name for itself by not logging your search activity...
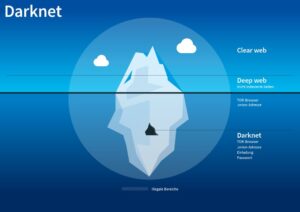
Onion websites use onion routing, a technique for encrypting and anonymizing data transmitted over the Tor network....
The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection...