
However, if you’re communicating with state intelligence agencies, you should use Tor alongside a VPN for maximum privacy. Otherwise, the first node in the onion relay system sees your real IP address, which can be used to locate you and unveil your identity. It is an archive stored on the Dark Web that keeps a snapshot of websites on the surface internet. The useful site allows you to see how a website looked at an earlier date. This lets you check what information it contained at a previous point in time.
What Is The Process For Obtaining A Certificate For An Onion Domain?
Accessing it through an onion link is much more convenient if you’re unable to directly view it on your screen. As you can imagine, the dark web has some forums filled with the types of characters who are best avoided. However, one of the less obscene discussion sites is Raddle, named and styled somewhat in the style of Reddit. Join millions of users who trust ForestVPN for privacy and unrestricted internet access. Viney Dhiman, the mind behind GeekerMag, is a seasoned content writer with over 12 years of experience.
Avoid clicking links posted on surface web comment sections or unverified forums. And never bookmark .onion links unless you’re sure they come from a trusted, PGP-signed source. ProPublica made history by becoming one of the first major investigative journalism outlets to launch a .onion mirror. This version of their site allows readers in restrictive countries to access groundbreaking journalism without censorship or surveillance. It is identical to the surface web version in content but built with privacy in mind.
What Is The Hidden Wiki Used For?
- The Tor routing innovations created for US intelligence agents are now used by a variety of everyday users who value their online privacy and data security.
- This makes it even harder for third parties to see your email traffic.
- For those needing an additional layer of security, you can set it to disappear right after viewing.
- That’s why relying on trusted onion directories like Ahmia, Dark.Fail, OnionLinks — and the real Hidden Wiki — are essential.
- The social media giant is also aware of the many attempts by repressive regimes to restrict its access.
Once pasted, the Tor Browser will connect to the site over the Tor network, which might take a few seconds longer than a normal website. Remember to always keep your browser updated to the latest version, as this ensures you benefit from the newest security patches and performance improvements. The Tor Browser looks and feels similar to a regular web browser but is configured to prioritize privacy and security by default. It blocks browser trackers and resists fingerprinting, which helps maintain your anonymity while browsing.
Subscribe To The Blog Newsletter
By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity. They have an onion site as well, presumably to allow access to the website’s content in countries that aren’t so friendly to the notorious intelligence agency’s … Pissmail is the service for you, offering an onion based web service accessible via Tor browser. Lots of .onion sites contain very nasty things, and many of them are likely scams.
Facebook Onion Site
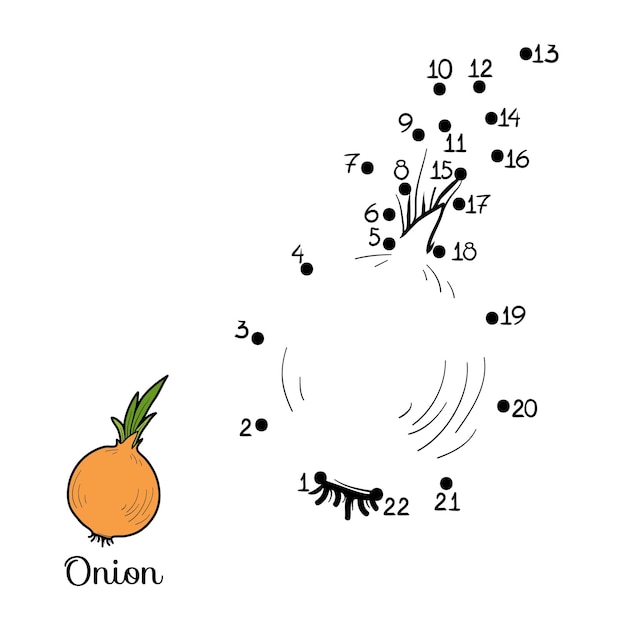
These layers upon layers give this network its iconic “onion” name—as the onion itself has layers upon layers. The Tor browser is the most preferred browser for surfing the dark web because it creates encrypted pathways for user traffic, ensuring all the activities are anonymous. However, please note this article is for research and educational purposes only. The dark net is full of notorious hackers, scammers, malware, and other viruses. We recommend using NordVPN and a robust antivirus like TotalAV to keep you safe while browsing the dark web. As a result, your dark web use may draw unwanted scrutiny from your ISP or law enforcement.
Onion Domains
This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session. Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. Also, you must log in or have a specific IP address or URL to access the deep web content. Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. Facebook’s dark web version allows users to access the site where it is banned or restricted.
If you’re looking for a completely anonymous, easy-to-use email service, ProtonMail is an excellent choice. Wasabi Wallet allows you to manage, sell, and buy cryptocurrency on the Dark Web. It charges a small fee for its services and provides reliable and anonymous transactions. ProPublica is a news outlet that has won the Pulitzer Prize and is a non-profit that works to highlight issues that can impact the public on a large scale. ProPublica joined the Dark Web to protect themselves and keep their journalists safe.
- Unlike many onion search engines and other listings, Real World Onion Sites doesn’t include links to the darker side of the dark web.
- As long as you are not looking for anything illegal in the real world, it’s perfectly legitimate to use the dark web to find whatever you need.
- The Tor Metrics is a good place to get more information about the Tor project.
- Some are so well-built that they appear trustworthy until it’s too late.
- Of course, bypassing paywalls is ethically questionable and may be illegal in some jurisdictions.
Does The Tor Project Run Any Onion Services?

The trade-off is fewer listings but higher confidence in the links it does provide. Users looking for a streamlined, no-frills directory with strong privacy protections will appreciate OnionDir. Still, they should combine it with other resources to cover a broader range of sites. Whistleblower platforms enable confidential document submission without compromising the identity of sources.
Should I Browse Things Like Facebook And Gmail From Tor?
For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy.
The Onion Service Protocol: Overview
Therefore, the whistleblower must take note of their random code name. To search for the onion URLs, you need access to a deep web search engine. If you’re new to the deep/dark web, DuckDuckGo’s onion link should be your first port of call. This parent site gives access to all other dark websites through a simple search.
The list includes news, media, literature, libraries, email, social networking, crypto, and more. Cross-check onion links with trusted directories like dark.fail or onion.live, and never follow a link blindly. With the right precautions, the Hidden Wiki in 2025 remains one of the most helpful tools for navigating the dark web — and yes, you’re in the right place.
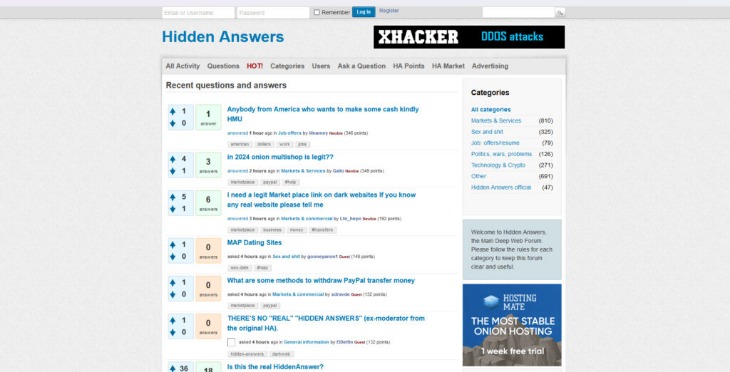
The website’s articles focus on digital rights, surveillance, and security research. I found their technical explanations clear and well-researched, though the site updates less frequently than other news platforms. Yes, governments can still monitor onion sites if they really want to. Local offices frequently monitor suspicious activities that involve their jurisdictions, so authorities might be closer to your anonymous communication than you know. Since most Tor websites are non-indexed and unregulated, the probability of scams is much greater on the dark web. Malicious actors can prey on unsuspecting users without leaving much of a digital footprint on Tor, so it’s often just a matter of time before you run into one.
Fortunately, you can’t just stumble onto dark web websites by accident. Stay private with a tool like Surfshark’s Alternative ID to mask your contact details and use generated data on sites you don’t trust. Given the above threats, it’s a good idea to use Tor over a VPN to access the dark web. Since the organization behind it is independent, it’s fully user-supported and relies on donations to keep its site up and running. All of this underscores Riseup’s prioritization of users’ rights over business interests.



