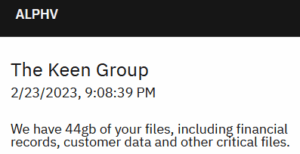
When your data is found on the dark web, it means that you’ve been compromised. Therefore, you need to start by changing your passwords, and you need to notify your credit card or bank provider. The most important thing is to ensure that you never click on links that you’re not sure of their source. Also, it should be common knowledge not to share personal information online. The fact that there are no real regulations as well as authorities to monitor transactions, you’re always on your own, and you’re a potential target and victim of a scam or fraud. Interestingly, the hackers don’t hide, but most of them even openly advertise what they offer on the darknet forums.
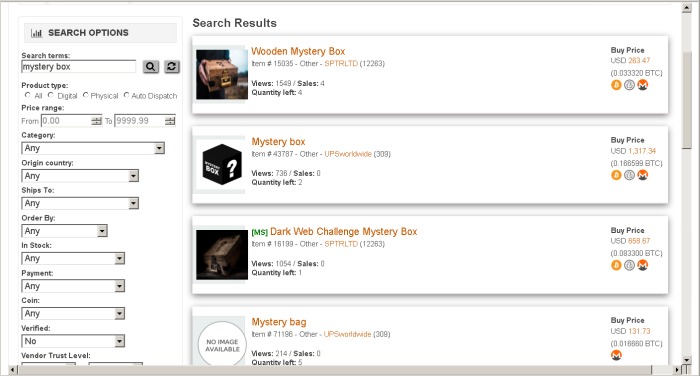
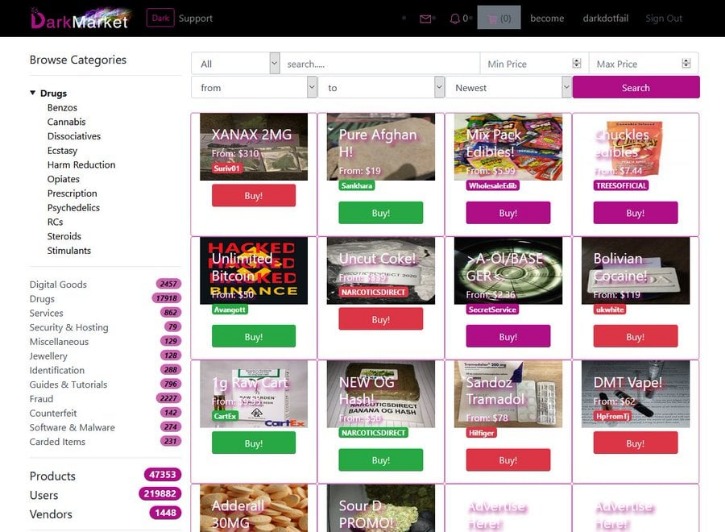
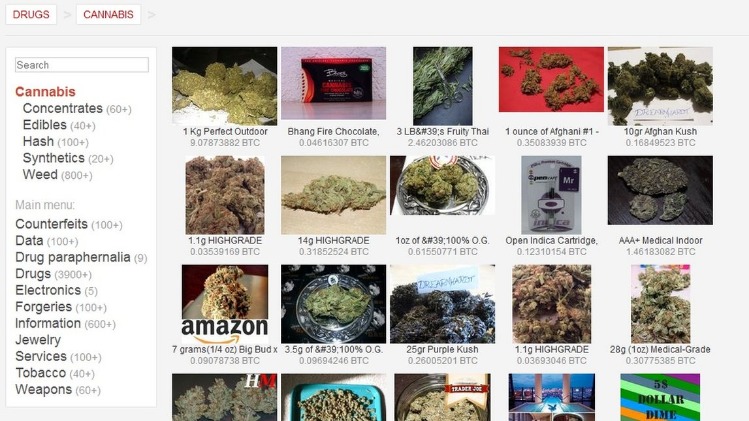
What You Can Buy On The Darknet Markets
Every investigation is led by a Cryptocurrency Tracing Certified Examiner (CTCE) and Certified Fraud Examiner (CFE). If you would like to discuss a potential investigation, please complete the form below. From at least mid-2012 through July 2017, Singh controlled at least eight distribution cells within the United States, including one in Columbus.
- Hence we do not distinguish multisellers by the number of markets in which they operate.
- Since the ISP can’t detect you’re accessing dark web URLs, it won’t trigger any alarms about your online activity.
- When we started, there were only a handful of markets to track and one review website – darkwebwebsites.org.
- Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria.
Darknet Markets
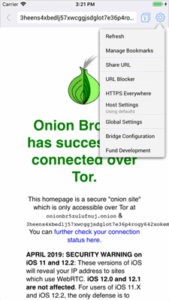
Accessing these markets requires the Tor network, which ensures anonymity by encrypting traffic through multiple layers. Cryptocurrency payments are the norm, with Bitcoin (BTC) and Monero (XMR) being the most popular options, Monero often favored for its privacy features. Examples include the sale of high-quality products with low risk for contamination (including lacing and cutting), vendor-tested products, sharing of trip reports, and online discussion of harm reduction practices. Darknet or dark web marketplaces are a hidden part of the internet that surface web users can’t access; they can only be accessed with special anonymity software called Tor. Many people (mostly criminals) use these sites to perform illegal transactions such as selling banned goods and services. Vortex Market stands out from other darknet markets due to its intuitive interface, which allows users to easily navigate through an extensive catalogue of goods and services.
Power Your Insights With Data You Can Trust
And, of course, think twice before sharing too much personal details online. Even the smallest details about you can be useful to cybercriminals. That all is for general internet activities, you can guess how crucial having a VPN is when you hop onto something like the dark web. They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk.

What Kind Of Content Is On The Dark Web?

Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day. Torch is funded primarily through advertising—purchased in BTC, of course—which is why you’ll find the front page blanketed with old-school banner ads of dubious origins. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. Search engines on the dark web are a bit of a contradiction because dark web sites by definition are not indexed by traditional search engines.
The Deep Web contains content that is not indexed by search engines, such as your personal email address, a brand’s gated pages or your online banking account. There’s no denying that the dark web is well-known for illegal activities. Besides, not everyone wants to purchase an illegal item – some want items anonymously. That’s exactly what happens when it comes to the dark web marketplaces.
What Are Darknet Markets? Complete Guide
The shift toward Monero as an alternative to Bitcoin is growing, offering enhanced privacy for transactions. Onion routing masks IP addresses, making it nearly impossible to link purchases to real-world identities. Markets now integrate self-destructing listings and time-locked payments, further minimizing exposure. Vendor reputations are transparent, with detailed feedback systems ensuring product quality matches descriptions. Bitcoin remains dominant, but privacy coins like Monero are gaining traction for their enhanced anonymity. Additionally, we analyse the U2U network of transactions, i.e., the transactions between pairs of market first-neighbors where the source and destination nodes are market users without the market as an intermediate.
Welcome To Abacus Market
So, what even is this dark web, and why are these marketplaces present there? Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. Law enforcement and security researchers recommend treating all darknet interactions as compromised by default.
The largest component of the S2S network of U2U transactions between sellers for each year with the respective number of nodes (N). The nodes are sellers that are active in that year, and an edge is placed between two sellers if at least one transaction occurs between them during that year. The network is mostly populated by U2U-only sellers, followed by market-only sellers. After a major external shock in 2017, the S2S network shrinks but, unlike the multiseller network, recovers, and grows again (though slower than the multibuyer network).
What Are Tor Markets?
Want to get illegal drugs, fake passports, Trojan, or other cyber attack software? Understandably, as in the case with most illicit trade markets, you don’t even need to verify your email Awazon. Following Silk Road’s closure, numerous competitors emerged, including Silk Road 2.0, Evolution, and Agora. This generation introduced improved security practices but suffered from increased instability, exit scams, and improved law enforcement techniques. Perico Market is a newer entrant to the darknet market scene, notable for focusing on strong privacy practices, Monero-only payments, and clean UI.
Some believe STYX is the OG darknet market when it comes to financial crimes. It trades in hacked bank accounts, stolen credit card information, and other services that facilitate cryptocurrency laundering. The popular Silk Road was the first dark web marketplace that you could only access via the Tor Browser. The darknet markets are a hotbed for selling stolen personal information. The stolen data can be just anything from full names, credit card details, passwords to social media accounts, bank account information, and social security details, among others.
For consistent access, users rely on updated darknet market lists, which filter out scams and highlight trusted vendors. In contrast to the other types of sellers, the median income of U2U-only sellers increases after operation Bayonet. Moreover, we observe a trend of increase in their median income relative to the value before operation Bayonet—an increase of almost six times by the end of the period of observation (see Supplementary Information S4).
The classification is performed in five steps (see Fig. 1), as detailed next. To reduce the presence of noise in the S2S network, we consider only stable U2U pairs, i.e., pairs that have at least three transactions throughout the whole period of observation13. The trading volume generated by stable pairs is more than five times larger than that of non-stable pairs13.