It’s not just a tech tale; it’s a saga of gutsy moves, big money, and the cat-and-mouse game with law enforcement that’s shaped the dark web we know in 2025. From Silk Road’s wild west days to today’s slick setups like Abacus, here’s how it all went down—raw, real, and straight from the shadows. Monero and Bitcoin are two of the most commonly used digital currencies on the dark web markets.
These are the primary sources of what the general public thinks of as “dark web.” Online marketplaces selling hacked credit cards, fake passports, malware kits, untraceable drugs, anything. Blockchain even has an HTTPS security certificate for even better protection. Unlike other search engines, it does not collect or share web activities and personal data of users. When using Tor for enhanced privacy and anonymity, it’s crucial to consider the security of your email communications. While popular email providers may be convenient, they often track user data, impose stringent monitoring, and may not be optimized for anonymous browsing. These services can potentially log your IP address or expose your information through various means, undermining the benefits Tor offers.
What Awaits The Users? Buyers In The Crosshairs!
Those who use these services can still be traced and prosecuted if caught, especially as law enforcement continues to sharpen its tracking tools. Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content. The markets often share materials related to child exploitation, pornography, and non-consensual recordings, all of which are serious crimes that inflict lasting harm on real-life victims. Such content fuels a dangerous cycle of abuse, violence, and exploitation. The site gives out free samples of the stolen data every now and then to gain more customers.
Illicit And Risky Use-Cases
Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals.
Criteria For Choosing The Best Dark-Web Marketplaces
These domain names are not registered with a central authority but are instead derived from cryptographic keys. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download. Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way. You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together.
Types Of Dark Web Sites (and What Really Goes On There)
A lot of vendors from all over the world are registered here, offering an extensive range of products, including digital services, security tools, and other equipment. For those who are looking for a reliable Alphabay Market alternative, Awazon Market aspires to become the solution. Of course, not all the popular and widely-used dark web sites and things like marketplaces on the dark net are illegal. Some use them due to privacy concerns, such as journalists talking to informants or whistleblowers, while others may simply want to protect their confidential information from observation or tracking. Nevertheless, most people on the internet do not need to communicate or venture into the dark web.
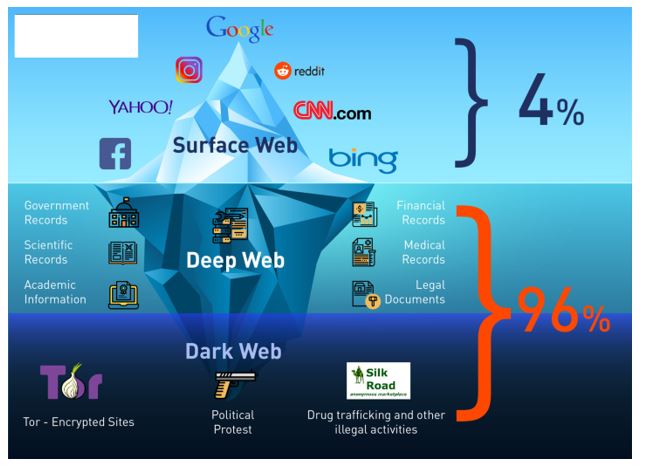
Introduction: How Much Of The Internet Can You See?
Ares market has emerged as one of the most sophisticated darknet marketplaces, combining advanced security features with an intuitive user experience. Unlike traditional e-commerce platforms, Ares operates exclusively through Tor hidden services, ensuring complete anonymity for all participants. In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere. You should be aware that law enforcement agencies may be monitoring the dark web and that visiting certain websites or engaging in illegal activities can result in criminal charges. You can also check out this ultimate dark web safety guide to browse safely. The digital underworld has witnessed a major blow with the recent dismantling of Archetyp Market, one of the longest-operating darknet drug markets.
- The anonymity and encryption provided in dark markets create a haven for cybercriminals and nation-state actors to buy and sell dangerous assets while evading detection.
- These digital currencies provide a degree of anonymity, as transactions are recorded on a public ledger but do not directly link users to their real-world identities.
- It is a good way to prevent third parties from tracking online activities.
- This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites.
- One of the biggest problems cybersecurity teams face isn’t a lack of tools — it’s too many alerts.
One of the most well-known technologies enabling darknets is the Tor network, which was developed by the U.S. Naval Research Laboratory in the mid-1990s and later released to the public. Tor, short for “The Onion Router,” routes internet traffic through a global network of volunteer-operated servers to anonymize a user’s online activity. This technology initially had noble intentions, aiming to protect activists, whistleblowers, and individuals in repressive regimes.

FAQ About European Darknet Markets

Other sites explicitly block search engines from identifying them. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messy, unregulated community with everything from freedom fighters to full-blown cybercriminals. With the onion browser, you can access ordinary HTTPS websites on the web. This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing.

- That ensures trust and safety for every user exploring Ares darknet products.
- Later in 2022, the US Naval Research Laboratory built on Freenet’s idea to create a secure and encrypted network for sensitive communications, which was later released to the public as open-source software.
- Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net.
- They engage in financial crime and sell other people’s stolen personal information, since they’re under the veil of anonymity.
- Whether you want some pharmaceutical products (drugs) or digital items, you will probably find the products here, and that too at affordable prices.
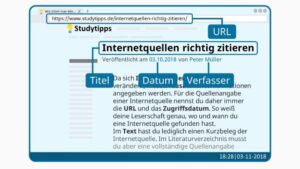
Also, you must log in or have a specific IP address or URL to access the deep web content. The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. The anonymity provided by onion routing comes at the cost of slowing your internet considerably.
Community Forum / Arche Wiki / Patch Notes / Team
Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. It’s, ironically, more conspicuous than using popular browsers and sites. The darknet, also known as the dark web, is a concealed section of the internet that’s inaccessible via standard search engines. You can only access it using special software, settings, or authorization. This area comprises websites and content that are purposely kept hidden from public view. Cryptocurrencies, while offering enhanced privacy, also present significant risks.
The dark web is a hidden section of the internet that you cannot reach with common search engines like Bing or Google. The only way in is through the use of special software that renders all users anonymous and untraceable. We will be exploring the top 10 Dark Web markets in this article. From items like drugs, fake ID cards, and hacked bank accounts to more complex offerings like human trafficking, these sites carry all the illegal activities you can think of. Discover everything about what a darknet market is, top marketplaces, security threats on them, and learn how to protect your data online. Dark markets continually adapt and evolve to stay ahead of law enforcement and security measures.
This just involves turning on your VPN before you open Tor and connect to dark web sites. Impreza Hosting is a service that helps you host a site on the Tor network. It provides an .onion URL and an interface for you to manage your Tor site easily. It also boasts that no personal information is required to use the service, and payment can be made with cryptocurrency. Accessing darknet requires using Tor Browser, a special web browser that routes your internet traffic through a global network of relays managed by volunteers. This way, it becomes very difficult to trace which websites you’re visiting, and these sites won’t know where you are located.
Payments were not made in euros or dollars, but with the anonymous cryptocurrency Monero, which is particularly difficult to trace. Designed for the elite darknet operator seeking streamlined access, surgical control and unmatched discretion. The seller does not make clear how they are obtaining these cards, but threat actors are known to clone cards, or access banking information from stole credentials, particularly through Stealer Logs. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. If you only want to mask your IP address and don’t need to access the dark web, then going online with a VPN is much easier and faster than using Tor. Activists, whistle blowers, and journalists also use the dark web to communicate securely with sources and news organizations.