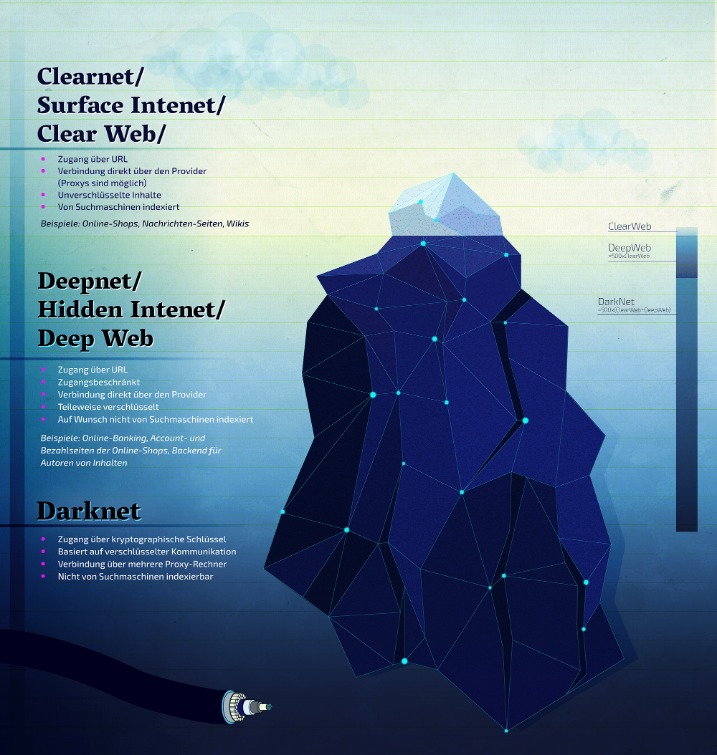
Since the Hidden Wiki can be a hotbed for scams, explain best practices for verifying links before visiting or interacting with them. Discuss how the Hidden Wiki servers are usually hidden, decentralized, and often hosted by volunteers or anonymous groups. Talk about challenges like uptime reliability, DDoS attacks, and frequent domain changes due to law enforcement or hacking threats.
Is Accessing The Dark Web Illegal?
Many free VPN providers lack basic security features and track your online activity, so they don’t offer much privacy. While the best dark web sites listed above are a good starting point for a safe, legal surfing experience on Tor, there really is no substitute for a VPN. SecureDrop has even been adopted by various news organizations worldwide. It provides a safe haven for anyone looking to shed light on wrongdoing or share critical information with the media.
The Hidden Wiki: A Comprehensive Guide To Dark Web Directories
When using the Tor network, avoid accessing your regular browser or any site that could link back to your real identity. Mixing these activities can jeopardize your anonymity and expose your personal information. In summary, the Tor Browser is your gateway to the darknet, providing a secure and anonymous way to explore and access resources that are otherwise hidden from the standard internet user. In addition to these tools, you need to exercise extreme caution when browsing on the dark web because there are tons of phishing and malicious sites on there.

Tor Hidden Wiki 2024
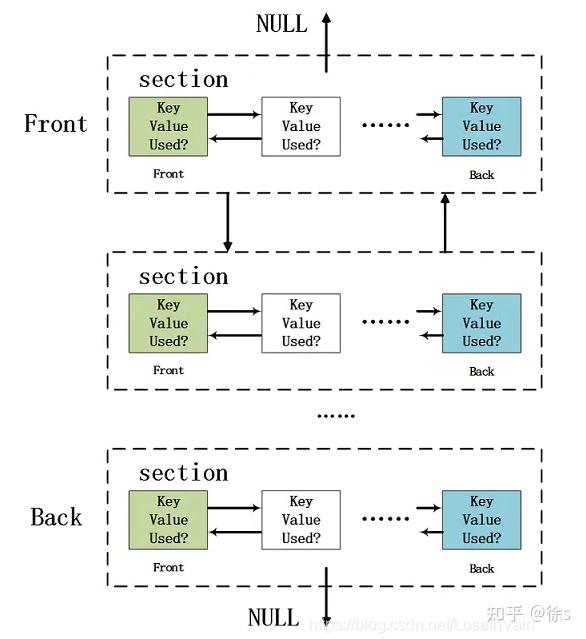
To counter takedowns, developers are turning to decentralized DNS systems like Handshake and InterPlanetary File System (IPFS). These tools remove reliance on central registrars and servers, allowing dark web sites to persist across mirror nodes even after a seizure. While adoption is early, the shift signals a long‑term move toward censorship‑resistant infrastructure.
- Avoid clicking on suspicious links, disable JavaScript where possible, and never share personal or financial information on dark web sites.
- The significance here lies in the potential damage to individuals and businesses.
- Financial fraud is common, and you have no recourse if transactions go wrong since these markets operate outside legal frameworks.
- Darknetlive contains articles about everything related to the dark web.
- While this may all sound sophisticated, it is a financial crime and very risky.
Transactions within dark markets predominantly involve cryptocurrencies like Bitcoin, Monero, or Ethereum. These digital currencies provide a degree of anonymity, as transactions are recorded on a public ledger but do not directly link users to their real-world identities. Just like on the regular internet, phishing is a big problem on the dark web as well. Fraudsters create fake versions of popular darknet sites to trick users into entering login details or personal data.
Can I Access The Hidden Wiki Without Tor?
The use of hidden wiki links became prevalent as it enabled users to navigate the vast and often treacherous waters of the dark web more efficiently. This evolution was significant, as it marked a move towards a more organized approach in finding reliable resources. Always remember to use a VPN in conjunction with the Tor browser for an additional layer of privacy.
Surprisingly, most guns on the darknet actually start as legal products. The UNODC (United Nations Office on Drugs and Crime) maintains that almost all firearms are originally manufactured through legal means. One notable fact is that the site has changed its domain twice since its formation. Today, Exodus Marketplace works from 3 different domains, two of which are its mirrors. While pluggable transports can assist in bypassing censorship, they may also make you more identifiable.
Use HTTPS Whenever Possible
But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship. You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on. Before clicking any of the dark web links below, you’ll need to get the Tor Browser (also called the Onion Browser) or another service that provides dark web access, such as the Brave browser. Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material.
Tips To Stay Safe When Using The Dark Web
It delivers an uncensored search experience, granting users access to a diverse array of information while effectively excluding illegal content. With NordVPN’s double VPN feature, your traffic is routed through two servers for double encryption. It also includes a dark web monitoring feature that crawls the dark web and alerts you if your details show up anywhere.
Privacy Advantages Of The Hidden Wiki
Tor Browser aims to make all users look the same, making it difficult for you to be fingerprinted based on your browser and device information. If you find a link that is not working let us know on our contact page. If the website you are trying to visit has Neutral mark it means we could not verify if this website is a legit or a scam one, since it has mixed reviews. If the website you are trying to visit has Recommended mark it means it has been verified and is safe to use. Enable MFA wherever possible to protect your accounts from unauthorized access. ZeroBin encrypts any text pasted into it, and its own servers don’t even know what you pasted.
First, check out our beginner’s guide on how to use Tor, then come back when you’re ready to get started. Even completing a transaction is no guarantee that the goods will arrive. Many need to cross international borders, and customs officials are cracking down on suspicious packages. The dark web news site Deep.Dot.Web teems with stories of buyers who have been arrested or jailed for attempted purchases. A study, Into the Web of Profit, conducted by Dr. Michael McGuires at the University of Surrey, shows that things have become worse.
- To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network.
- Additional marketplaces like AlphaBay and Hansa flourished and fell, hybridizing with escrow services, online reviews, and encrypted communication to create a more intricate system.
- Whether you want some pharmaceutical products (drugs) or digital items, you will probably find the products here, and that too at affordable prices.
- This technology makes it very difficult to track the identity or location of users.
The anonymous group behind Tunnels alleged that the materials were produced while exploring the forbidden tunnels, built underneath some of the most prestigious American Universities. No info is available on the explored institutions or how these sections can be accessed. I think it’s safe to say that these are unsanctioned exploits, all the more reason to boast them on the dark web.
Users slip into this shadowy realm using a anonymizing browser, like Tor (The Onion Ring) browser, and a Virtual Private Network (VPN) to protect their identity and secure their connection. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. It is easily accessible by the general public and requires no special configuration.