The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe.
What A Real ID Is And What It’s Not
- Synthetic IDs are one of the fastest-growing tools for identity theft, used for laundering money, terrorist financing, or grand-scale theft.
- These range from dark web vendors to encrypted Telegram and Signal channels.
- Modern fraud detection systems go beyond Optical Character Recognition (OCR) to evaluate subtle visual features that can reveal image manipulation.
- Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user.
High-quality laminates will remain intact, while non-professional or low-quality laminates may bubble under this stress. Additionally, authentic IDs will have smooth edges, while counterfeit ones may feel sharp or uneven. The Gullah Society is dedicated to preserving and celebrating the rich cultural heritage of the Gullah people.
FBI reports indicate that 65% of major financial fraud cases in 2023 involved fake identification documents at some stage. For businesses verifying identities digitally, it’s crucial to have a robust system capable of catching these sophisticated AI-generated fakes. ID verification solutions must incorporate advanced algorithms, real-time data analysis, and multi-step verification processes to ensure that identities are legitimate. More concerning than the fake ID-generator itself was the talk in the Telegram thread of fake identities for sale. These identities would allow fraudsters to create fake IDs using real personal information such as name, address, and date of birth.
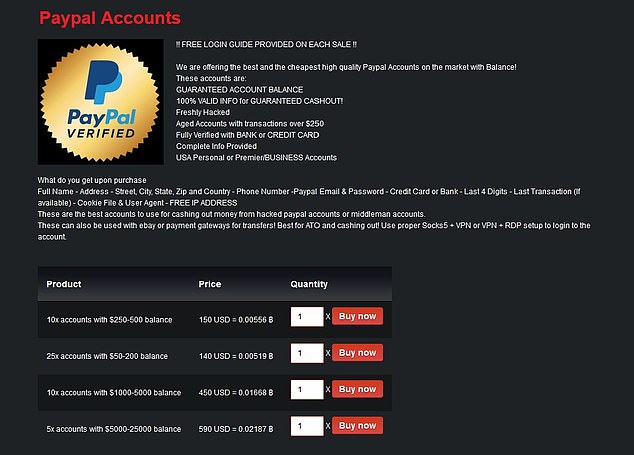
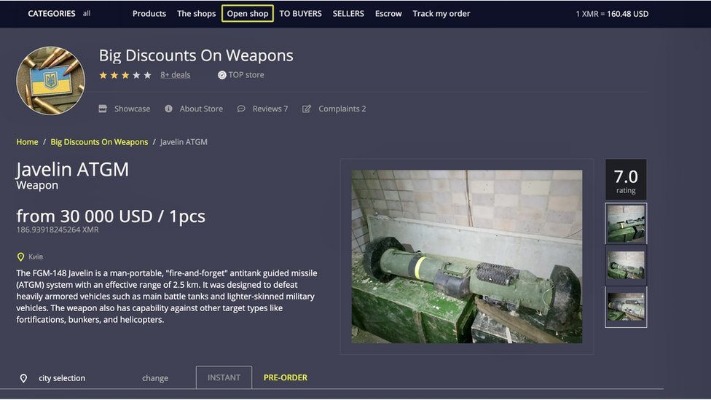
Mega Market

These are the primary sources of what the general public thinks of as “dark web.” Online marketplaces selling hacked credit cards, fake passports, malware kits, untraceable drugs, anything. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. Its .onion site provides an additional layer of privacy and security for users accessing their Bitcoin wallets or exploring transaction data, especially useful in regions where cryptocurrency sites might be monitored or blocked.
StartPage – User-Friendly Dark Web Search Engine Like Google
Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion. Another website is Dread, which is often called the “Reddit of the Dark Web.” It’s a community platform where users can discuss new markets, share onion links, add reviews, and much more. Hence, if you participate in them, whether knowingly or unknowingly, you can end up putting criminal charges on yourself, and in some extreme cases, even imprisonment. Unlike other search engines, it does not collect or share web activities and personal data of users. The payoff values in the scenario of using a fake ID illustrate the dynamics of rational decision-making under peer pressure. Hypothetically, using reasonable gain/loss values, if the student successfully uses the ID, they gain social rewards (+3) while the bouncer avoids trouble and might receive a tip (+2).
Editing Real IDs
Official IDs incorporate holographic images that become visible when exposed to light, serving as a critical security feature. These holograms vary by state, making it essential to know the specific design for your ID. For example, Illinois driver’s licenses display the state name diagonally across the front when tilted under light. In 2026, local police, federal agencies, and even international bodies are collaborating to maintain shared databases of seized fake IDs. This cooperative approach helps track large-scale operations and prevent repeat offenders from exploiting weak systems.
Back Side Security Elements
While not all of the documents were created using AI, the case highlights how digital identity fraud can be used to access sensitive systems. Similar tactics may soon become accessible to less sophisticated actors as these tools spread more widely. When fake ID users infiltrate your business, the ripples can become tsunamis. From financial losses to reputational damage and regulatory penalties, the risks are far-reaching. The solution lies in tightening up fraud detection measures and prioritizing robust age verification processes that protect not just your business but your brand’s future.
Fake ID Statistics 2025: A Wake-Up Call For Age-Restricted Sellers
The scale of this fraud, achieved without AI, highlights just how much damage can be done when these tactics are automated. AI-generated fake IDs are created using image generation systems trained to replicate the structure and visual details of official documents. These models are often trained on large datasets of ID images—some pulled from public sources, others leaked or scraped from compromised platforms. Over time, they learn to mimic design elements like background textures, text alignment, official seals, and machine-readable zones.
Global Access Through Encrypted Marketplaces
Every jurisdiction and document type (and many jurisdictions have 20+ valid document types in circulation at any given time) has different expected fields. When we scan an ID using our AI algorithms we instantly check to make sure the data is in the format we expect it to be. We then compare that data against the plaintext data on the front of the document.
Criminals Avoiding Law Enforcement
Before shipping away a fake ID, we put it through the ringer and make sure it holds up to scrutiny. In some states like Illinois and New York, mere possession of a fake ID can result in felony charges, while in others like Texas and Ohio, first-time offenses are typically treated as misdemeanors with limited consequences. Want to spice up a costume, pull a prank, or use it for a creative project?

Furthermore, data will help to detect attacks against the network and possible censorship events. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics.
- It is one of the most active and up to date markets and always provides new and updated malware and data.
- The landscape of identity verification is rapidly evolving, with new technologies and regulations reshaping how businesses and consumers interact.
- The scale of this fraud, achieved without AI, highlights just how much damage can be done when these tactics are automated.
- Surfshark supports unlimited simultaneous connections to protect as many devices as possible.
- At once, they are protecting their customers, revenues, and brand reputation against the risk of fraud from individuals or organized criminal networks.
Quick Links
All our print and online content always has been and always will be FREE OF CHARGE. Whether it’s local news in Spain, UK news or international stories, we are proud to be the voice for the expat communities who now call Spain home. With up to 100,000 identity documents now circulating, vigilance is key – from guests monitoring their finances to hotels tightening their tech. Authorities say the investigation is active and more impacted properties may be named in the days ahead. AgID detected ‘illegal sales activity’ offering the trove, with listings priced from about €800 up to €10,000, according to Corriere della Sera.
The operation led to the discovery of 43 fake IDs, involving 15 international students from the University of Toronto and Ryerson University. This batch of fake IDs was the first to pass through Canada’s bank-grade iris verification system, a technological breakthrough that had outpaced conventional law enforcement detection equipment. AI-generated fake ID images are made to look good, but they usually don’t have a sophisticated understanding of barcode data (or MRZ) formatting.