This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites. It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web.
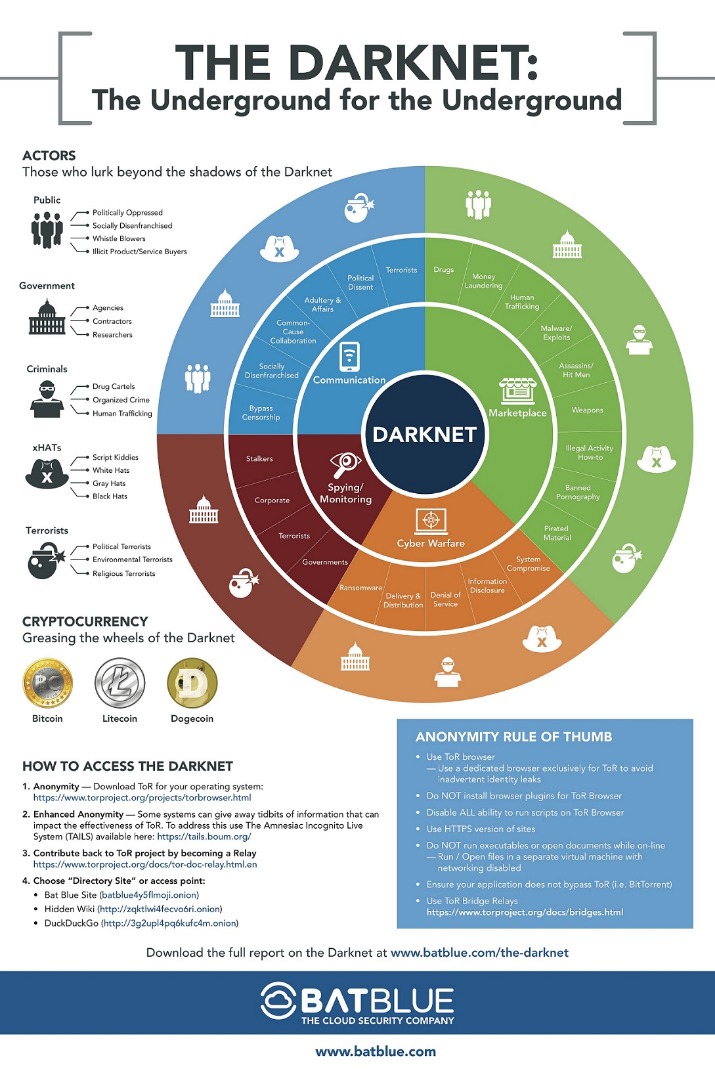
Privacy and anonymity are the dark web’s hallmarks, thanks to a network of servers that hide users’ identities and locations. If you’ve ever checked your medical results online through a portal that required a login, you were navigating the deep web. It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security.
Can Search Engines Find Everything On The Dark Web?
To stay safe and private when visiting any listed sites, ensure you have a VPN and anti-malware installed and enabled. The platform utilizes end-to-end encryption, ensuring it does not store any activity records. Like other email clients on the dark web, it does not require you to give your personal information. It is a Swiss-based company (privacy-friendly country), and all its tools are open-source, meaning anyone can test its vulnerabilities.
Popular Dark Web Marketplaces Of Today – Detailed List
The deep web is the part of the internet you can’t access through search engines like Google and Bing. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. It contains 7,500 terabytes of information, compared with only 19 terabytes of information in the “surface” web. To look at it in a different way, it makes up between 90% and 95% of the internet.
Using Escrow And Trusted Mediators Where Possible
These concerns are valid because using Facebook undoubtedly exposes users to some of the highest levels of surveillance capitalism anywhere on the web. This is a news resource about Tor that is hosted by its developers at the Tor Project. Julian Assange may have lost much of the goodwill he once enjoyed, but WikiLeaks remains one of the most important sources of uncensored political information. Although you can access its content in any browser, for security reasons the only way to submit documents is through Tor. Calling itself “an info beam in the Dark Web”, Flashlight gathers news about cryptocurrency, Tor-related projects and internet privacy in general, presenting it as a constantly updated feed.
Beacon Cybersecurity Newsletter
- DrugHub is an XMR-only, security- and privacy-focused marketplace that offers a unique .onion access system, private mirrors for all vendors, and excellent uptime.
- Most people start by using the Tor Browser, which hides your IP address.
- Over the years, they added many additional privacy features, such as “Anonymous View” for added protection.
- Dark web forums are very similar to their clear web counterparts in almost every way, except for the content they discuss.
- For 2025, they’re teasing AI-powered search—could make digging through listings a breeze, which I’m hyped for since their catalog’s already hefty.
- However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired.
Technically, yes, but you’ll still need to use the Tor network to access .onion sites, even on Chrome or Firefox. Chrome offers proxies that can give you access to dark sites, while you need to change the configuration of Firefox to do so. However, these methods can compromise your online security and would be very slow, so it’s better to just use Tor. Similar to Facebook, X (formerly Twitter) also offers a Dark site if you want to access the platform using Tor.
Run Antivirus/Anti-Malware Software
We strongly recommend shielding yourself with a VPN before you access the dark web. The notion that the Tor browser provides failsafe anonymity is false; you need to protect yourself. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products.
Should I Use A VPN To Access Tor?
Word’s out they’re going decentralized in 2025—less downtime, more trust, right in line with where things are headed. The site’s slick—vendor stats update live, checkout’s a breeze, and the vibe’s modern without being over-the-top. I’ve used it a handful of times; deliveries landed smooth via DeadDrops—plain packaging, no fuss. It’s not the biggest player like Abacus, but it’s got a loyal crew and uptime that rarely blinks.
SecureDrop protects your privacy by encrypting your data, which makes it unreadable. Also, it doesn’t log your IP address or any information about your browser or device. Moreoever, the servers are owned by the organizations that use the service. The best news is Torch updates its sites every single day, so you’ll always be able to browse the latest news and access new services and sites.

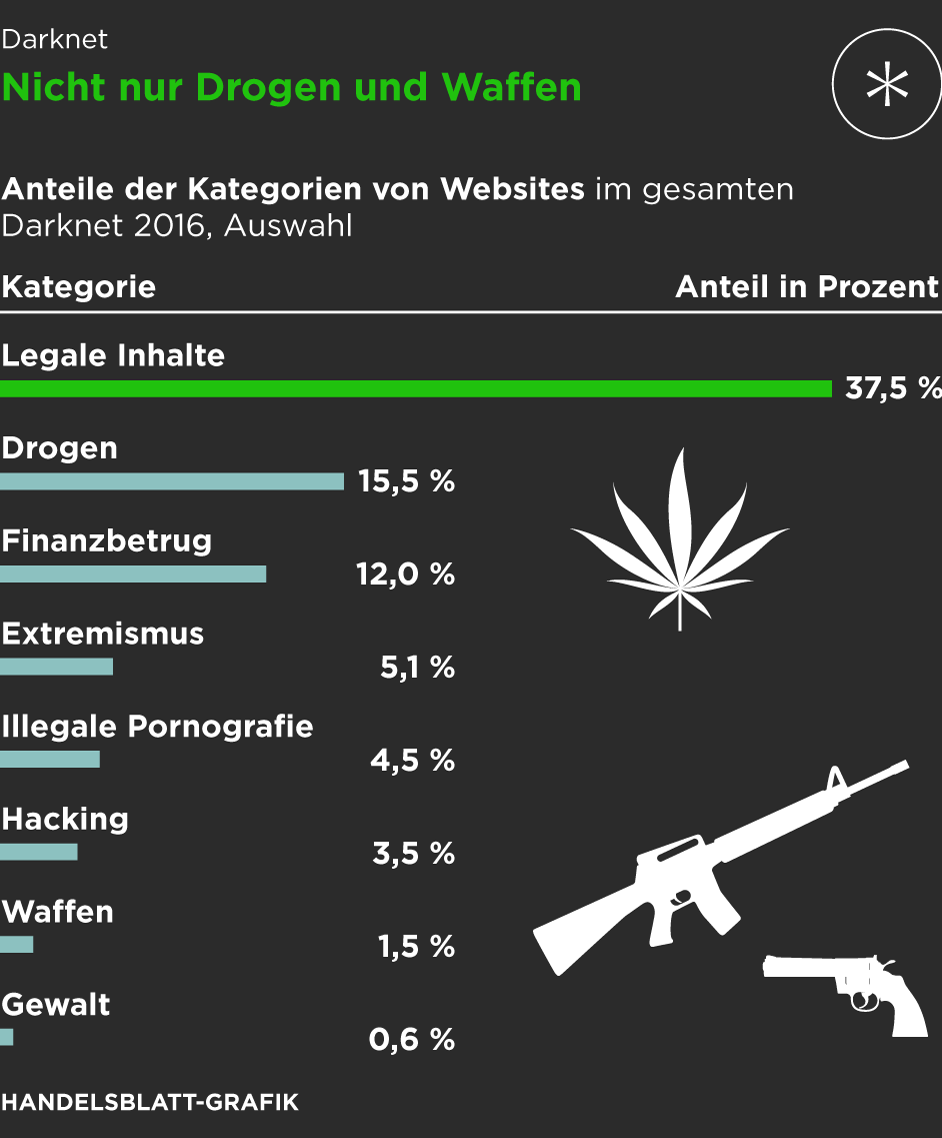
In addition, it is worth noting that users should not blindly trust links on the Hidden Wiki because this is a community resource that anybody can update, and some of the links are malicious. As a result, it is probably a good idea to double-check and verify any onion links you find using a secondary source such as Onion Links or DarkWebPug. You need to invest in cryptocurrency to buy and sell through hidden sites, and Bitcoin is by far the most popular option. As we’ve mentioned, DuckDuckGo is Tor’s default search engine but it’s also worth bookmarking its ‘.onion’ site, if only to see that the Dark Web hasn’t wiped the smile from the happy logo’s bill. Indeed, the privacy-loving bird thrives on the freedom and anonymity offered by the browser, letting you quickly search the web without being spied on.
It uses the CoinJoin process, allowing you to mix your coins with other strangers making the transactions very difficult to track. That said, if ProtonMail doesn’t suit your needs, there are other Dark Web email platforms available, such as RiseUp and Mail2Tor. For example, RiseUp is an invite-only platform, meaning that you will need an invitation to use it. Beyond its directory functions, the platform also serves as a community hub where you can discuss various topics and share your experiences. Its longevity and reputation have solidified its position as a cornerstone of the Dark Web community. Founded in 1998 as Ixquick.com, we later changed the name to Startpage.com.
OnionName — Buy Readable Onion Domains
This layer of security ensures that users can freely express themselves and seek information on sensitive or controversial topics without the risk of reprisal or surveillance. The anonymity offered by Hidden Answers fosters a community where open, honest dialogue can flourish, covering subjects that might be taboo or heavily moderated on conventional platforms. The buyers, or “consumers,” are cybercriminals who use these tools to launch illegal activities. The victims, who are common users, businesses, and even banks, who end up paying the price. From there, these products are then passed on to distributors, which are the dark web marketplaces in this context.