
Also note that, simply “browsing” the dark web can’t necessarily land you in jail, as long as you don’t buy or sell anything which is legally controlled. Another legal use of the Deep web are sites like ProPublica, which are anonymous whistle blowing sites which anyone can use to share exposing documents or truths about powerful people or agencies. You also need to know that more than half the sites and sellers on the Dark web can’t be trusted, and are just scammers. That’s so because it’s already an illegal arena, so you can’t exactly go to the authorities about it.
- Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together.
- You also need to know that more than half the sites and sellers on the Dark web can’t be trusted, and are just scammers.
- Malicious actors and government agencies can run Tor nodes, compromising privacy and security.
- The dark web is full of unknown and potentially dangerous content.
- Experienced blogger with a strong focus on technology, currently advancing towards a career in IT Security Analysis.
This article aims to clarify these concepts, explore their differences, and highlight their respective purposes and risks. These hidden networks intentionally conceal IP addresses and encrypt communications through multiple layers of routing. Understanding the relationship between Tor and the dark web is essential—Tor (The Onion Router) is the primary software used to access these hidden sites. This is akin to the things you actively hide from other people and don’t want anyone else to learn about.
All Shades Of Internet Security
Most of our usage of the “private” internet is through authenticated portions of the deep web. Security solutions like anti-virus software protect your system and network from malware and other threats. The dark web, being a hub for criminal activities like identity theft and malware distribution, exposes you to various security threats like malware or phishing. You will never know when you stumble upon illegal materials, inadvertently download malicious software, or expose yourself to identity theft.
- That is why getting links from other pages is a basic principle of search engine optimization (SEO).
- This allows people to access important information and services regardless of their location.
- You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom.
- SecureDrop is a site that protects the privacy of journalists and whistleblowers.
- People use it to share information when their local governments act hostile or snoop extensively.
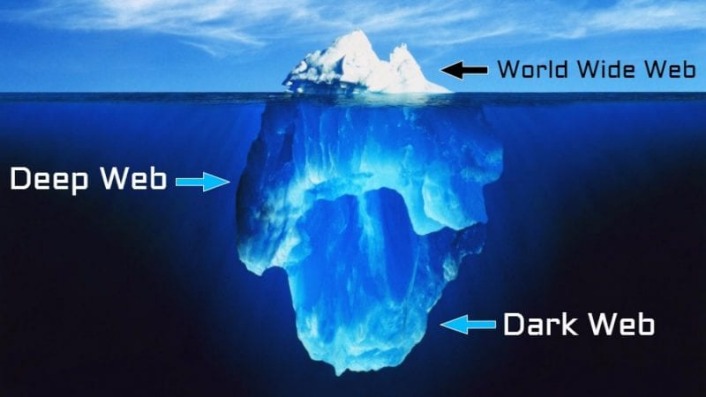
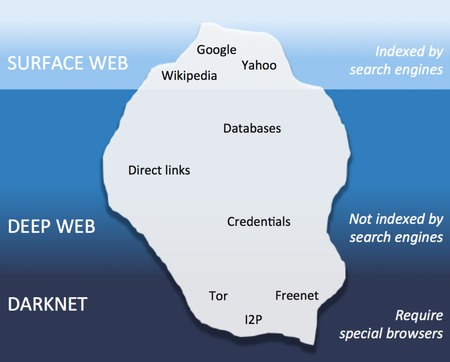
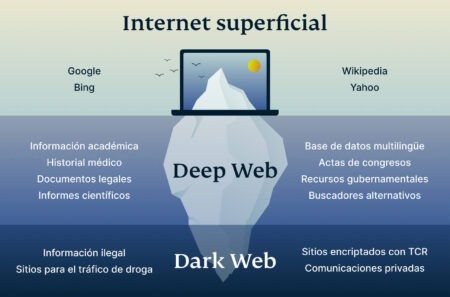
You’re only scratching the surface when you use the Internet for daily activities—reading news, managing finances, running businesses. Search engines like Google, Bing, and Yahoo can access just about 4% of the web. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Learn effective strategies for conducting threat hunting in your organization. The dark web’s layered encryption and routing methods make it extremely difficult for security teams to identify who is behind malicious activities. Discover the key differences between the Dark Web and Deep Web, their uses and risks to businesses.
Data Link Layer
As a deep web subsection, the dark web shares many characteristics. However, noteworthy differences exist in operation, scope, size, access methodology, applications, and security. However, maintaining security procedures is critical even though these websites are legitimate. Using threat intelligence platforms to analyze the threat data gathered from the dark web also enables organizations to defend themselves against attacks more effectively. It is worth noting that some pages on the deep web contain valuable personal data to cybercriminals. Securing this data prevents it from being compromised and possibly showing up for sale on the dark web.
This part of the Internet is available to everyone without the need for special tools. Although most people use the Tor browser to access the dark web, it can also be used free of charge to gain privacy while surfing the normal indexed web (clear web/surface web). The benefit of using Tor to surf the regular internet is that your activities will be private. Thanks to a strong layer of encryption, your ISP cannot know which websites you’re visiting. The dark web is a layer of the internet where users can fully mask their IP addresses in order to anonymously access or share certain content. The anonymity provided by the dark web does indeed make it ideal for people looking to engage in illicit activity.
Furthermore, data will help to detect attacks against the network and possible censorship events. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem.
What Is The Dark Web & How To Access It Safely In 2025
There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. There are several programs that hackers frequently use on the dark web. But remember, it’s essential to take all the necessary and important security steps before entering such sites on the dark web. As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor. From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information.
What Types Of Content Exist On The Deep Web?
Crimes range from data theft and selling illegal goods for cryptocurrencies to human trafficking and more severe offenses. On the Internet, these public spaces are known as the surface web. They are Web pages, Web applications, and other online elements that search bots — digital analogues of cartographers’ cameras — can index. Anyone can find them using a search engine and view them without paying, registering, or installing special software. You can conduct discussions about current events anonymously on Intel Exchange.
Sure, you can use other cryptocurrencies if Bitcoin’s not your cup of tea. Well, VPN over Tor is basically its opposite – instead of going through the VPN first, the signal passes through the Tor network, before going through the VPN. Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination. Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny.
How Can I Safely Access The Dark Web?
Locating surface web websites is possible because search engines can index the web via visible links (a process called “crawling” due to the search engine traveling the web like a spider). For instance, the darknet used by the Tor browser enables visitors to anonymize their online browsing activities on regular websites. While the content on the dark web has the potential to be more dangerous, this content is usually walled off from regular users. However, it is entirely possible for regular users to accidentally come across harmful content while browsing the deep web, which is much more easily accessible.
The Dark Web Provides More Layers Of Encryption
You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous. Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable. Despite its relatively high profile, the dark web makes up a vanishingly small portion of the World Wide Web, perhaps less than 0.01 percent. This information can be used to target ads and monitor your internet usage.
Surface Web Vs Deep Web Vs Dark Web Vs Darknet
Privacy, which is usually provided by encryption, is another benefit of the deep web. Encryption on the deep web allows fee for service sites to keep their content away from nonpaying Internet users while serving it to their customers. The encryption of databases is absolutely necessary for all forms of fintech to function properly.
It allows you to search for images, maps, files, videos, social media posts, and more. The website is available on the surface web and has a .onion site. This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. It is an excellent option if you want to surf the web anonymously. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions.
Is Tor Illegal To Use?
As discussed above, user profiles on the deep web are home to valuable personal data to criminals. It is important to use strong, unique credentials for every account. This illegally-obtained data can allow malicious actors to gain access to confidential data, use stolen credit card numbers, and even bring down the entire remote infrastructure of an enterprise. Intranets, or internal networks used by companies and academic institutions, cannot be accessed by the public. They require access to a specific VPN service and credentials before they can be viewed.


