
Amy and her husband Stephen Allwine – an IT specialist and a deacon at a local church – met with officers who informed them that someone had paid at least $6,000 on the dark web to murder Amy. The Allwines said they had no idea of who could be hiding behind the Dogdaygod persona. He was eager to kill a woman living in Cottage Grove, Minnesota. Evidence of the first murder linked to Besa Mafia emerged shortly after Monteiro met up with two police officers and seven months after Besa Mafia’s takedown. Monteiro gleefully bombarded Yura with questions, punching holes in the site’s business model, security and technical makeup.
Use A Dedicated Browsing Machine
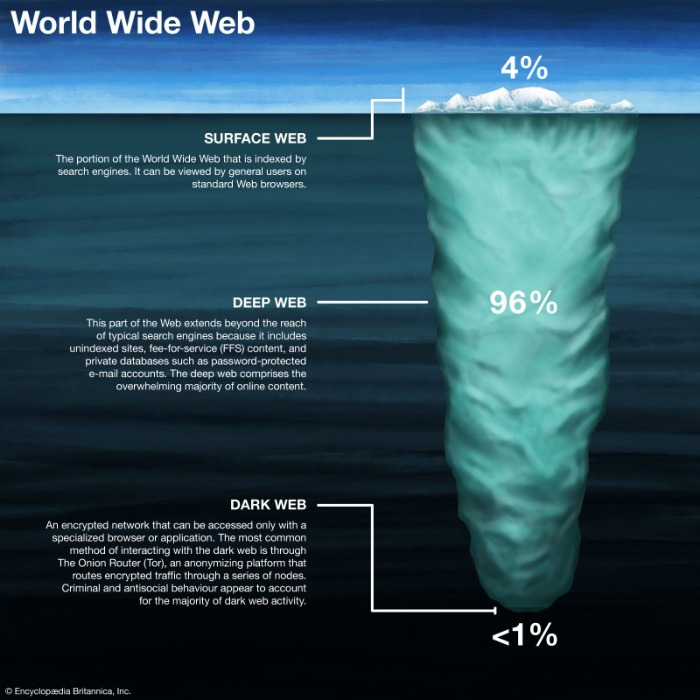
The U.S. Army developed “onion routing” to protect intelligence communications online. In 2002 the dark web began to grow significantly when researchers backed by the U.S. The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe. Journalists in overly restrictive countries also appreciate the anonymity of the dark web. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. That means that only 0.024% of all the known pages are findable in Google’s search engine.
The Justice Department did not disclose how it became aware of Felkins’ actions. Tor Search engine used to search for popular .onion sites that advertise many known scams. He said she helped him in his planned Appalachian Trail hike by making reservations at known hostels and other rest points and took care of his vehicle for him in his absence. Following the incident, she began receiving unpleasant untraceable phone calls from someone using an electronic device to disguise a voice, court documents said. “Sasser responded to this news by stating, ‘I hope you both fall off a cliff and die,’” court documents said.
As a result, the trading of illegal goods online has become more commonplace, and vast dark web marketplaces have been created. Using NordVPN or even ExpressVPN or PIA seems to be beneficial for many users. Such providers offer strong encryption and don’t store logs, ensuring all online footsteps are completely masked. Above all, it’s vital to go on the dark web carefully and sensically. You need a special browser (Tor) and all of these websites are intentionally obscured. So, to clarify again, this tutorial will cover how to access the dark web privately and safely – not the deep web.

“48 Hours” Disrupts Alleged Dark Web Hitmen In Potential Murder-for-hire Plots
This just involves turning on your VPN before you open Tor and connect to dark web sites. While technically not an onion site, we’re including Sci-Hub (sci-hub.se) as an interesting example of a site you can access via Tor. Sci-Hub gives access to millions of scientific papers, mostly ones from behind paywalls.
They branded themselves as a branch of the mafia, and promised murder for sale, at the click of a button. Yes, but you need to take some precautions to avoid cyber threats. In addition to the Tor browser, you should use an antivirus program (like Norton 360) to protect your device from malware infections, and a VPN (like ExpressVPN) to secure your IP address and traffic. Also, only use .onion links from legitimate sources like The Hidden Wiki. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy.

Social Media And Forums
A random dark web link can lead you to malicious software, phishing sites, and illegal content. Since most Tor websites are non-indexed and unregulated, the probability of scams is much greater on the dark web. Malicious actors can prey on unsuspecting users without leaving much of a digital footprint on Tor, so it’s often just a matter of time before you run into one.
- In opennet mode, the network will automatically assign you to other users on Freenet’s network.
- The deep web provides the perfect platform for these hitmen to remain anonymous and evade law enforcement.
- Navigating the dark web is like starting an epic quest — it’s dangerous to go alone.
- As enticing as it might be, don’t follow links to other parts of the dark web.
- For example, Facebook maintains an official Tor hidden services address at “facebookwkhpilnemxj7asaniu7vnjjbiltxjqhye3mhbshg7kx5tfyd.onion”.
New Bitcoin Purchases By The US Government Still On The Table, Bessent Says
This allows you to access Facebook through Tor, and your connection doesn’t ever leave Tor where it can be snooped on. This may be useful in countries that block Facebook, for example. Monitoring the dark web for information that can be used to target your business helps get ahead of threats.
Included in that dump were alleged lists of “hitmen,” photos of targets customers had uploaded, orders made on the site, and a large cache of messages purportedly between users and site admins. A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity. Many news publications, like the ones listed above, have a SecureDrop on their .onion sites. No, it is illegal to hire a hitman, regardless of where you do it. If you come across any listings for hitmen on the dark web, you should report them to law enforcement immediately.

External Links
Wasabi Wallet is a Bitcoin wallet that not only hides all your data in the Tor network but also allows you to “join” your transactions with others to increase your anonymity. This makes it incredibly difficult to find out who you are paying. Not Evil is a reflection of what the community is looking for and what the community reports as abusive or inappropriate content.
The Unbelievable Tale Of A Fake Hitman, A Kill List, A Darknet Vigilante And A Murder
The users only have access to a fraction of the available data and web pages. Data breaches like the ones mentioned above highlight the significant threats posed by dark web black markets. Stolen data can quickly transition from legitimate systems to underground forums, where it becomes a valuable commodity for cybercriminals. To counter these risks, organizations need robust, proactive solutions that go beyond traditional cybersecurity measures.
When the first hit-man sites were discovered, an oft-repeated assumption was that the dark web was crawling with legitimate assassins waiting to kill on command. But is this terrifying narrative grounded in reality, or is it simply a sensational myth amplified by pop culture and Internet folklore? In this article, we dig into the chilling rumors, the real facts, and what these myths reveal about our relationship with anonymity, crime, and the darker corners of the Internet. We may earn a commission when you buy through links on our sites.©2025 GIZMODO USA LLC.
People have been organizing illicit trades via the Internet since the 1970s. Those early examples, though, were through closed networks, and the actual exchanges of money and goods generally had to take place in person. With the advent of crypto-currencies, it became not only possible to complete trades online without leaving a money trail but easy.
What Are Onion Sites?
I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution. An easy way to find content on the dark web is to receive a link from someone who already knows about it. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy.
It isn’t only the (sometimes only implicit) anonymity provided by the Internet that potentially makes hiring a contract killer online more attractive than doing so face-to-face. Never provide personal or financial information unless you’re certain of the legitimacy of the website or seller. Trust your instincts, and if something feels off, it’s better to be safe than sorry. Remember, on the Deep Web, trust is hard to come by, so always proceed with caution. Make sure to prioritize encryption and secure communication when navigating the Deep Web to protect your sensitive information and maintain your privacy.



