
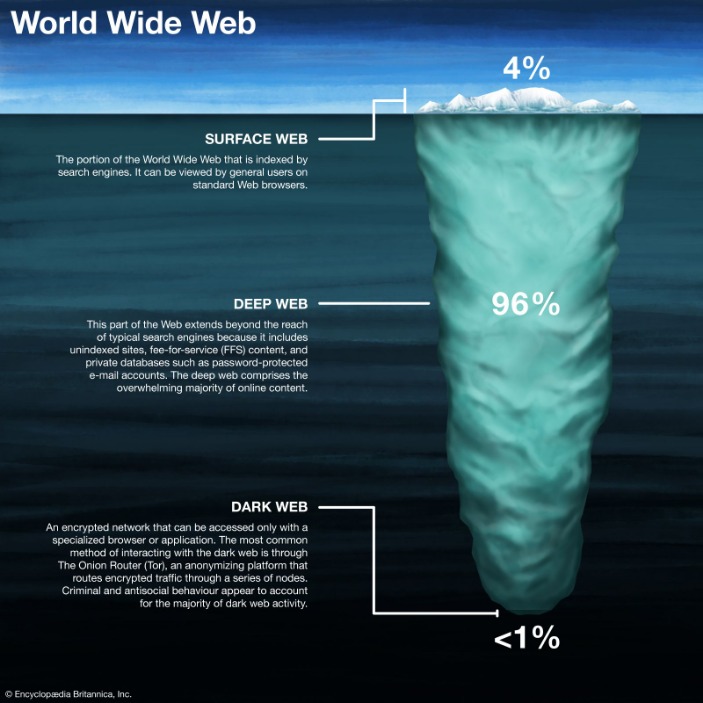
The dark web is a portion of the Internet that is inaccessible to normal search engines. To help you make educated choices about cybersecurity to keep you (and your data) safe and secure, by providing detailed, accurate, and practical information based on thorough testing. KeyBase combines encrypted messaging with secure file sharing and identity verification. Its dark web version provides the same functionality as the clear web option, while adding Tor’s anonymity layer. You can use the Tor Browser app on Android devices to access dark web links safely.
Bitcoin – New Links (
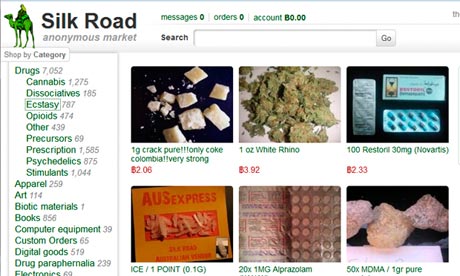
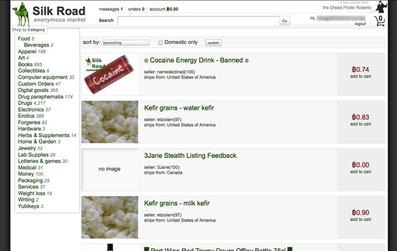
Major news outlets like The New York Times, The Economist, and The Guardian host SecureDrop instances on the dark web to give sources a safe, anonymous way to share sensitive information. Versus Market sets itself apart by prioritizing customer happiness and user experience. Versus Market provides services, including instant messaging, dispute settlement, and intuitive navigation, in an effort to make buying and selling transactions easier for its consumers. To accommodate a wide range of tastes and needs, the market provides a large selection of stimulants, prescription drugs, and opioids.
- If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites.
- In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market.
- Thankfully, you don’t need to use your official name or email; just use a fake username (we tested it successfully).
- Others are looking for stolen data, hacking services, or even banned books and political content.
- You can also check out this ultimate dark web safety guide to browse safely.
- However, not Evil is not a repository for illegal services and illegal material.
Legitimate Reasons Why People Use The Dark Web
Either way, it can be extremely risky for anyone to attempt to purchase controlled substances or unapproved drugs from the internet. Most dark web links are hosted on “.onion” domains due to the sensitive nature of the businesses or services they host. Tor websites may provide secure access to cryptocurrency wallets and anonymous email clients, and they’re also used to access black market sites.
Why Brand Monitoring And Threat Intelligence Are Stronger Together: 15 Key Benefits
The Internet is a vast and complex landscape, much larger than the familiar interface we use every day. Similarly, some cryptomarket drugs—MDMA powder and cocaine—were far less likely to contain adulterants. But others—amphetamine and LSD—were found to be more likely to be adulterated than samples acquired in-person. He recommends verifying market employees carefully, and to weed out law enforcement infiltration through barium meal tests.
Russian Market
You can even use a secure email provider or a burner email address whenever you visit the dark web. The website has a sleek design and interactive user interface, making it the most preferred choice in terms of user experience. You can pay through Monera and Bitcoin using the escrow system or the traditional market account after making a purchase on this shop. If you want to buy something, deposit cryptocurrency in your wallet, and you will be charged directly. Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection.
Related Articles From The Safe Browsing Section
Founded in 2014, BriansClub remains one of the oldest and most infamous dark web markets for stolen credit cards, fullz (complete identity kits), and dumps. Launched after the takedown of AlphaBay in 2021, Abacus Market has rapidly risen to prominence. It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data.
Users seeking enhanced focus, energy, or euphoria may unknowingly consume substances with severe cardiovascular and neurological risks. For several years, Yahoo was at the apex as the internet’s best web service provider, offering… If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. It will make your VPN activities seem like normal traffic, so you can use an uncensored internet. A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks.

A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. You should never use your personal information on the dark web anywhere else in your life. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. For example, it maintains your privacy and enables you to access untraceable content and services.
Encrypted Communication Tools
Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy.
Invictus Market
One of the key factors driving the success of darknet markets is the vendor rating system, which allows buyers to evaluate sellers based on product quality, delivery speed, and communication. This transparency fosters trust and encourages vendors to maintain high standards. Additionally, the diversity of products available on these platforms has expanded, offering everything from pharmaceuticals to rare substances, catering to a wide range of consumer needs. Security protocols on these platforms are continuously updated to address emerging threats. Features such as two-factor authentication, end-to-end encryption, and regular security audits ensure that user data and transactions remain secure.
Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing. Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else. In some authoritarian states, accessing Tor nodes can flag you for surveillance. They can also take advantage of legitimate software to hide their tracks. For example, YoMix is a bitcoin mixer used by the Lazarus Group to launder their stolen cryptocurrency profits, with a massive influx of laundered funds in 2023. For those seeking secure cloud-based file storage, this comprehensive list provides the ultimate…
The Torrez market is one of the biggest dark net marketplaces, also called a community-driven marketplace. It contains a good selection of product listings that range over 35,000 items. The website has an interface and design similar to other dark web shops. It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security. Vice City Market is a new and cutting-edge dark web marketplace where you can find a range of products and vendors at an affordable price (compared to the damage they do to the victims).
Using a reliable VPN with Tor provides a way to improve security when accessing dark web links. The VPN encrypts your traffic before it enters the Tor network, preventing your ISP from seeing that you’re using Tor. This double encryption also protects against compromised Tor entry nodes that could potentially monitor your activity.



