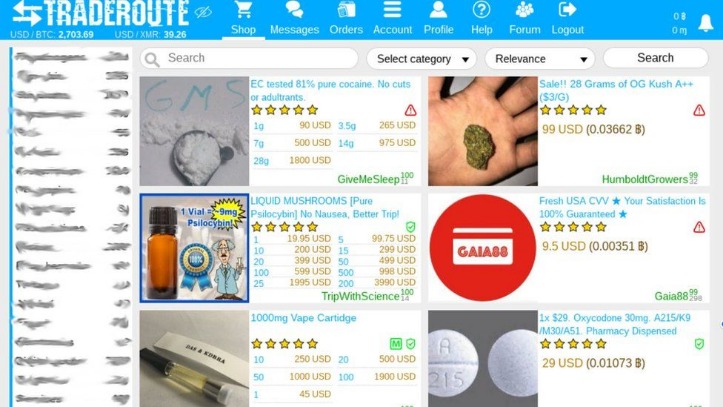
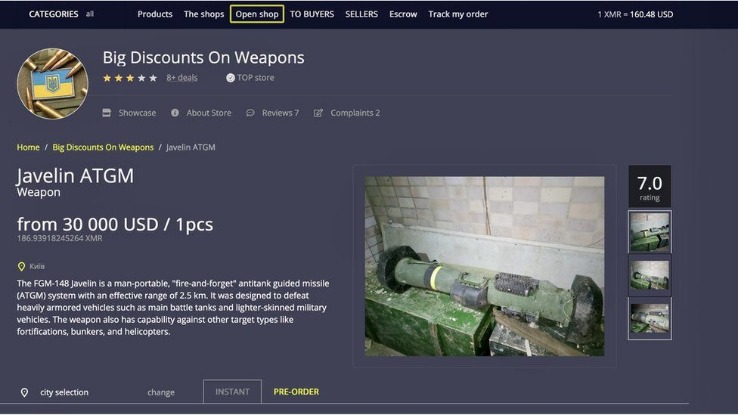
Like ransomware, criminals can buy software and inject your devices with viruses. With it, they can spy on people, steal their sensitive data, or secretly control their devices. These software are also capable of launching DDoS attacks and phishing campaigns. These marketplaces are full of risks (security, legal, ethical issues – all of them). But if you still decide to access these websites, for education or research purposes, make sure you stay cautious. Although these marketplaces are continuously shut down by law enforcement agencies, they still work today.
Average Prices Of Common Dark Web Items (
The data format, which includes user agents and victim IP addresses typically observed in both local and global phishing attacks, allows us to assert with high confidence that it originated from such activities. To combat these threats, banks allocate substantial resources to fraud detection and prevention. Advanced cybersecurity tools and artificial intelligence are increasingly used to predict and mitigate fraudulent activities. These technologies analyze real-time data to identify suspicious transactions, reducing potential losses. Regular audits and compliance with standards like the Payment Card Industry Data Security Standard (PCI DSS) are also essential to maintaining secure systems and practices. One of the earliest and most notorious dark web marketplaces was the Silk Road, which paired the darknet with Bitcoin for anonymous transactions.
The only way in is through the use of special software that renders all users anonymous and untraceable. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products. Torzon Market has established itself as a significant player in the darknet ecosystem, offering a secure, user-centric platform for anonymous trading. Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet.
Facebook Hidden Friends Vulnerability (With “fb-hfc” Released)
If you’re looking to understand how the dark web is shaping cyber threats in 2025–26, this comprehensive guide provides the stats, insights, and trends you need to stay informed—and stay secure. DeSnake joined the conversation, creating an account with his moniker on September 12, 2021 in attempts to mitigate the marketplace’s potential reputation damage. DeSnake repeatedly pointed to their vouches from Dread and old PGP key pasted to Ghostbin, paste site. DarkOwl has been unable to assess how the larger darknet community (outside of Dread) feels about the new Alphabay Market.
Stay Within Legal Boundaries

Regarding the validity of the stolen payment card dataset, additional details such as user agents, IP addresses, dates of birth, and email addresses suggest with high confidence that the information is authentic and not generated. The validity of cards obtained through phishing can vary; however, they often demonstrate a relatively high validity rate due to several factors. Customer feedback from b1ack’s operations further corroborates this assessment. Considering this backdrop, it is evident that b1ack’s primary goal has consistently been to profit from the sale or use of these stolen credit card details.
KYC Compliance & Identity Verification

On September 13, I wrote about how an earlier dive into the dark web economy by Armor Threat Resistance Unit researchers revealed it was possible to exchange $800 (£630) of Bitcoin for $10,000 (£7,900) cash. At the time, that sounded like an unbeatable deal for those willing to break the law and face the jail time. And then along came the Flashpoint analysts who found even bigger illicit “bargains” in these dark web marketplaces. Access to a compromised bank account, known as a “bank log” in cybercrime parlance, with a balance of $10,000 (£7,900), could be yours for $25 (£19.75), for example. While personal information packages that enable a criminal to steal the victim’s identity, or “fullz” as they are known, and achieve a promised $20,000 (£15,800) bank loan cash-out were on offer for just $5 (£4) more. If that sounds cheap, fullz packages start at around $4 (£3) as they are seen as a commodity item within these circles.
Risks And Threats On The Dark Web
Deep web marketplaces are online marketplaces where people can buy and sell illicit goods and services under the protection of the anonymity of the dark web. The goods and services on offer range from leaked credit card details, exploit kits, and hackers for hire to advertisements for hitmen services. Launched in 2020, Cypher Marketplace sells fraudulent documents, stolen credit cards, fake IDs, and malware. Its emphasis on user anonymity and document forgery makes it a core tool for identity fraud. For those interested in digital products – like stealer logs – RussianMarket and 2Easy are the most popular alternatives to Genesis, having already proved their capabilities.
- The market facilitates trades in stolen credit card data, hacked bank accounts, and services to facilitate the laundering of cryptocurrency.
- If any user is found not complying with the law, strict and immediate action will be taken against them.
- Stolen credit cards are used to cash them out or make purchases that can be resold.
- Moreover, the layers of encryption and the bounce of your data from node to node effectively mask your IP address, enabling online anonymity.
- Just like on the regular internet, phishing is a big problem on the dark web as well.
Operating on the darknet, Cosmos Market offers a wide range of illicit goods and services, drawing buyers from all corners of the globe. Security experts are alarmed by its growing popularity and the potential risks it poses to both users and the online community. As authorities continue their battle against cybercrime, Torrez Market remains a significant player in the shadowy world of the dark web. The market facilitates trades in stolen credit card data, hacked bank accounts, and services to facilitate the laundering of cryptocurrency. In fact, everything is in English, and the site picks up users everywhere in the world.
- Simple mistakes—such as inadequate operational security practices, sharing identifiable details, or using compromised devices—can quickly compromise anonymity and expose users’ real-world identities.
- Carding shops are a type of dark web marketplace that hosts the trade of credit cards and other stolen financial information.
- Use of fullz by bad actors presents a risk to businesses who allow for digital identity verification, as fullz give fraudsters a deep ability to impersonate a legitimate customer.
- The terms “deep web” and “dark web” often appear interchangeably in headlines, but they describe very different slices of online reality.
Here’s What Your Data Sells For On The Dark Web
These packages are typically sold on the dark web or underground forums, where cybercriminals trade in stolen data. Fullz are highly sought after by fraudsters as they provide all the necessary information to commit various types of identity theft, including credit card fraud, loan applications, and even tax fraud. Carding shops are a type of dark web marketplace that hosts the trade of credit cards and other stolen financial information. These platforms serve as hubs for cybercriminals to buy and sell compromised payment card details. In the mysterious world of the dark web, security professionals have their eyes fixed on the best dark web marketplaces.
How To Access The Dark Web Safely
The BBC’s Tor mirror (bbcnewsv2vjtpsuy.onion) delivers global news to audiences in countries that block the broadcaster’s regular site. During the February 2024 Iranian protest blackouts, digital‑rights monitors reported traffic spikes to the mirror as citizens sought unfiltered coverage—proof that onion sites can outmaneuver nationwide filters. The Experian Smart Money™ Debit Card is issued by Community Federal Savings Bank (CFSB), pursuant to a license from Mastercard International.
Hacked Online Services & Entertainment Accounts
Online payment methods such as mobile payments and payment processors are becoming more popular among retailers. However, as demonstrated in the table below, there was a small general downward trend in the prices of these items. As the Dark Web market evolves, its operators adopt strategies and priorities similar to those of traditional marketing and retail businesses. Then, you can set up 2FA (two-factor authentication) for that extra touch of security in case someone somehow figures out your password.
First things first, always use strong and different passwords for each account you open. They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk.
Ticketmaster Data Breach (
A senior member from the carding community Ranklez claimed he had evidence to suggest Cazes wasn’t alpha02. Ranklez and alpha02 had a history in the carding community as Ranklez sold alpha02 fullz for conducting identity theft. To access them, you usually need the actual link and proper authentication, including repositories, member platforms, company databases, or de-indexed sites.



