It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address.
By combining security best practices with tools like search Deep Web engines, organizations can transform the Deep Web from a blind spot into a source of intelligence. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe. Your ISP can’t see which websites you’re visiting on the dark web when you’re using Tor, but they might be able to predict or assume you are using Tor if they analyze your monitored internet traffic. The users of the dark web are typically aiming to block governments from snooping on them.
Avoid Dropping Personal Information On The Dark Web

Naval Research Laboratory, this technology was initially designed to protect government communications. Over time, it has become an essential tool for individuals seeking to browse the internet anonymously or evade censorship in restrictive environments. Unlike the dark web, which necessitates anonymizing browsers such as Tor, the deep web is accessible via standard web browsers. However, most deep web content is gated behind login credentials, subscription fees, or institutional access permissions.
How Can I Find Sites On The Deep Web?

Keep reading to discover the differences between the deep web and dark web and what they mean for your online safety. One drug dealing website called Silk Road became so famous it was routinely cited as an example of the dark web in mainstream media reports. Its owner was eventually arrested and sentenced to life in prison with no chance for parole. We test each product thoroughly and give high marks to only the very best.

Media Outlets With A Secret Door

Hacker services against banks and other financial institutions are offered there. Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution. The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures. The release of Freenet in 2000 is considered by many as the start or founding of the dark web. University of Edinburgh student Ian Clarke created Freenet as a thesis project. Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito.
Called “dark” because it is accessible with anonymity and only through certain networks and software such as Tor, this part of the Internet represents a small fraction of the overall Web. The deep web search engine operates on the same infrastructure as the surface web but consists of content not indexed by conventional search engines. This includes dynamically generated content, private databases, password-protected sites, and content requiring specific permissions or protocols.
It is tremendously more vast than the surface web, with some experts estimating that search engines index less than 1% of online content. Unlike the dark web, which is deliberately obscured by layers of technology, the deep web exists just below the surface web. The majority of the deep web consists of regular websites that require users to create an account before they can be accessed. The dark web is a subsection of the deep web including websites that one can only access through purpose-built web browsers.
Besides, governments might actively monitor such activity, and anyone showing a keen interest in the dark web can become a law enforcement target. A major chunk of the dark web is home to illegal activities or things, such as banned drugs, weapons, stolen identities, for-sale malware, looking-for-work cybercriminals, and whatnot. Dark web hosts project which ends with .onion (aka onion sites) and not .com, .net, .org, etc. that we generally operate with.

Encrypted Communication Tools
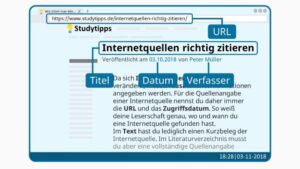
- You can also search Google Books, which contains extra information you won’t find in Google.
- But then you hear terms like ‘Dark Web,’ ‘Deep Web,’ and even ‘Gray Web’.
- It is a good way to prevent third parties from tracking online activities.
- The Deep Web refers to web data you can’t find using a search engine like Google.
Without the Deep Web, sensitive communications would be exposed to the open web, making data breaches and identity theft far more common. For comprehensive protection against scammers, viruses, and ransomware across every layer of the internet, get Norton 360 Deluxe. Although the deep web’s information isn’t indexed by regular search engines, it can often still be accessed. The terms deep web and dark web are sometimes used interchangeably, but they are not the same.
- This .onion link makes it impossible for hackers to impersonate your profile.
- In other words, the deep web covers everything under the surface that’s still accessible with the right software, including the dark web.
- This is the primary reason why the US NRL developed the TOR technology used by most Dark Web visitors.
- Examples include software as a service (SaaS) solutions, paid news websites, and streaming services.
- Data in the Deep Web is hard for search engines to see, but unseen doesn’t equal unimportant.
- ExpressVPN is an excellent choice for Tor and accessing the Dark Web.
What Is The Deep Web?
However, it’s much harder to get at the people who are doing the uploading and downloading. Sections of the dark web are often closed down too, as part of police operations. DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links. These typically come with “.onion” after them, rather than something like “.com” as on the standard web. Open up Tor, and you won’t suddenly see the dark web staring back at you.
A Common Misconception: The Deep Web Vs The Dark Web
The average person doesn’t share their private life with just anyone; they let specific people know about it when the information is needed. For example, you might tell your closest friend about a problem in your personal life, but you would not tell the clerk at your grocery store. The deep web encompasses any content that exists on the deep web cannot be accessed by a search engine. Apart from that, the content that you access on the deep web is very similar to the type of content that you would access on the surface web.
Onion Links: How To Access Them
And while it’s based on the Mozilla Firefox browser, Tor is not as well maintained and has page rendering issues. For starters, much of the content on the deep web is irrelevant and would only make searches that much more difficult. And there’s also a privacy issue; no one would want Google bots crawling their Netflix viewings or Fidelity Investments account. The most common way to access the dark web or deep web is by using the Tor network, and doing so is not nearly as complicated as you might think. First, you need a web browser that’s capable of utilizing the Tor protocol.
Understanding BlackCat Ransomware: Threat Overview And Protective Measures
Though you don’t have to perform a penetration test on every website you log in to, you should ensure that it runs on a secure framework that uses HTTPS encryption. The deep web is defined as the internet section that is not indexed by web crawlers. The dark web, on the other hand, is defined as a subsegment of the deep web that can be accessed only with special tools.
Mullvad VPN
Today, many organizations exist that are created only to handle these reports anonymously and effectively. They know how to process the information and get it to the correct law enforcement agencies internationally. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user. The use of the dark web raises suspicion as it shows there is something you want to do privately. Therefore, the legality of the dark web will mainly depend on how you use it.
Without this security, neither firms nor individuals could safely conduct financial transactions over the Internet. The dark web was designed mainly to provide users with more privacy. Also called the hidden web or invisible web, the deep web is different from the surface web, where contents can be accessed through search engines. Information on sites like Investopedia is part of the surface web, as it can be reached through search engines. Most experts estimate that the deep web is much bigger than the surface web.