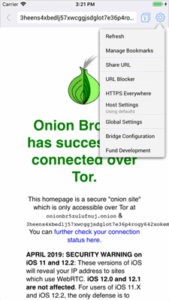
If you’re using a browser like Tor and visiting .onion websites that aren’t accessible through regular search engines or browsers, you’re likely on the dark web. These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers. Keep in mind that visiting the dark web isn’t illegal, but engaging in criminal activity there is.

Venus crawls and gathers a wide array of onion sites, ensuring you have access to the latest information available on the dark web. The search engine doesn’t impose censorship, meaning you can find a broad spectrum of sites, including those that may be illegal or disturbing. Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you’re looking for.
Are There Dark Web Links For Android Devices?
While the dark web is not inherently illegal, it does host a range of illegal content, hidden services, and illicit activities. It is a private search engine that lets you search the regular internet via Tor. This allows you not only to visit sites with the added privacy provided by the Tor network, but also search the web as privately as possible from inside the Tor browser.
How To Access The Dark Web
For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy. Although profiting from pirated copyrighted material is unethical and illegal, there are some exceptions to using copyrighted material, such as a “private study” provision under UK law. The CIA is contactable on the dark web, providing a completely anonymous way to get in touch with them. However, if you’re communicating with state intelligence agencies, you should use Tor alongside a VPN for maximum privacy. Otherwise, the first node in the onion relay system sees your real IP address, which can be used to locate you and unveil your identity. The New York Times can also be anonymously accessed via the dark web.
Dark Web Tools And Services
NoScript and HTTPS Everywhere extensions provide additional protection against malicious scripts and unsecured connections. A reliable VPN encrypts your traffic before it enters the Tor network, preventing surveillance from your ISP or malicious actors. During my tests, ExpressVPN’s military-grade encryption and verified no-logs policy provided consistent protection against tracking and monitoring.
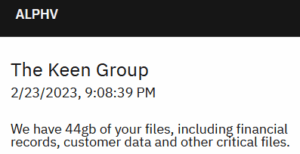
- By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet.
- Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims.
- Archetyp Market – Gaining popularity due to advanced security protocols and a user-friendly interface.
- It also offers a comprehensive list of marketplaces, exchanges, and websites linked to fraudulent activities, helping you stay informed.
- Its strength lies in regular updates and community-driven verification of links.
How Do I Find onion Links For Sites?
While OnionLinks hosts links to both legal and illegal content, it reflects the dual nature of the dark web itself. On one end, you’ll find links to independent journalism platforms like ProPublica’s .onion site and encrypted communication tools like SecureDrop. On the other, there are links to darknet markets, mixers, and carding forums—elements of the underworld that raise ethical and legal concerns. OnionLinks does not host this content directly, but by linking to it, it treads a gray area that reflects the broader debates surrounding online anonymity and regulation. Security protocols on these platforms are continuously updated to address emerging threats.

Features That Make WTN Market A Secure Platform

Such content fuels a dangerous cycle of abuse, violence, and exploitation. While hiring a hacker might sound like something out of a movie, it’s a very real threat. Businesses may use these services to sabotage their competitors, while individuals may seek revenge or simply want access to private information about someone. These hackers don’t hide in the shadows as much as you might think. Anything from planting malware and stealing sensitive files to hijacking email accounts or breaking into social media profiles.
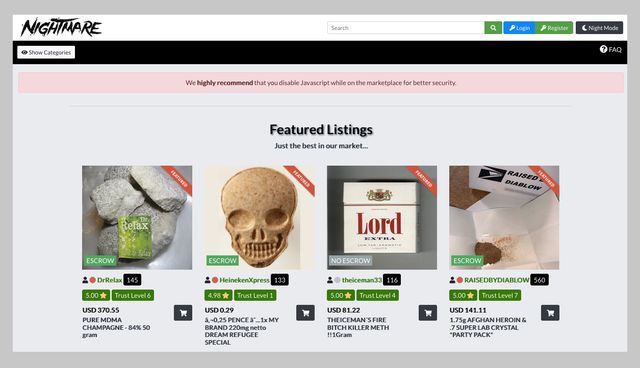
These platforms rely on advanced encryption and decentralized systems to ensure anonymity and reliability for both buyers and sellers. The best darknet markets in 2025 prioritize security, reliability, and user experience, making them ideal platforms for the drug trade. These markets leverage advanced encryption technologies, such as Tor and PGP, to ensure that transactions remain private and secure. Vendors and buyers benefit from end-to-end encryption, which protects communication and payment details from unauthorized access.
D Onion Websites: Between Anonymity And Risks
I’ve been poking around these places for a while now, from the giants like Abacus to the old-timers like Vice City. This isn’t just a quick list; it’s the full scoop on what they offer, how they keep things tight, and why they’re worth your time—or not. Whether you’re new to the dark web or a vet who’s seen it all, you’ll find something here to chew on. Below, I’m breaking down each market with everything I’ve picked up—listings, quirks, the works. Onion sites can be safe in terms of privacy protection due to strong encryption, but they also host a significant amount of illegal content and scams.
You’re only scratching the surface when you use the Internet for daily activities—reading news, managing finances, running businesses. Search engines like Google, Bing, and Yahoo can access just about 4% of the web. Activists, whistle blowers, and journalists also use the dark web to communicate securely with sources and news organizations. mark it means it has been verified as a scam service and it should be avoided.}
Therefore, you will always find updated search results while using this service. The developers of ProtonMail recommend using the Tor browser to visit the dark web version of the service. This ensures greater security and privacy, making it much more difficult for snoopers to get in. Another standout feature is that the servers can’t see what you type, copy, paste, or send. To increase the security level, add password protection and determine the expiration time for messages.
Darknet Markets Darknet List 2025 Darknet Market Links Darknet Market Links In 2025
Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection. A VPN hides the fact that you’re using Tor, which is blocked in some countries and always raises doubts because of its criminal reputation. By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited. The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero.