In particular, causes of death are likely to be best identified when the cause is unique and obvious, while the potential for bias increases when comorbidities exist or when the cause of death is occluded by more proximal sources. Furthermore, post-hoc analyses suggested that this null finding may have been due to competing causes of death among Blacks which may mask an association. Although our inability to explore this is a limitation of our study, examining all-cause mortality provides some protection against this potential bias. A growing body of evidence indicates that the unique constellation of environmental stressors and psychosocial challenges experienced by Blacks in the US contributes to accelerated declines in health and generates racial disparities 1.
Should You Use A VPN And Tor?
According to the report, that is incredibly important to brands because African American buying power is at $1.3 trillion currently and based on gains in population, income and education, it’s estimated to rise to $1.54 trillion by 2022. More than half (54%) of all African Americans have lived their entire life in the digital age. These tech-savvy Gen X, Millennial and Gen-Z consumers represent a coveted market segment whose interconnectivity is central to their everyday lives—particularly the product purchase cycle. The report urges smart marketers to recognize this shift from consumer to creator and offers insights on building new inroads to this culturally conscious and digitally native consumer segment. New York, NY – Sept. 13, 2018 – African American consumers are enjoying a remarkable period of influence, cultural expression and entrepreneurship that is manifesting digitally and trending mainstream, according to global researcher Nielsen.
“If the site invests in setting up a ‘native’ Tor onion-address for their website, then people who use the Tor browser to access that address never step outside the protection of the Tor cloud,” Muffett says. Tor refers to “the onion router”, which is a network that bounces your traffic through random nodes, wrapping it in encryption each time, making it difficult to track; it’s managed and accessed via the Tor browser. That may seem an extreme way to browse the web, but such protections are increasingly worth considering, says Sarah Jamie Lewis, executive director of the Open Privacy Research Society.
For example, although legally sanctioned forms of criminal profiling may not have an overt racial component, they have been applied inequitably and found to disproportionately impact racial minorities 15. Racial discrimination in employment and housing markets has also been found to occur covertly despite being expressly prohibited by law 16, 17. Discrimination can also be experienced more subtly through interpersonal interactions, such as instances of being treated with less respect or courtesy, being followed in stores, or receiving poorer service at restaurants 18. In contrast to traditional, overtly racially motivated discrimination and prejudice, attributions of intent for these experiences are often less clear. Furthermore, individuals may not disclose experiences of discrimination, or may be unaware “invisible” discrimination and racist events that are not directly experienced 14.

How To Access The Dark Web Safely And Securely
Some dark web commerce sites have dangerous chemicals and weapons for sale. The standard dark web browser is Tor Browser, which directs your browser traffic through the Tor network so you can reach the darknet. As your traffic passes through Tor, it’s encrypted and bounced between at least three relay points, known as nodes.
As Society Moves Online, Many Are Left Behind
This allows them to respond quickly to new business opportunities and stay ahead of the competition. On the other hand, with Wireless NaaS, you only pay for the service and don’t have to worry about software/hardware/licensing costs, daily monitoring and management, or ongoing maintenance and upgrades. As a result, the total cost of ownership for Wireless NaaS can be significantly lower compared to traditional wireless network solutions. Advocates heralded Project 2025 as a means of restoring traditional American values and streamlining government, while critics raised concerns about potential rollbacks on civil rights, environmental protections, and equity-focused programs. The rise of cryptocurrency, and in particular Bitcoin, significantly increased the dark web’s use in illegal trade. Users could exchange funds online without sharing credit card numbers or other identifying information.
Understanding BlackCat Ransomware: Threat Overview And Protective Measures
Illegal cyber activity cannot necessarily be stumbled upon easily but tends to be much more extreme and threatening if you do seek it out. Before we unpack the dark web’s threats, let’s explore how and why users access these sites. The reputation of the dark web has often been linked to criminal intent or illegal content, and “trading” sites where users can purchase illicit goods or services.
Art, Race, And The Internet: Mendi + Keith Obadike’s BlackNetArt Actions
In February 2011 Ross Ulbricht founded what is believed to be the dark web’s first black market, Silk Road. The U.S. Federal Bureau of Investigation (FBI) arrested Ulbricht in October 2013, but imitators still arise, many much larger. Being hidden doesn’t translate into being completely protected from the possibility of tracking, or, when it comes to illegal activities, of risk. However, it’s up to us to take control of our personal privacy in a world of bulk data collection, surveillance, and personalized ad tracking. There are numerous directories that host .onion links and websites, but you should always exercise caution. Some will lead you to commercial sites that deal in everything from illicit drugs to fake passports, whereas others are non-commercial and include legal content, such as education and training workshops, forums, and personal blogs.
Method II – VPN Over Tor
To access a dark web resource, you will need to know its web address to the letter. These websites will also use .onion top-level domain names, and many of them will be very long, random combinations of letters and numbers. You won’t be able to access .onion addresses using a standard search engine as they aren’t indexed by crawlers. No longer restricted to dial-up, many of us now consider access to a stable high-speed internet connection a critical element of our daily lives. We pay our bills online, check our bank statements, communicate via email, find information, and maintain a presence on social media. Some of the websites to look out for on the dark web include mirrors of both the BBC and the ProPublica investigative journalism platforms, built to help inform people who are living in countries where the internet is heavily censored.
“The mission of Black Fashion Fair is to discover, support, and further the trajectories of designers and the communities they inspire,” Gregory said. “Creating Black Fashion Fair was me trying to offer an alternative to traditional retail concepts and methods because Black designers are left out of those spaces.” TikTok has swooped in and staked its claim within the entertainment industry as the go-to destination for discovering new artists, influencers, and talent. If you delve deeper you’ll realize the app’s simple interface is an ideal medium for dreaming up innovative content. Breakr, a new tech start-up from four Florida A&M University alumni aims to disrupt spaces like TikTok.
More On How To Stay Safe On The Dark Web
BlackPlanet arguably laid the foundation for social media as we know it, including, of course, Black Twitter. VPNs are often recommended as protection in such cases, but Whited disagrees. “All of your traffic goes through it, and you have to trust them as if they are your new ISP. Because the backbone of our software is a decentralised network, you don’t have to trust us to browse the internet privately.” Infiltrations can put you at risk of monitoring for other types of activity as well. Evading government restrictions to explore new political ideologies can be an imprisonable offense in some countries.
- But if you want to find something specific, you can also ask a Librarian to help you locate it.
- Dawn Dickson, an e-commerce entrepreneur, founded PopCom as a hybrid firm in 2017.
- This browser is a service originally developed in the latter part of the 1990s by the United States Naval Research Laboratory.
- Some hackers offer ransomware as a service (RaaS), where cybercriminals can “rent” a strain of ransomware from its creator in exchange for a fee or a percentage of their ransom payments.
- The dark web can certainly be dangerous — with no regulation, it’s a riskier place to hang out than the surface web.
However, these names likely conjure up a scarier conception than the real definition of the dark web. This means that the JavaScript will be disabled by default on every website and some symbols and images will not be displayed. Well, there’s a reason why it’s recommended to browse with a minimized or rescaled window – you can be tracked based on your active window’s dimensions (yeah, they really can do that). So, do yourself a favor and rescale that Tor window as much as you can before proceeding.
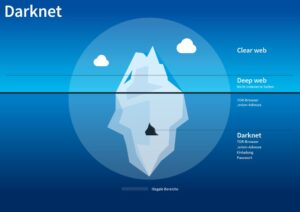
At the dark end of the web, you’ll find the more hazardous content and activity. Tor websites are located at this far end of the deep web, which are deemed the “dark web” and are only accessible by an anonymous browser. The deep web rests below the surface and accounts for approximately 90% of all websites. This would be the part of an iceberg beneath the water, much larger than the surface web. In fact, this hidden web is so large that it’s impossible to discover exactly how many pages or websites are active at any one time.