However, in the event of a dispute don’t expect service with a smile. Every communication is encrypted, so even the simplest transaction requires a PGP key. Law enforcement officials are getting better at finding and prosecuting owners of sites that sell illicit goods and services.
Criminal Hacking Services
But human trafficking, illegal pornography featuring underaged victims, money laundering, and assassinations are also examples of the darkest corners on the dark web. Pixel Privacy believes in digital privacy and does not believe in using it for heinous and/or illegal activities, and so the focus of this article will be on legal activities. BLACKOPS flickered into being under a phantom known as “Desnake,” a figure veiled in mystery who saw beyond the clutter of bloated markets. Launched on May 17, 2020, it carved a lean path—drugs alone, no sprawling excess—a deliberate choice to shun the glare that toppled giants like Silk Road. Fueled by Monero’s untraceable pulse and Tor’s layered cloak, it’s a market where silence is strength, pulsing beyond the surface web’s grasp. And beware—while many explore out of curiosity or for research purposes, it’s important to remember that engaging with these platforms, even as an observer, can lead to serious legal and ethical consequences.

After AlphaBay closed, Abacus Market took its place as the world’s largest underground darknet marketplaces. Abacus Market quickly rose to prominence by attracting former AlphaBay users and providing a comprehensive platform for a wide range of illicit activities. It goes without saying — the dark web and its hidden marketplaces can be a dangerous rabbit hole. This article offers you a quick rundown on the black market and how to get access to hidden sites, the risks involved and key measures to ensure your security. Still, even with these crackdowns and better defenses, dark web markets just keep coming back.
- It’s recommended not to use new alternative links as they could just be planned exit scams.
- Markets like AlphaBay and Hansa adopted stronger encryption and expanded offerings to include hacking tools and stolen data.
- Nevertheless, by analysing the income of each multiseller, we observe that the median income still reflects their high income, as shown in Fig.
- Therefore, as long as this dark part of the internet exists, these marketplaces will flourish and emerge.
- The goal is simple — make financial fraud easy and get as much attention as possible.
- Cybersecurity companies and researchers monitoring darknet markets face legal and ethical restrictions.
Hacking Services
The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web. The disappearance of Black Ops Market underscores the cat-and-mouse game between darknet operators and authorities. While advanced encryption and decentralized hosting (e.g., I2P) prolong market lifespans, persistent vulnerabilities—such as PHP exploits or admin leaks—often lead to takedowns.
Disgruntled Developer Gets Four-year Sentence For Revenge Attack On Employer’s Network
To reduce the presence of noise in the S2S network, we consider only stable U2U pairs, i.e., pairs that have at least three transactions throughout the whole period of observation13. The trading volume generated by stable pairs is more than five times larger than that of non-stable pairs13. The S2S network is mostly populated by U2U-only sellers, followed by market-only, and market-U2U (see Supplementary Information Section S5). Kingdom Market is a newer darknet market that has been around since April 2021 but was only recently vetted for listing on Dread, the pre-eminent forum for markets on the dark web. It features a unique site design unlike any other market yet is still intuitive and easy to use.
From the last quarter of 2013, U2U-only sellers become the largest category of sellers and remains as the largest throughout the rest of the observation period. Connecting to the Tor network might raise eyebrows depending on who and where you are. Although data sent through Tor can’t be tracked or decrypted, your internet service provider and network administrator can still see that you’re using Tor. The VPN’s encryption will hide from your ISP the fact that you’re using Tor. The dark web contains much of the internet’s illicit content, ranging from drug trafficking to child pornography sites. After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages.
Versus Market (Best For User Reviews & Vendor Ratings)
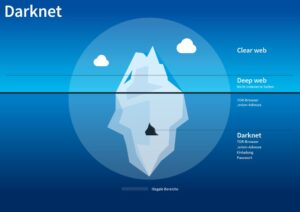
The deep web is made up of content that search engines such as Google do not index. Such data includes medical records, financial information, research papers, private forums and networks, and other content. Darknet markets operate within this hidden space, often hosting illegal activity, while the deep web primarily consists of everyday private or password-protected content.
Don’t Provide Personal Information
Overall, dark-web marketplaces inherently involve substantial risk, and users must thoroughly understand these threats. Anyone considering engaging with these platforms must carefully evaluate potential consequences, exercise stringent security practices, and remain vigilant to minimize exposure to these significant hazards. Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences. When both buyers and sellers are anonymous, the credibility of any ratings system is dubious. Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias. More often than not, law enforcement is targeting the sellers more than the buyers.

More Ways To Stay Safe On The Dark Web
Deep web includes pages and databases not indexed by search engines, typically because they’re behind logins or other security walls. Those can be private company databases, financial account dashboards, subscription-only content, or student portals. Many people go to the dark web to buy things they can’t find elsewhere, but what if what you’re buying is also trying to harm you?
Many mainstream media organizations monitor whistleblower sites looking for news. You can conduct discussions about current events anonymously on Intel Exchange. There are several whistleblower sites, including a dark web version of Wikileaks.
Purchasing or selling illegal goods—such as controlled substances, counterfeit documents, or stolen data—can result in significant legal penalties, including fines, criminal charges, and imprisonment. Even users who access these platforms without intent to buy illegal items risk suspicion or investigation. The Dark Web—a hidden part of the internet accessible only through specialized software like Tor—has become increasingly significant as we enter 2025. It was quite popular for selling a wide range of products and services. It offers impressive features, including PGP-signed addresses, payment via Monera, sticky and featured listings, and auto shops. In 2017, the website went offline following a law enforcement action taken by the American, Canadian, and Thai authorities, but since August 2021, it’s been operational again.
New darknet sites and markets continuously emerge to replace those that get shut down. The technology behind the darknet is actively maintained and continues to evolve. The Silk Road was a famous dark web marketplace where users could buy and sell goods and services anonymously.
We’re back with another video in our Webz Insider video series on everything web data. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. We respect your privacy and never track or record any details of your online activity. So, be sure that whatever you do on the Internet—browsing, downloading, and other habits — remains completely confidential. Weak passwords like the date of your birth, “password 123”, and other easy-breezy ones are a criminal’s dream. Make sure you create strong unique passwords for every online account.