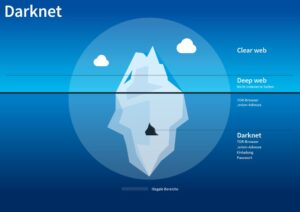
When both buyers and sellers are anonymous, the credibility of any ratings system is dubious. Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias. The deep web is the part of the internet you can’t access through search engines like Google and Bing. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. It contains 7,500 terabytes of information, compared with only 19 terabytes of information in the “surface” web.
Taking the necessary precautions makes tracing your activities on the dark web difficult. For example, I strongly advise using a reliable VPN like NordVPN. Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection. However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities.
Real-World Examples: Data Breaches Feeding Dark Web Black Markets
SecureDrop is one of the most reliable file-sharing sites on the deep web. SecureDrop helps whistleblowers anonymously send sensitive material to media outlets via a unique SecureDrop URL. The files are automatically encrypted, and the sender’s IP is not logged. ZLibrary hosts free file-sharing access to academic texts, scholarly articles, and general-interest books.
Disable Java And ActiveX In Your Network Settings
Dark web monitoring platforms, such as Lunar, provide an automated solution to safeguard personal identifiable information (PII) and credit card details. These platforms continuously scour the deep and dark web, looking for any traces of your sensitive information. By setting up alerts, businesses can receive notifications whenever their PII or credit card information appears in suspicious contexts. This proactive monitoring enables businesses to track and investigate potential threats in real-time, helping to prevent fraud before it can impact their operations. The use of such platforms is crucial for maintaining the integrity and security of customer data, and it provides an additional layer of defense against cybercriminal activities. Darknet markets facilitate transactions for illegal goods and services.
Silk Road 20
The marketplace has over 8,400 listings and 500 vendors who communicate in English and accept Bitcoin for transactions. Conversely, transaction networks obtained from the blockchain contain the entire transaction data of the DWMs and U2U transactions, allowing a thorough investigation of the ecosystem as a whole. In fact, previous studies on DWM transaction networks have revealed crucial aspects of the ecosystem13,14,15. However, they have so far mainly focused on DWM users, without distinguishing between buyers and sellers, and neglecting the different weight that more active users may have in the system. The reason is that the operational structure of DWMs inherently hides the seller–buyer link, as all transactions are made through the marketplace.
Report It To The Authorities (if It’s Safe To Do So)
Silk Road was once the most well-known dark web marketplace, but after its shutdown, many new markets took its place. Today, buyers and vendors look for reliable alternatives that offer security, escrow protection, and a strong vendor community. The dark web isn’t illegal, because it’s essentially just an anonymous web browser providing a platform for various websites.
- Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security.
- To counter these risks, organizations need robust, proactive solutions that go beyond traditional cybersecurity measures.
- Dream’s founder had been arrested by US authorities in August 2017.
- Apart from the dark web markets that are operating online today, some raided platforms influenced many markets.
- You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is.
- With the onion browser, you can access ordinary HTTPS websites on the web.
More Ways To Stay Safe On The Dark Web
As enticing as it might be, don’t follow links to other parts of the dark web. In combination with that data, and data gathered by other methods and/or tactics may in fact lead to complete exposure and could eventually lead to the police standing at your doorstep. This type of government surveillance applies mostly to countries with environments that are hostile to free speech.
Its founder, Ross Ulbricht, was arrested, and law enforcement took control of the site. Since then, many copycat markets have tried to replace it, but not all of them have lasted. The key differences between dark web markets and regular online stores are clear. Regular stores are public, with visible ads and a standard payment process. They usually accept cryptocurrencies, such as Bitcoin, which keeps transactions secret.
The Top 6 Deep And Dark Web Credit Card Sites
The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for. Talking about copycats and potential risks, due to its high risk and low signal-to-noise ratio for legitimate content, we advise beginners and privacy-conscious users to avoid The Hidden Wiki. If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites. Technological advancements can both aid and hinder black market activities. While improved encryption and anonymity tools help protect users, enhanced tracking and surveillance technologies pose new risks.
Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination. Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny. The US Supreme Court has indicated that even casual browsing could lead to legal consequences. After a buyer bought something, their payment was held in escrow to help guarantee that shoppers would receive the agreed-upon goods or services. David is a programmer and writer who has worked as a software developer at MIT.
(The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder. So, once you’ve activated your VPN and your privacy is secured, it’s time to visit Tor’s official download page. Instead, you need to get the Tor browser to access the dark web. Make sure that when you download the Tor file, it’s from their official website. But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network.
One of the best Silk Road alternatives today is We The North Market. With its low 5% vendor fee, secure transactions, and verified sellers, it’s an ideal choice for buyers looking for a trusted marketplace. Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences.
Instead of ending in .com or .co, dark web websites end in .onion. That’s “a special-use top level domain suffix designating an anonymous hidden service reachable via the Tor network,” according to Wikipedia. Browsers with the appropriate proxy can reach these sites, but others can’t. A VPN protects your connection against everyone, not just your ISP and the authorities.
As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products.
Dark Web Search Engine
HSI New York leads and directs all operational and administrative activities of the El Dorado Task Force (EDTF). The EDTF encompasses a standalone Cyber Division as part of an effort to stay abreast of emerging criminal threats and in keeping with current and future investigative priorities. The EDTF’s mission is to disrupt, dismantle or render ineffective organizations involved in the laundering of proceeds of narcotics trafficking and other financial crimes.