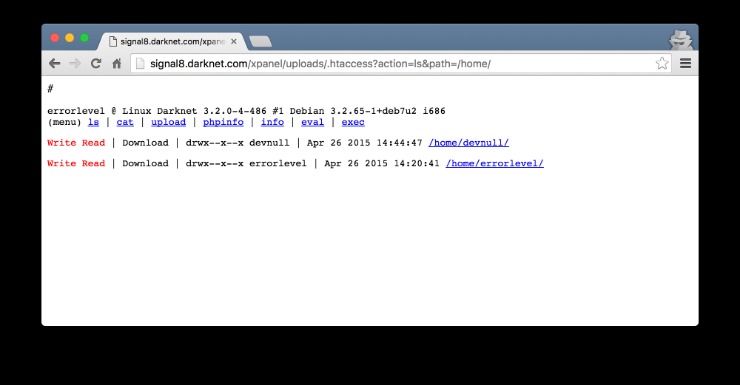
Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails. This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to. Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down. Due to its absolute anonymity for knowledgeable users, the chance of running into bad people is also realistic, as they can operate relatively freely without the fear of getting caught doing something unlawful. On top of that, the installation process of Freenet is rather easy. Simply download the file, install the software, and you’re ready to use its web-based interface.
Hence, it should be the top priority to track these platforms and shut them down as quickly as possible. The buyers, or “consumers,” are cybercriminals who use these tools to launch illegal activities. The victims, who are common users, businesses, and even banks, who end up paying the price.
How To Access The Dark Web Safely And Securely
We also conceptualize OBMs as crowd-powered catalyst organizations and recommend LEAs to monitor OBMs dynamics balancing the technological and the social dimensions. OBMs serves as digital innovation hubs for criminal communities and can be used to discover new schemas of illegal activities. Digital infrastructure, also called information infrastructure or cyberinfrastructure, is a term which encompasses a socio-technical interconnected structure of systems, people and organizations (Henfridsson & Bygstad, 2013). In an era defined by digital connectivity, protecting sensitive, critical and personal information from cyber threats – including those originating from the dark web – is a strategic imperative. International Standards offer organizations a robust, globally recognized framework to strengthen cybersecurity resilience, mitigate risks and safeguard sensitive and critical data from unauthorized access and misuse.

These marketplaces are full of risks (security, legal, ethical issues – all of them). But if you still decide to access these websites, for education or research purposes, make sure you stay cautious. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals. This trove of stolen data included names, addresses, Social Security numbers, and phone numbers, leaving millions of individuals vulnerable to identity theft. Shortly after the breach, a hacker group known as USDoD listed this data on dark web marketplaces, pricing it at a staggering $3.5 million.
Common Scams On Dark Web Marketplaces
The categories are well organized, ranging from drugs and fraud to digital products, guides, and malware.What really sets it apart is its focus on security and usability. It supports PGP encryption, two-factor authentication (2FA), alerts against fake sites (antiphishing), and a verification system for sellers. Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero. All of this has made it one of the most reliable markets still active in 2025.
Hidden Answers
The dark web remains a persistent challenge for law enforcement and cybersecurity professionals. While it offers anonymity and opportunities for illicit activities, it also presents significant risks to individuals and businesses. By understanding the nature of dark web markets and the threats they pose, we can take steps to protect ourselves and mitigate the impact of cybercrime. Dark web marketplaces aren’t just peddling the same old stolen credit card numbers and drugs anymore.
The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. It will make your VPN activities seem like normal traffic, so you can use an uncensored internet. However, this feature is only available on iOS, Android, and Windows.

Don’t Provide Personal Information
Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions. Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they’re doing and what they’re looking for. You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment).
History Of Dark Web Marketplaces
If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail. Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators. Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. The use of the dark web raises suspicion as it shows there is something you want to do privately.
Why Security Leaders Prefer To Buy CTI Solution For SaaS Platforms In 2025
When you know what to expect, you’re less likely to fall for a trick and should be able to keep your identity safe. Once many users begin to rely on the site and store funds in escrow, the operators disappear, taking all the money with them and leaving their customers and clients with nothing. Drug dealers can sell to customers across the world, not just locally. This expanded reach, combined with anonymity, only makes it easier for them to grow their operations without getting caught immediately. Surprisingly, most guns on the darknet actually start as legal products. The UNODC (United Nations Office on Drugs and Crime) maintains that almost all firearms are originally manufactured through legal means.
These onion addresses will remain online even if the original page disappears. It also keeps the graphical copy and text of the page for better accuracy. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live. The good news is that the BBC Onion site is an international edition. As a result, it not only focuses on the UK but also provides worldwide news.
WANT TO TRY THE TOP VPN RISK FREE?
Find exclusive digital assets and services while ensuring your identity remains hidden and your transactions secure. MEGA has a wide range of illicit drug offerings in their market catalog including items ranging from marijuana to opiates with delivery across the Eastern Slavic language countries of Russia, Ukraine, and Belarus. Similar to other anonymous centralized markets, MEGA also supports vendors selling digital goods such as databases, carding and counterfeit related products, and ready to use hacking software. MEGA features a hidden service layout very similar to RAMP, with over 200 links to unique vendor shops from the landing page and many of the same drug vendors that once traded on RAMP also advertise on MEGA. Dark web marketplaces are websites where you can exchange illicit goods and services like stolen credit cards, account login credentials, counterfeit items, drugs, and other items. Usually dark web transactions are made with Bitcoin or other cryptocurrencies.
- However, such shocks do not affect the existence of OBMs (Décary-Hétu & Giommoni, 2017).
- The quantity, price, and characteristics of the product are all provided.
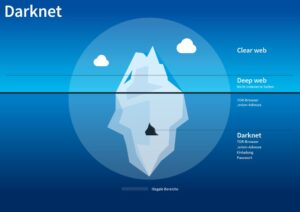
- You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web.
- The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown.
- While they won’t disclose details of their operations, many have dedicated cyber units with specialized training, intelligence sharing, partnerships with industry, and joint operations.
The Silk Road was a famous dark web marketplace where users could buy and sell goods and services anonymously. All the payments were made through cryptocurrency, further enhancing marketplace anonymity. The users on this site can review and rate the products that promote reliable and fraudster vendors. To prevent the users from DDoS attacks, it provides personal marketplace domains to high-volume buyers and sellers. Moreover, this shop provides detailed statistics about each user profile on the platform, giving users a better idea about the vendors for the buyers and vice versa. This marketplace accepts payments via Monero but also supports the Escrow system.