This survey highlights active and recently shuttered markets with actionable metrics and intelligence for threat hunters, CISOs, and red team leaders. Blockchain forensics and artificial intelligence have advanced crypto crime detection by trawling humongous databases in order to flag suspicious transactions. AI simplifies pattern recognition, and blockchain forensics leverages openness in trying to follow illegal transactions and construct lawful evidence.
#BHUSA: 1000 DoD Contractors Now Covered By NSA’s Free Cyber Services Program
Smart contracts manage vendor-buyer interactions, and blockchain-based dispute systems replace traditional moderators. In exploring the top 10 dark-web marketplaces in 2025, we’ve examined their core operations, diverse use-cases, inherent risks, and evolving trends. While these marketplaces continue to serve legitimate purposes, such as enabling secure communication and privacy protection, they also remain hotspots for illicit activities and cybercrime. Technological advancements like AI-driven security, quantum-resistant encryption, and blockchain integration are reshaping the landscape, but simultaneously, global enforcement efforts grow more sophisticated and collaborative.
Layering, Smurfing, And Other Laundering Techniques
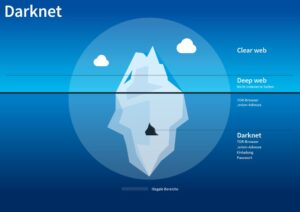
Nevertheless, due to their unregulated nature, DWMs exhibit behaviours not observed in regulated marketplaces. They offer anonymity to their users by using and developing specialized tools. DWMs are accessed through darknet browsers supporting the onion routing protocol (e.g., Tor), which provides anonymous communication connections35.
Blockchain Transaction Tracing
Specifically, to be classified as a multiseller, a user must be classified as a seller in at least two markets simultaneously. The multihomers play a crucial role in the ecosystem because they act as edges between markets. While there may occasionally be multihomers who are active in several markets simultaneously (see Supplementary Information Section S3), multihomers predominantly operate in at most two markets throughout the period of observation.
Darknet entities received only 0.3% from online wallets in 2019 compared to 4.6% in 2011. But during the last two years, the incoming flow from wallets has doubled. The Crystal analytics team have compiled a detailed report based on investigations into darknet interactions using bitcoin, and how regulation is changing trends. In total, Abacus Market generated nearly USD 100 million in Bitcoin-enabled sales. However, considering that Monero — a privacy coin — typically accounts for two-thirds to three-quarters of total volume, Abacus’s sales are likely closer to between USD 300 million and USD 400 million.
Money Laundering
Ideal marketplaces support anonymous browsing through networks like Tor and I2P, utilize privacy-focused cryptocurrencies such as Monero, and implement measures to prevent tracking and transaction tracing. Platforms that provide clear guidelines for maintaining operational security (OpSec) and offer built-in tools for data obfuscation are especially favored. Another notable trend is the rise of encrypted peer-to-peer (P2P) messaging systems integrated directly within marketplaces, providing secure communication channels between buyers and sellers. The integration of blockchain-based smart contracts is also becoming widespread, automating secure transactions and reducing the likelihood of fraud. The Dark Web—a hidden part of the internet accessible only through specialized software like Tor—has become increasingly significant as we enter 2025.

Shifts In User Behavior And Marketplace Structures
Correspondingly, the multihoming activity is a mechanism that contributes to the ecosystem’s resilience. Because they are already active in more than one market, the migration cost for the multihomers is usually smaller compared to that for non-multihomer users, especially for sellers, that need to rebuilt their reputation23. The empty point on the multiseller median income line demarcates the quarter with only two multisellers. After that quarter, their number remains small, which is represented by the dashed line. In all panels, the dashed vertical line marks the time of operation Bayonet. Given the darknet’s infrastructure, which is hidden behind onion routing, the darknet attracts sites whose proprietors want to remain anonymous.
These marketplaces are full of risks (security, legal, ethical issues – all of them). But if you still decide to access these websites, for education or research purposes, make sure you stay cautious. In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures.
- However, we are not aware of any mechanism in the market to delete user accounts that have been inactive for a long time, although we believe this may exist but not be reported or well-known.
- It offers access to hacked bank accounts, credit card data, and cryptocurrency laundering tools.
- Due to law enforcement, many markets now require invites, referrals, or verified PGP identities.
- Users will be aware that operators may have lost control of the market if the canary is not updated within the mentioned date.
- In 2025, the dark web no longer exists in isolation—it interacts with mainstream platforms, influences real-world crime, and exploits cutting-edge financial systems.
Data And Methods

It hosts over 40,000 listings and offers everything from illicit goods and substances to hacking tools. With an estimated market value of around $15 million, it has grown into a massive hub for cybercriminal activity. In conclusion, this paper presents the outcome of our investigation into how security mechanisms are implemented in mainstream dark web markets. In particular, we highlight that the twelve dark web markets we observed have different levels of security to protect themselves and their users.
Nevertheless, finding the perfect balance between financial secrecy and regulatory needs is a future challenge for digital finance. Additionally, we analyse the U2U network of transactions, i.e., the transactions between pairs of market first-neighbors where the source and destination nodes are market users without the market as an intermediate. In the U2U network, an edge connects nodes that are not necessarily users of the same market. Previous studies have shown that, although the number of users and transactions is larger in markets, the trading volume in the U2U network is larger than that of markets13. Each marketplace is a star-graph where the central node is the marketplace, and the leaf nodes, i.e., the first-neighbors, are the marketplace users.

Interaction Between Darknet Entities
Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs. Hydra also featured numerous vendors selling false identification documents. Users could search for vendors selling their desired type of identification document – for example, U.S. passports or drivers’ licenses – and filter or sort by the item’s price. Many vendors of false identification documents offered to customize the documents based on photographs or other information provided by the buyers.

Historically, DNMs have been known for the illicit drug trade, but in recent years have differentiated themselves with unique service offerings. For example, in Russia-based DNMs, the illicit drug trade remains predominant. Since last year’s Crypto Crime Report, the top performing Russia-based DNMs have held steady, but Kraken DNM overtook Mega as the leading DNM by annual revenue in 2024. It added that many fraud shops are increasingly offering third-party crypto-payment processors like UAPS via API calls, as a way to reduce their own costs, improve operational efficiency and increase security. However, overall the sector has fragmented somewhat from the days when Silk Road, AlphaBay, Wall Street Market and Hydra ruled the roost.
Discover everything about what a darknet market is, top marketplaces, security threats on them, and learn how to protect your data online. 1Transaction volume is a measure of all attributed economic activity, a proxy for funds changing hands. DNMs received $2 billion as opposed to close to $2.3 billion in 2023, while fraud shop volume is down by slightly more than half at $220.1 million. Blockchain intelligence firm TRM Labs reports that Abacus shutting down so abruptly has all the indications of either an exit scam or a covert law enforcement operation dismantling the activity. Malicious vendors often infect buyers with spyware, ransomware, or infostealer malware hidden in downloadable files. Some listings are nothing more than scams designed to trick people into sending cryptocurrency without delivering anything in return.
Instead, law enforcement agencies now appear to focus more closely on the vendors. Without vendors, darknet marketplaces cannot operate or generate profits, making them a more strategic enforcement target. The evolving landscape of cryptocurrency usage within darknet marketplaces has once again shifted, with Bitcoin (BTC) reclaiming its position as the primary means of exchange. This resurgence follows the delisting of Monero (XMR), a privacy-focused cryptocurrency, from major exchanges, significantly impacting its accessibility and liquidity.