The built-in browser is hardened for maximum privacy, and it is integrated with the OS’s security features. Not only will it not work, but it’ll also leave a big digital footprint. Purchases through links on our pages may yield affiliate revenue for us.
Using Tor Browser FAQs

Therefore, you should stay cautious and avoid clicking when accessing the dark web. Doing so will protect you from accidentally accessing illicit content or becoming a victim of malware. Additionally, much of the materials on the dark web are illegal, and unknowingly downloading such content can implicate you in criminal activities punishable by laws. If your device is infected with malware, read our guide to remove malware from your computer.
The CSO Guide To Top Security Conferences
This makes it extremely difficult to find out who you are transacting with. The good news is that the platform will not see what you copy/paste. Your data is encrypted in the Tor browser before reaching the ZeroBin servers. Blockchain.info (now Blockchain.com) is a popular cryptocurrency wallet and blockchain explorer service (one of the first sites to launch on the dark web).
Some users also share links on encrypted apps like Telegram or Keybase that you can check. Naval Research Laboratory mathematicians and computer scientists in the mid-1990s. The U.S. Army developed “onion routing” to protect intelligence communications online. Social networks, such as Facebook, have created dark web versions of their sites to address privacy problems related to their surface web versions. ExpressVPN had created a .onion version of its website to allow greater privacy and anonymity for Tor browser users. DuckDuckGo offers an .onion version of its search engine, while Sci-Hub offers access to millions of scientific articles and papers.
How To Use Tor Browser Safely
If you need a way to organize as an activist or you want to discuss censored topics with others, my first suggestion is to stick to offline meetups. The second, less secure option is to use encrypted messaging apps with ties to specific non-profit or activist organizations. For example, Briar is an extremely private chat app designed to help journalists communicate anonymously with sources. Signal is our Editors’ Choice for private messaging apps because it does a great job of blending privacy and social media functionality for a highly customizable chat experience.
Regularly Update Your Software
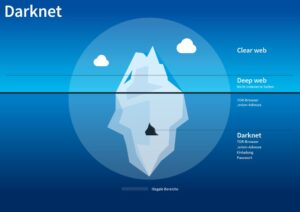
Beneath this surface lies the deep web, encompassing private databases, subscription-only services, and other non-indexed content. Within the deep web is an even more hidden layer known as the dark web, accessible only through specialized browsers like Tor. Tor (The Onion Router) is a free and open-source dark web browser that enables anonymous communication by routing Internet traffic through a volunteer network of over 6,000 relays. The Tor Browser opens access to “.onion” sites, unique addresses within the dark web. Its multi-layered encryption is a cornerstone of anonymous browsing on the dark web. Tor is one of the easiest and safest ways to access the dark web, which is unavailable to normal “surface web” browsers.
Accessing The Dark Web With Tor Browser And VPN
ExpressVPN is my top choice because it supports Tor traffic on all of its servers and works automatically without needing any additional configurations. It also provides super-fast speeds, and its no-logs policy has been independently audited and confirmed — this way, you know it doesn’t store any user data. Plus, it backs all first-time purchases with a 30-day money-back guarantee, so you can try it out risk-free. I review privacy tools like hardware security keys, password managers, private messaging apps and ad-blocking software.
How Tor Browser Works
If you live in a regime that blocks Tor or need to access a web service that blocks Tor, you can also configure Tor Browser to use bridges. Unlike Tor’s entry and exit nodes, bridge IP addresses are not publicly listed, making it difficult for web services, or governments, to blacklist those IP addresses. Using a VPN alongside Tor adds an extra layer of security by hiding your IP address from Tor entry nodes and encrypting your traffic. This prevents anyone—including your ISP—from knowing that you’re using the Tor network. The Deep Web includes unindexed content like private databases and password-protected sites accessible with standard browsers. If you engage in illegal activities or access illegal content that could implicate you in a criminal offense, you may face serious legal consequences, including fines and imprisonment.
If you want privacy and anonymity, NordVPN accepts payment in Bitcoin. Moreover, it offers a 24/7 customer support service and a 30-day money-back guarantee. Due to its hidden nature, the dark web is also famous for the names underground internet and black web.
- Since then, volunteers and sponsors around the globe have maintained Tor and the Tor Browser.
- This is one of the reasons why it is always good to hide your IP address.
- While getting in isn’t that difficult, doing so safely does require following some basic steps—especially if you want to keep your privacy intact.
- Advocacy groups are also reaping the advantages of the darknet because, here, the term of censorship is as popular as HTTPS.
You might fall to the wayside of legal lines for many reasons that are important for the protection of freedom. Others may act in ways that are illegal for the protection and safety of others. Let’s unpack both of these concepts in terms of the “dark web browser” and the websites themselves.
- Some of these cybercriminals are known to track and blackmail pedophiles.
- By routing internet traffic through multiple nodes, Tor provides a high level of anonymity for users accessing the Dark Web.
- While compatible with “.onion” services, Ahmia also filters search results to exclude potentially harmful or malicious websites.
- Understanding the implications of visiting the dark web requires a nuanced look at various legal aspects and potential consequences.
- Law enforcement agencies in many countries monitor the dark web to combat illegal activities.
- Similar to onion websites, I2P lets you access hidden I2P websites (also known as eepsites).
Suppose you share your name, social security number, or any other personally identifiable information on any dark website. In that case, there is a high chance that your data will become accessible to cybercriminals. Then, they can use your data to impersonate you and run social engineering attacks to target your loved ones. You might visit the dark web seeking anonymity or unique services, but this anonymity also attracts scammers.

Click the button, get the provider for around $3.3/mo, and install it on your device. NordVPN works on every Tor-friendly system – Windows, Android, Linux, and macOS. However, while Tor is great, safe, and whatever you think, it’s not as great as another component – a VPN. We must explain that Tor is safe on paper but practice has shown that this browser can fail you. Cryptocurrency is often used for payments on the dark web, exposing users to fraud or money laundering schemes. By following these precautions, you can significantly reduce the risk of falling victim to scams and malware on the Dark Web.
It collects data from the public Tor network and archives historical data of the Tor ecosystem. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live. The good news is that the BBC Onion site is an international edition. As a result, it not only focuses on the UK but also provides worldwide news.