This misuse allows cyber criminals to reach a broader audience while evading detection—blending into the digital spaces that consumers and businesses use every day. Prices of information on the Dark Web are shaped by multiple factors ranging from database security to the specific vulnerabilities in stolen data. Vx-underground operates as a prominent channel for sharing malware-related content, offering insights into recent threats, leaked tools, and historical malware samples. It serves as a resource hub for cybersecurity researchers, regularly posting files, reports, and threat actor-related commentary. The ease with which any item, from stolen physical things such as credit cards to huge dumps of personal information, can be found and bought online should give everyone pause.
The dark web has become a notorious hub for illegal activities, and credit card fraud is no exception. Criminals exploit the anonymity and encryption features of the dark web to buy and sell stolen credit card information. This underground marketplace offers a range of stolen credit card details, including card numbers, CVV codes, and even full personal information. Card Shops are a type of dark web marketplace that hosts the trade of credit cards and other stolen financial information.
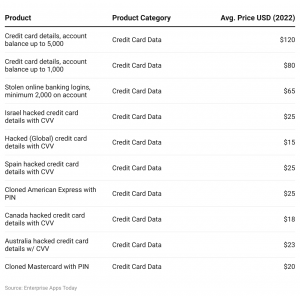
This includes using strong passwords and enabling two-factor authentication. Adding fullz to a card purchase increases the price by about $30 for a physical card and under a dollar for digital card info. A quick guide for developers to automate mergers and acquisitions reports with Python and AI.

Carding Is A Cyber Crime Niche Of Its Own
This latest breach serves as a stark reminder of the ongoing threat posed by cybercriminals and the importance of robust cybersecurity measures for you to put in place if you have not already done so. While you are thinking these are probably already old numbers no longer active, a vast majority of this enormous database originates from American victims. If you have been affected by the breach, you must take immediate steps to protect yourself from the potential consequences of identity theft and fraud.
How Does Credit Card Fraud End Up On The Dark Web?

Stolen credit cards are used to cash them out or make purchases that can be resold. Dark Web credit cards can be a nightmare for victims, often leaving them with significant financial losses and damaged credit scores. Many cybercriminal groups announced their support for Durov and continue to rely on Telegram’s strong encryption and familiar infrastructure.
How Do Dark Web Monitoring Platforms Like Lunar Help In Tracking Activities On Dark Telegram Channels?
Once stolen card data hits the dark web, it can be hard to track down just where it lands, and it can be even harder to prosecute offenders. LeakBase, which has an important place for database leaks, emerged in 2023. The forum focuses on database leaks and includes a community that challenges the Breach forum. The forum is free to join and member status can be upgraded within the forum. Active database leaks are shared in the forum mainly by the staff team.
Escrow And Feedback Systems
Legitimate users of the dark web include activists, or people who live under oppressive regimes, but they only account for a small percentage of the dark web. The sale of payment card information is big business; in 2022, the average price of stolen credit card data averaged between $17 and $120, depending upon the account’s balance. Digital banking has transformed both consumer banking and the threats posed to banks and their customers. In addition to new scams and schemes targeting online banking customers, we have seen the evolution of criminal marketplaces to trade in stolen information, stolen accounts, and stolen money.
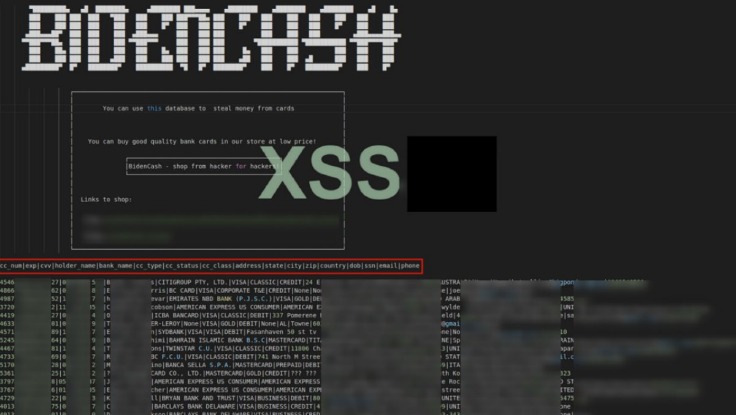
Credit Cards Skimmed And Used As Marketing Tool
- Since then, BidenCash has continued to operate using the “dumping” method.
- All of these features, its competitive pricing, along with the volume of credit card information listings, make Real and Rare one of the prime sites to trade credit card information online.
- Whistleblowers, journalists, and individuals living in repressive regimes often use the Dark Web to communicate securely and protect their privacy.
- These are hard to detect, but only using ATM machines inside banks or other physical buildings offers some protection, Thomas says.
- Leveraging real-time visibility into Telegram will empower cyber pros to rapidly respond thus reducing the risk of critical security incidents.
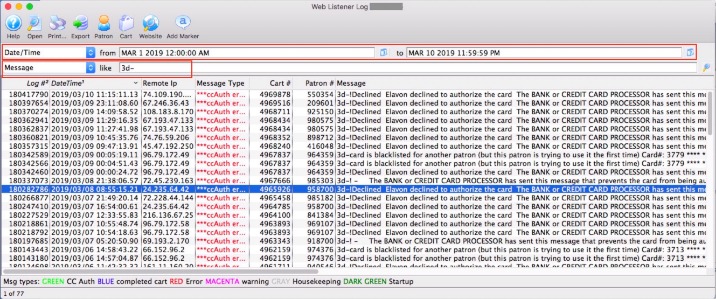
However, this same anonymity also makes onion websites a breeding ground for illicit activities. The stolen credit card records include credit card and owner details, including credit card number, expiration date, CVV number, holder’s name, country, state, city, address, zip code and email address or phone number. In our research of the data of 1M leaked credit cards on the Dark Web, we analyzed the leaked email addresses to gain a better understanding of the risk. Additionally, fraudulent charges can lead to overdraft fees, late payment penalties, and damage to credit scores. These financial losses can have a lasting impact on victims’ financial stability and may require extensive efforts to resolve the issue and regain control over their finances. To avoid such losses, it is crucial to regularly monitor credit card transactions, report any unauthorized charges promptly, and take proactive steps to protect personal information.
The use of JavaScript-sniffers, also known as Magecart, has led to a significant increase in stolen payment card data. The cards were likely compromised online, using phishing, malware, or JavaScript-sniffers, which are increasingly popular among cybercriminals. Regularly monitoring your credit card statements can help you detect any suspicious activity, such as unauthorized transactions.
- The administrators of the largest illegal marketplace on the darknet for stolen credit cards are retiring after making an estimated $358m (£260m).
- When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track.
- This new trend for marketplaces winding down in an orderly fashion is known as “sunsetting” or “voluntary retirement”.
- Abacus Market quickly rose to prominence by attracting former AlphaBay users and providing a comprehensive platform for a wide range of illicit activities.
- The price for cloned cards varies depending on the credit limit, with an average price of $171.
- If the number of credit cards from this latest release are still active, it would point to the site blossoming over the course of just a few months, as well as just how prolific online credit card theft has become.
What Are Ransomware Leak Sites

However, it’s noteworthy that this recent release lacks the comprehensive data quality that previously set BidenCash apart. However, the validity of the data hasn’t been confirmed yet, so it could very well be auto-generated fake entries that don’t correspond to real cards. And beware—while many explore out of curiosity or for research purposes, it’s important to remember that engaging with these platforms, even as an observer, can lead to serious legal and ethical consequences. While this topic may seem distant for most people, understanding how these spaces operate is crucial. It helps us stay more vigilant, better protect ourselves, and make informed decisions online.
Stay informed about the latest trends and tactics used by criminals to better safeguard your financial well-being. It’s important to detect fraud when a threat actor is trying to use stolen payment information to make a purchase from your business. Tools like an Address Verification Service (AVS) can help detect fraud in online purchases by comparing a customer’s billing address with the address on file with the issuing bank. Flare’s Dark Web Monitoring platform monitors dozens of .onion sites for credit card fraud, BINS and other financial fraud related data.
Experience Flare for yourself and see why Flare is used by organization’s including federal law enforcement, Fortune 50, financial institutions, and software startups. By monitoring the dark web, you can quickly identify when your cards are compromised through partner organizations or merchants. Security teams monitor for telltale signs of card data exfiltration.
Next, let’s explore how individuals can access the Dark Web safely, while minimizing personal risks and vulnerabilities. Next, we will explore the payment methods used on the Dark Web and the measures individuals can take to protect themselves during transactions. – Read feedback from experienced Dark Web users or trusted individuals who have had successful transactions with the vendor. Next, we will explore the significance of evaluating seller feedback and ratings on the Dark Web and how it can assist in making better purchasing decisions. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust. Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews.