By integrating top-grade security into their operations, organizations can not only reduce their exposure to cyber threats but also reinforce trust in an increasingly data-driven world. As cyber threats grow more sophisticated, organizations are keeping a close watch on the dark web. Companies use dark web monitoring to scan for leaked data, stolen credentials and breach indicators, helping them track and identify perpetrators. But let’s be realistic, the best defence isn’t just playing detective after the fact.
- The Dark Web refers to a specific section of the internet that exists on an encrypted network, intentionally hidden and accessible only through specialized software.
- Though using the Tor is completely legal and legitimate but there is some content that cannot be accessed as it is a punishable offence.
- Tor Over VPN is when you first connect your computer or mobile device to your VPN service and then use the Tor Browser to travel the internet.
- Beginner directories like The Hidden Wiki offer a starting point, but extreme caution is advised—many sites listed may be outdated, broken, or link to illegal content.
- As of early 2025 the reboot remains online, though it commands a fraction of its former traffic and faces constant DDoS attacks and phishing clones.
Dark Web: What It Is, How It Works, Types & How To Stay Safe
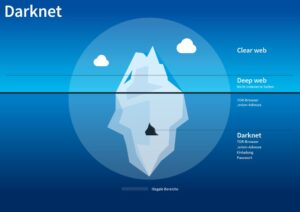
Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search. Policing involves targeting specific activities of the private web deemed illegal or subject to internet censorship. The deep web contains private networks used by business organizations, governmental departments, and educational institutions. These are used to share and exchange information without public exposure.

Q5 Are All onion Websites Illegal Or Dangerous?
Evading government restrictions to explore new political ideologies can be an imprisonable offense in some countries. China uses what is known as the “Great Firewall” limit access to popular sites for this exact reason. The risk of being a visitor to this content could lead to being placed on a watchlist or immediate targeting for a jail sentence. On the software end, the use of Tor and other anonymized browsers is not strictly illegal. In fact, these supposed “dark web” browsers are not tethered exclusively to this portion of the internet. Many users now leverage Tor to browse both the public Internet and the deeper parts of the web privately.
- The network is comprised of thousands of volunteer-run servers known as Tor relays.
- This prevents anyone—including your ISP—from knowing that you’re using the Tor network.
- And then there’s the “dark web”–hidden websites that won’t show up when you search Google, and can’t be accessed without special software.
- However, transactions involving controlled substances or hacking tools trigger the Controlled Substances Act, the Computer Fraud and Abuse Act and the Money Laundering Control Act.
- With many Tor-based sites being overtaken by police authorities across the globe, there is a clear danger of becoming government target for simply visiting a dark website.
External Links
The dark web is a small, hidden subset of the deep web that requires special tools to access. The dark web is home to the internet’s hidden sites, services, and products — some innocent, others downright dangerous. Read on to learn the pros and cons of the dark web, how to access it, and get tips for staying safe.
The Tor browser is based on Firefox and makes use of extensions like ‘NoScript’ to prevent harmful code from loading and there’s a built-in ad blocker (see below). There are also millions of servers which only store data which can’t be accessed via a public web page. Data brokers such as LocalBlox for instance crawl the web and store information about business and consumers to sell for marketing purposes. In order to understand the dark web properly, you need to understand that the internet is a huge and sometimes disorganized place. It has billions of sites and addresses, it is amazing that we can both search for – and find – anything.
Tor routes your internet traffic through a global network of volunteer-operated servers, hiding your location and encrypting your data at multiple levels. This makes it nearly impossible for anyone—governments, internet providers, or hackers—to trace your browsing activity back to you. While the Tor Browser looks and feels similar to Firefox, it’s specifically designed to connect to websites that aren’t accessible via regular browsers. It also includes paywalled services such as video on demand and some online magazines and newspapers.
Risks And Dangers Of The Dark Web
Furthermore, the dark web’s reputation often attracts curious individuals who are unaware of the potential risks. Casual exploration can lead to exposure to malware, scams, or illegal content, any of which could have severe consequences, both digitally and legally. While the dark web can serve legitimate purposes, such as supporting whistleblowers or journalists under oppressive regimes, it also facilitates illicit activities.
Afterwards, your request will be matched with the appropriate website. Tricky, but effective; that’s why it’s, by far, the best method to access dark web content. Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny. The US Supreme Court has indicated that even casual browsing could lead to legal consequences.
What Are EWallets And How Safe Are They?

Overall, the ending of the third season of “Dark” is a fitting and emotionally satisfying conclusion to a show that has captivated audiences with its complex and thought-provoking storyline. The ending ties together the various threads of the story in unexpected ways and leaves viewers with a sense of closure and resolution. The season ends with a stunning twist that ties together the various timelines and characters in unexpected ways. We see the true nature of the time loop and the interconnectedness of the various characters across different timelines. The final moments of the season show the characters finally finding peace and resolution, and we see the consequences of their actions play out in a deeply emotional and satisfying way. One of the key themes of the season is the idea of multiple timelines and the consequences of the characters’ actions in one timeline affecting other timelines.
How VPNs Are Helping People Evade Increased Censorship – And Much More

He focuses his writing on VPNs and security, previously writing for ProPrivacy before freelancing for Future PLC’s brands, including TechRadar. This process effectively masks your IP address, making it extremely difficult for anyone to trace your activities back to you. While most Tor users use this routing to send their traffic to the clear net, there’s another use for Tor routing. The dark web is a subset of the deep web which is difficult to regulate. Spaces on the dark web are specifically designed to offer anonymity and remain accessible only through specialized tools like Tor. In short, even with Tor, there’s no perfect anonymity online, but there are efforts to claw back our power online, says Lewis.
So, that means that the number of pages increased by over 100 trillion in just over three years. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine). It might sound weird that Google doesn’t index these pages, but it does carry some logical sense. Google’s purpose is to show the most relevant information to all of its users quickly and easily.
Top Dark Web Risks You Need To Know

A large portion of activities on the dark web involve illegal content, transactions, or services. Simply accessing certain sites or engaging with the wrong links could implicate you in criminal investigations. The Deep Web includes unindexed content like private databases and password-protected sites accessible with standard browsers. The dark web hosts various types of illegal content, such as stolen data, child exploitation material, and prohibited items. As an average Internet user, you may accidentally stumble upon such content.
How To Access The Dark Web Using The Tor Browser
Contrary to a widespread misconception, the dark web is a tiny part of the web. According to Recorded Future research1, out of 55,000 onion domains discovered, only 8,400 have a live site. “It’s essential for security professionals to approach the dark web with a strategic mindset focused on intelligence gathering rather than fear,” says Currie. AI-as-a-service (AIaaS) platforms offer many of these capabilities that lower the barriers for cybercriminals to carry out these attacks.