
“The Exam is far-reaching. I love that the questions are scenario based. I recommend it to anyone in the financial crime detection and prevention profession.” 1 The “coinbase transaction” is the transaction inside any block that pays the miners their block reward (As of November 21, 2019, the block reward is 12.5 bitcoin). This is not to be confused with the Genesis block, which is the name of the first block of Bitcoin ever mined by Satoshi Nakamoto in 2009. Furthermore, as mentioned prior, the technology technically originates as a piece of software, which does not fall into the category of a money transmitter. Enforcement of these regulations would be exceptionally difficult, and the resources required would be unreasonable, as every individual user would essentially need to be monitored.
Safer Drug Deals With Better Dарknet Security And Vendor Ratings
If you fall for it and log in, they immediately steal your credentials and either sell or use them for other scams. Once many users begin to rely on the site and store funds in escrow, the operators disappear, taking all the money with them and leaving their customers and clients with nothing. This can include everything from full names, email logins, and passwords to credit card details, social security numbers, and bank account information.
This can be stopped if law enforcement agencies can break any link, particularly dark web marketplaces, in the chain. Hence, it should be the top priority to track these platforms and shut them down as quickly as possible. The anonymity and lack of rules that define darknet marketplaces are exactly what make them breeding grounds for fraudulent activities.
Refresher On Blockchain
Bitcoin remains the dominant currency in darknet markets due to its decentralized nature and pseudonymous transactions. Its widespread adoption ensures fast, borderless payments without relying on traditional banking systems. Markets prioritize Bitcoin for its liquidity, though some now accept Monero for enhanced privacy. Finding reliable markets is streamlined through updated onion link directories, minimizing phishing risks. Vendor reputations are transparent, with detailed metrics on delivery times and product quality. By 2025, darknet markets have diversified, catering to niche demands while maintaining robust operational security.
This would allow gamers to buy in-game items or services for very small amounts of Bitcoin without having to pay high transaction fees. The Lightning Network allows for multiple transactions to occur within the same payment channel, which means that the cost per transaction is significantly lower than on the Bitcoin blockchain. The Lightning Network is a decentralized network built on top of the Bitcoin blockchain that allows for fast and cheap transactions. It was designed to solve the problem of scalability that Bitcoin faces, where the number of transactions that can be processed in a single block is limited. The Lightning Network is dependent upon the underlying technology of the blockchain.

The Escrow Process
Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero. All of this has made it one of the most reliable markets still active in 2025. The darknet continues to evolve as a reliable platform for drug transactions, with markets like Nexus and Abacus leading in 2025.
Use Cryptocurrency For Transactions
The victims, who are common users, businesses, and even banks, who end up paying the price. Ulbricht faced several serious charges, including distributing illegal drugs, running a criminal enterprise, hacking, trafficking fake IDs, and money laundering. In the end, he was sentenced to life in prison for running one of the largest and most scandalous dark web cases in history.

Exploring The Use Cases Of Darknets & Dark Markets
However, for mass adoption to take place of this new payment system, Bitcoin needs to be a viable and scalable medium of exchange instead of simply a store of value. To view your holdings in one of our investment products, please use the access details provided to you by your administrator. This article is for informational purposes only and does not constitute financial or investment advice.
- Also, when acquiring bitcoin make sure to use a non-KYC (know-your-customer) exchange.
- It provides a cost-efficient solution as mesh networks dynamically self-organize and self-configure, enabling dynamic distribution of workloads even if a few nodes fail4.
- Markets like AlphaBay Reloaded and Incognito use automated dispute resolution and decentralized hosting to minimize downtime and exit scams.
- “Operation RapTor shows that the dark web is not beyond the reach of law enforcement,” said Head of Europol’s European Cybercrime Centre, Edvardas Šileris.
- Nexus Darknet Market’s User Interface is distinguished for its exceptional design, providing straightforward navigation and an array of options in the top header.
Trustless And Secure
Some vendors offer services to help people “clean” illegally obtained funds using cryptocurrency and fake transactions. They mix and transfer funds through various privacy wallets and escrow services to hide the original source and make the illicit transactions harder to trace. Because the lighting network is built on Bitcoin’s blockchain, data can leak between those layers and reveal valuable information to attackers. Funding and channel close transactions can be used to link UTXOs to lighting nodes. Not even private channels are protected from this leakage, as sometimes they can publish information on-chain that reveals that the transaction was related to lightning network activity. The Lightning Network operates by creating a second layer above the Bitcoin blockchain, offering a pathway for off-chain transactions.
The combination of end-to-end encryption and decentralized hosting makes these markets resilient against takedowns. Buyers benefit from faster load times and improved uptime due to advancements in onion routing protocols. Demand for prescription medications and synthetic compounds remains high, with digital goods like hacking tools and counterfeit documents as secondary staples.

Too-good-to-be-true investment offers are another classic scam on the dark web. Early participants may see some profit, but that money usually comes from new victims, not actual earnings. Eventually, the system collapses, and most people lose their entire investment. Imagine trusting a site where you’ve been buying or selling for months, and everything seems legit. Some marketplace operators first build trust by running a legitimate platform. They sell these files for just a fraction of the original cost on the surface web or even share freely, which makes them tempting for people looking for shortcuts.
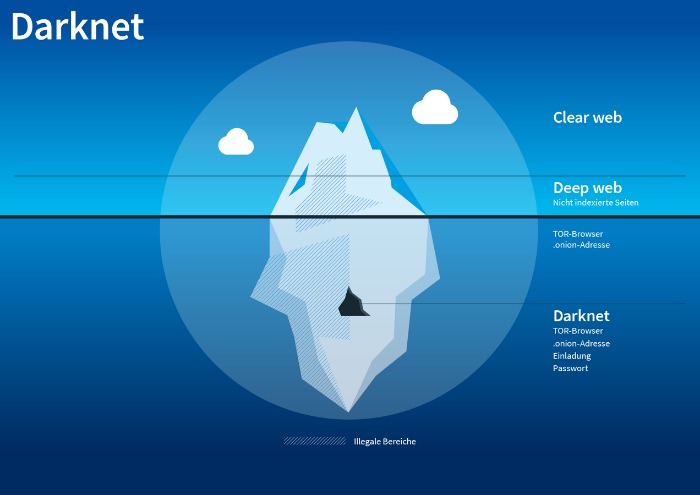
Is It Illegal To Access The Darknet?
Smart technologies make things easier, make the user experience better, and protect platforms from fears. All of these things help make darknet ecosystems more stable and user-friendly. AI is changing the way darknet marketplaces are run by making them safer and more automated. The most important aspect of darknet security is encryption mechanisms that keep users’ identities and data private. On Dec. 16, 2024, Rui-Siang Lin pleaded guilty to charges brought by the U.S. No, black market websites operate illegally and pose high risks of scams, fraud, and law enforcement action.
Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age. As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity. Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria. Since then, he has dedicated his career to writing extensively about crucial infosec, data privacy, and cybersecurity topics. When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements.
- This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk.
- When the attacker receives a payment, it starts a clock, routes the payment, and stops the clock when it receives the “receipt”.
- Some use them due to privacy concerns, such as journalists talking to informants or whistleblowers, while others may simply want to protect their confidential information from observation or tracking.
- The importance of Silk Road in Bitcoin’s history is, without a doubt, massive since it pioneered bitcoin’s use as a medium of exchange, and still remains the biggest bitcoin goods and services marketplace in history.
- Payment methods have expanded beyond Bitcoin, with privacy-focused cryptocurrencies like Monero becoming standard.
Advanced escrow systems ensure secure transactions by holding funds until buyers confirm receipt, minimizing fraud risks. Automated dispute resolution tools further enhance trust, with moderators intervening only in unresolved cases. Bitcoin was envisioned as a decentralized digital currency for fast, borderless transactions, but its growing popularity exposed a critical flaw—scalability. With an average of just seven transactions per second and confirmation times often stretching into minutes, Bitcoin’s network struggles to support the volume needed for everyday use. Enter the Lightning Network—a second-layer solution built on top of the Bitcoin blockchain.
Instead, similarly to what is known as the Hawala system, the Lightning Node of the coffee shop would accept the funds from Alice and note that Bob is owed 0.01 bitcoin. Using our example, this means Alice no longer must wait for a block confirmation for her purchase to be confirmed, as the funding transaction already locked her funds in the payment channel when it was created. The payment channel operates like a “tab” at a bar – a credit card (the funding transaction and promise of payment) is given to the bartender.



