While no information is stolen during a DDoS attack, it can be used for extortion or to conceal other hacking activities. A Distributed Denial of Service (DDoS) attack is designed to disrupt access to websites and other internet resources. This is achieved by overwhelming the targeted website’s server with thousands of connection requests, causing it to crash.
VPN Alternatives For Securing Remote Network Access
While receiving codes via SMS might be tempting, this is best avoided, as messages can be hijacked. With 2FA switched on, criminals won’t be able to hack into your account even if they have your log-in details as a further step is required to gain access after entering your password. Taking steps to prevent identity theft should be a priority for every single person online.
Namely, during the operation, the authorities seized $53.4 million in cash and cryptocurrency, 117 firearms, and 850 kg (1,874 pounds) of illegal drugs. The drugs included 258 kg (568.8 pounds) of amphetamines, 43 kg (94.8 pounds) each of MDMA and cocaine, and another 10 kg (22 pounds) of LSD and ecstasy pills. The marketplace’s founder, a man with dual Croatian-Serbian citizenship, was previously arrested and extradited to the US. In the case of businesses, and although we are talking about banks this applies to any industry, it is important to have the right partner.
Dark Marketplace Analysis

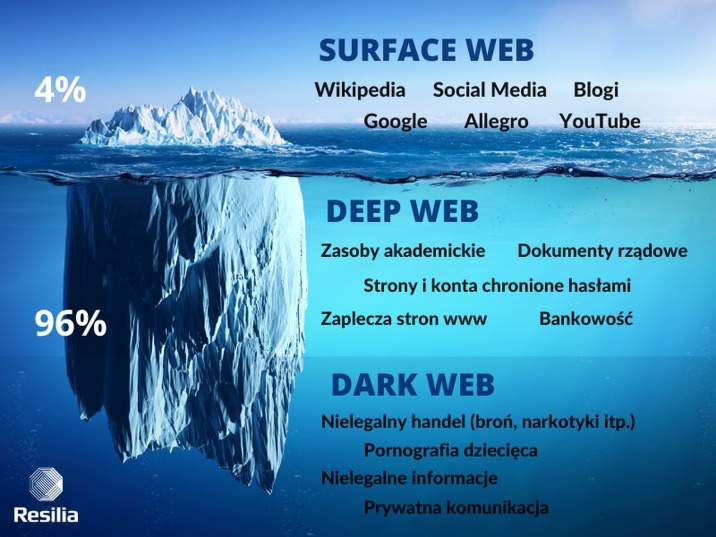
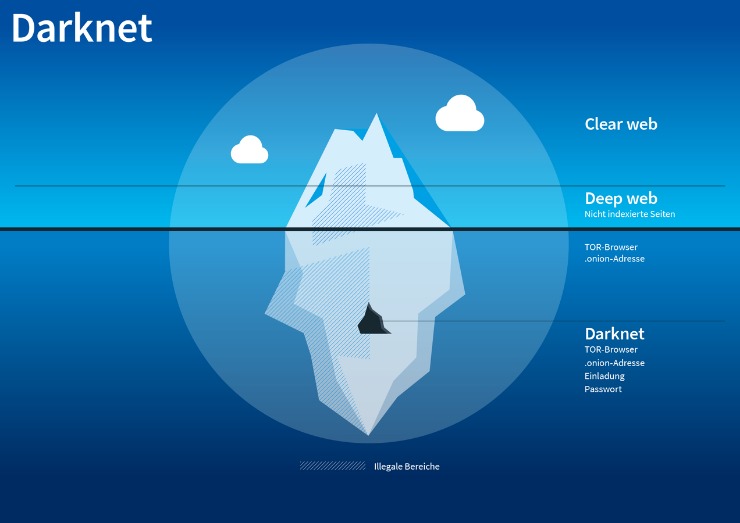
According to the most recent survey on the use of technologies that enable access to the Dark and Deep Web, India had the highest percentage of users at 26%. Russia was second, with 22% of local netizens saying they have used tools like Tor to access the Deep Web. Brazil (21%), Indonesia (20%), Turkey (16%), South Africa (16%), and Sweden (16%) all made the top five. At 10%, the US ranked 11th — the same as Australia, Hong Kong, Germany, and Japan. Deep Web stats from 2023’s third quarter reveal that Iranians made up 24.44% of Tor’s bridge users, while people from the United States accounted for 15.08%.
The main types of dark web intelligence components are solutions and services. A solution refers to a platform or service that provides organizations with the ability to monitor and analyze the dark web for potential threats and vulnerabilities. It can be deployed in several modes, including on-premise and in the cloud. According to crypto tracing firm Chainalysis, darknet marketplaces are suffering their largest consolidation in at least five years.
Access Our Free Web-based Dashboard Or WordPress Plugin
Install anti-virus or other anti-malware software on your personal computer to scan for malware. However, if a hacker gains access to the unsecured network you are on, they can easily view your account details and steal or modify your information. There is no shortage of methods to get hacked, but there are just as many ways to defend against it. By following these suggestions, you can deter unwanted intruders from accessing your accounts at home or work. Some of these bills have a guarantee that they can pass a UV pen test. Usually, these especially high-quality fake banknotes cost buyers around 30 percent of their face value.
Sales Intelligence Global Market Report 2025
Major companies operating in the dark web intelligence market are focusing their efforts on introducing intelligent and advanced solutions, such as virtual machines, to gain a competitive edge in the market. A virtual machine is a software-based copy of a physical computer that allows investigators and cybersecurity professionals to access the dark web in a secure and isolated environment. It provides a secure way to access the dark web, allowing investigators to generate a virtual machine directly from their internet browser without the need to install any software. The growing need for cybersecurity is expected to propel the growth of the dark web intelligence market going forward. Cybersecurity refers to the practice of protecting computer systems, networks, programs, and data from digital attacks, damage, theft, or unauthorized access. Cybersecurity is essential in dark web intelligence to protect against unauthorized access, secure sensitive information, and prevent potential cyber threats that may arise from monitoring activities on the dark web.
So, if the keypad jiggles around a bit, or if you notice the keypad is off-center, stop using it and contact the bank. As in most of the products listed this year, prices fell or barely held their value. Easy availability and low accuracy make data from email dump notoriously cheap.
In Q1 Of 2023, Verified Crypto Exchange Accounts Sold For As Little As $70
- Compromised voter databases combined with other user data can help malicious actors craft effective propaganda.
- Some use them due to privacy concerns, such as journalists talking to informants or whistleblowers, while others may simply want to protect their confidential information from observation or tracking.
- Both K9 and M30 were mostly found in Darkbay, within 384 listings in the year 2020, whereas Lean appeared 141 times in Empire listings.
- We’ve gathered statistics about what you can buy on the Dark Web and for how much to create this Dark Web Price Index for 2025.
Like most of the markets, STYX supports Bitcoin (BTC), Monero (XMR), and other crypto tokens to keep everyone’s identity hidden on this marketplace. But not everything is that terrifying, as Deep Web facts show that only 6.7% of Tor’s daily users engage in illegal activity on the Dark Web. The vast majority rely on the Deep Web and the Dark Web to provide them with freedom and anonymity while browsing the internet.
How To Spot Fake Weed?

On the dark web, even a minor slip-up can cause you big consequences. So, you need to be extremely cautious because the fake sites are often very similar to the real ones, making them dangerously convincing. Drug dealers can sell to customers across the world, not just locally. This expanded reach, combined with anonymity, only makes it easier for them to grow their operations without getting caught immediately. Surprisingly, most guns on the darknet actually start as legal products. The UNODC (United Nations Office on Drugs and Crime) maintains that almost all firearms are originally manufactured through legal means.
Man Charged In US For Running ‘Monopoly’ Darknet Drug Market
Dark Web marketplaces are much like ecommerce websites on the Surface Web, but with one major difference — they mainly sell illicit and/or illegally obtained goods. These include stolen login credentials, credit card details, medical records, and cryptocurrencies. According to the latest available data, Dark Web marketplaces have at least half a million users with more than 2,400 sellers. In all, these marketplaces have recorded over 320,000 transactions, with more than 4,650 Bitcoin and 12,800 Monero — the go-to Dark Web cryptocurrency — transferred.
- Fraudsters in possession of a hacked PayPal account can also try to double their money by using the account funds to run various well-established chargeback scams on merchants who accept PayPal.
- This indicates that hacking such accounts still remains extremely profitable.
- At DeepDotWeb, an anonymous editor chronicles everything darknet related, from the latest in cryptocurrencies to the rise of fall of new darknet markets.
- The dark web market predictions and review are part of KasperskySecurity Bulletin (KSB) – an annual series of predictions and analyticalreports on key shifts within the cybersecurity world.
- They even have a Telegram channel to provide their clients with live updates.
Credit card transactions on your statement which haven’t been made by you are worrying enough, but imagine logging into your online bank account and seeing your balance has been wiped clean. Unfortunately, this is happening more frequently as banking login data is being sold on the dark web. Moreover, demand for the login credentials of other online services such as Netflix, HBO Max, and Hulu has increased, leading to an influx of information for sale on the Dark Web. Over the past few years, the availability of information and data prices on the Dark Web has drastically risen. This is in part due to the increase in cyber attacks since the start of the pandemic. We’ve reported on many recent security attacks such as the FlexBooker, Volkswagen, and Gigabyte breaches, as well as supply chain attacks like the SolarWinds breach.
For a while, it seemed poised to be the new Silk Road—until a vendor allegedly exploited a vulnerability and made off with $6 million in Bitcoins. The marketplace abruptly shuttered soon after, taking with it all funds stored on the site. Online sleuths attempted to track the stolen Bitcoins (reportedly worth anywhere from $100 million to $220 million at the time) as the thief attempted to hide his or her tracks. In any case, Flare will continue to ensure that you’re up to date on all the new developments on the dark web and darknet markets. The cost of sensitive data to execute a range of identity fraud schemes and populate automated cyberattacks is again on the rise. For example, the per-record cost of so-called payment card “dumps”—which is full card information including magnetic strip track 1 and track 2 data—increased by 225% since 2018.
Darknet Market Price Index: 2018 Report
Experts estimate that criminals are paying $17 million to buy 720,000 pieces of data. In total, cybercrime costs the global economy about $445 billion a year. In short, a Dark.Commodity is a good or service that is actively being bought, sold, or traded in the underground economy, dark web, or within dark markets. As in traditional markets, these Dark.Commodities are assigned a unique Dark.Ticker symbol used to uniquely identify performance of a particular Dark.Commodity throughout the dark web.