
Don’t ever reveal your true identity on the dark web marketplaces because there’s a high chance of hackers and scammers misusing it. Beware of sharing your financial details on the dark web, as this can result in identity theft and your bank account amount being stolen. The ASAP is a moderate design marketplace on the dark web that offers helpful tools like mandatory PGP encryption and two-factor authentication for a safe browsing experience. Like other marketplaces, ASAP Market also requires you to register for an account.
How KELA Cyber Supports You In Darknet Monitoring And Risk Mitigation
Cybercriminals can rent or buy malware tools through darknet markets. This malware-as-a-service model allows less tech-savvy criminals to launch malware-driven cyberattacks without building the tools themselves. It also offers a comprehensive list of marketplaces, exchanges, and websites linked to fraudulent activities, helping you stay informed. From information security threats like identity theft and malware to scams and surveillance, navigating the dark web without caution can lead to real dangers. So, is the dark web a lawless underworld or a misunderstood frontier for privacy and free expression?
What You Can Buy On The Darknet Markets

One of the most well-known technologies enabling darknets is the Tor network, which was developed by the U.S. Naval Research Laboratory in the mid-1990s and later released to the public. Tor, short for “The Onion Router,” routes internet traffic through a global network of volunteer-operated servers to anonymize a user’s online activity.
Obtain Verified Abacus Onion Links
It relies on P2P connections and requires specialized tools and software. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship. It works by sending internet traffic through volunteer-operated nodes all over the world. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites.
Mixo Exchange: Fast & Anonymous Exchange
- However, based on preliminary estimations, the equivalent products on the surface web appear to be advertised for a multiple of the prices found for darknet markets.
- Like regular browsers with domain names, the Tor browser also has its own domain designation.
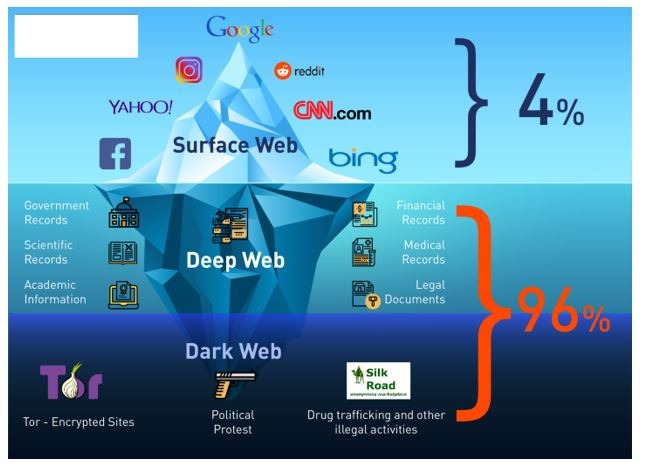
- Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word.
- Tor Browser masks your IP address and routes traffic through multiple servers.
Social platforms buzz with anonymous conversations, even as law enforcement hunts through digital shadows to crack down on criminal rings. The dark web is a murky part of the internet that isn’t accessible via a normal browser — and can be dangerous to visit if you don’t know what you’re doing. We’ll show you how to access and browse dark web sites, and how using a VPN to encrypt your connection can help you visit the dark web more securely. As well as phishing scams, a multitude of other scams operate across the dark web.
Exiting Safely
Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments. Additionally, you can opt for Subgraph OS as a second option to Tor. The early version of Tor was created to mask spy communications. In due course, the framework was remodeled and made public as a secure browser. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy.
DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content. It can also reside in web archives, non-HTML pages, and so forth. Anything hidden makes most people curious to know what’s inside. That’s exactly what happens when it comes to the dark web marketplaces. If you’d like to use it to exchange currencies, please feel free.
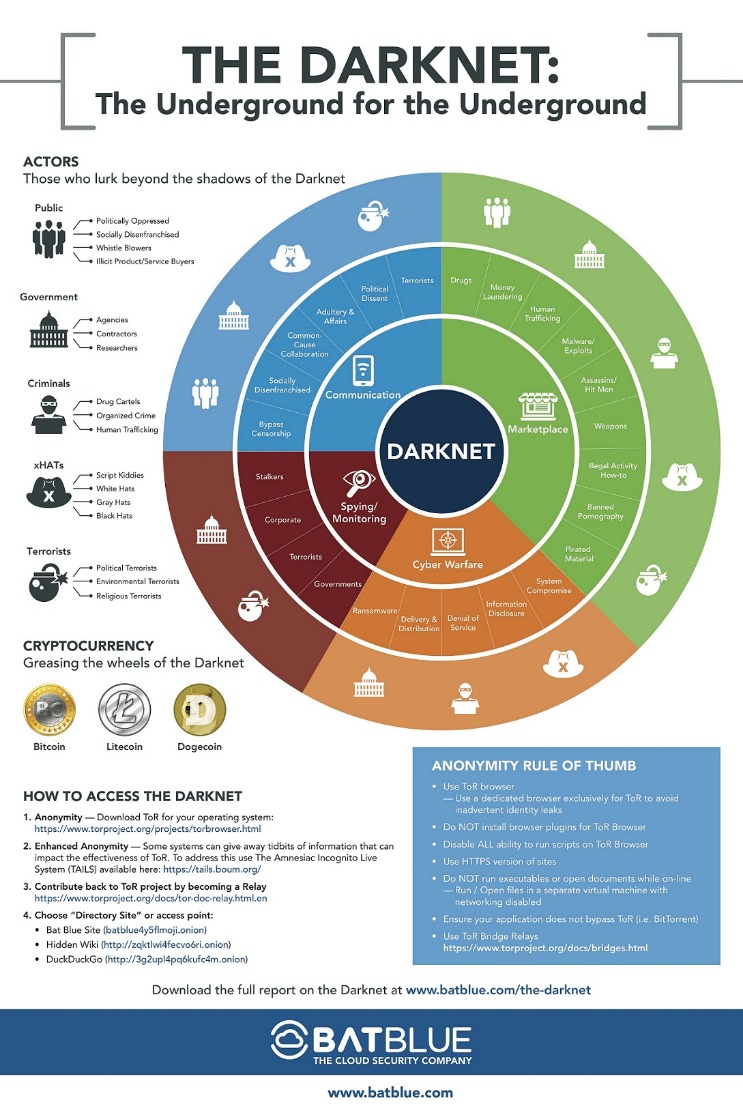
Therefore, it’s almost impossible for authorities to track those who run the darknet markets or even their locations. With Tor installed, you’ll next need to find a darknet marketplace domain to visit. The Tor network mandates that Tor clients (such as the Tor browser) can only access sites using the .onion TLD. However, these domains are not easy to distinguish, and are usually represented in long, often randomly generated alpha-numeric strings.
More Ways To Stay Safe On The Dark Web
Especially if you have a buyer account with little history (few orders). Using a virtual private network (VPN) is highly recommended to ensure your online activities remain anonymous. A VPN encrypts your internet connection and masks your IP address, making it difficult for anyone to track your location or monitor your online behavior. Choose a reputable VPN provider that does not keep logs of user data. LifeLock Standard helps safeguard your personal information, accounts, and identity. Hacking and cybercrime forums on the dark web are spaces for newbie hackers to ask questions, veteran cybercriminals to share their expertise, and buyers to find sellers.
It’s for the good that these sites are not available for the general internet user. Because it’s a members-only platform, you’ll need to register first. Thankfully, you don’t need to use your official name or email; just use a fake username (we tested it successfully). The site doesn’t require an email verification, though it offers all the features and security that you want in a dark web marketplace. When you access this site, do so with extra protection, even if you are technically anonymous when you use the Tor browser.
There are some websites you can absolutely get in legal trouble for even visiting, so proceed with the utmost caution. Most e-commerce providers offer some kind of escrow service that keeps customer funds on hold until the product has been delivered. However, in the event of a dispute don’t expect service with a smile. Every communication is encrypted, so even the simplest transaction requires a PGP key. The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below.
Deep Web Radio is a digital station with a wide variety of music. It allows you to search for images, maps, files, videos, social media posts, and more. It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications. Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge. It contains millions of scientific research documents from around the world. The site seeks to liberate information by making it free to individuals and institutions.



