
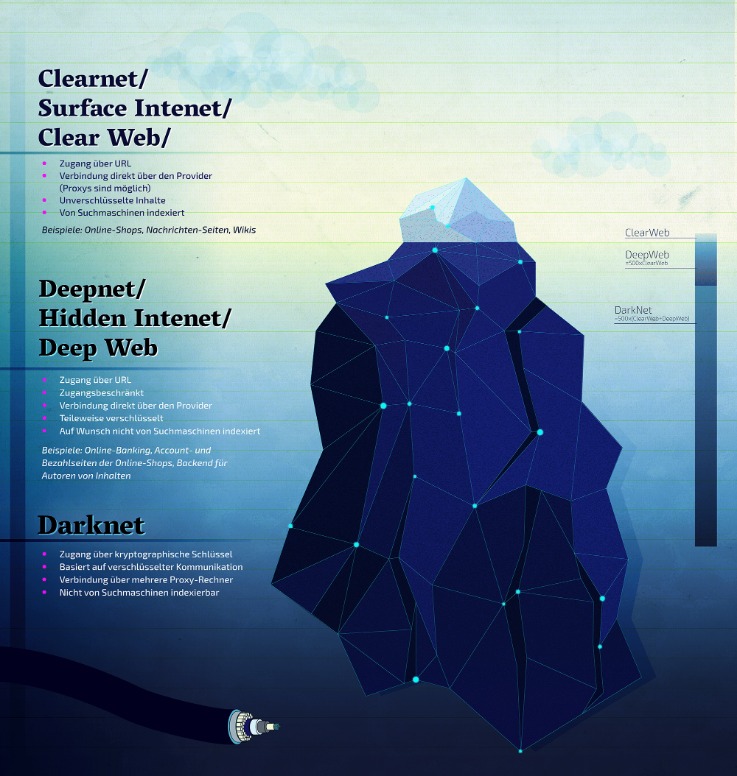
This ensures credit reporting agencies will not provide your credit report if anyone tries to open a new loan or credit card account in your name.6. Add additional challenges for financial accounts and mobile providers wherever possible. Darknet markets — also known as cryptomarkets — provide a largely anonymous platform for trading in a range of illicit goods and services. Accessing the dark web can only be done using specific browsers, such as TOR Browser.
How To Protect Your Personal Data Online
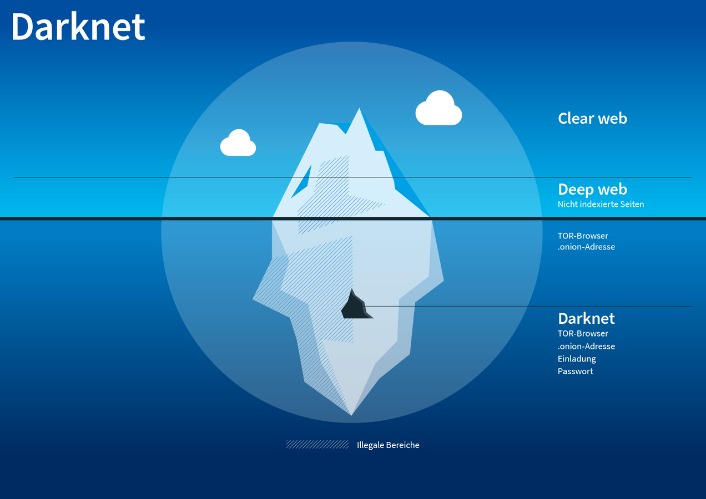
While hiring a hacker might sound like something out of a movie, it’s a very real threat. Businesses may use these services to sabotage their competitors, while individuals may seek revenge or simply want access to private information about someone. The dark web is designed in such a manner that it hides the identities and locations of its visitors. This extra privacy makes it much harder for authorities to track down who runs these markets and where they are located. For these reasons, most of these stores naturally like the dark web due to its protection.
Understanding Tor Hidden Services

The year 2023 has seen dark web marketplaces, like the MGM Grand Market, emerge as potential platforms for non-traditional services, including wedding photography. This trend raises questions about the viability and ethics of offering traditional services in such unconventional spaces. While the anonymity and digital nature of these platforms can be appealing, they also bring challenges such as legal ambiguities and the risk of associating with illicit activities. Darknet markets facilitate transactions for illegal goods and services.
How To Access The Dark Web: Step-by-Step Tutorial (and A Few Words Of Caution)
By following these steps and exercising caution, you can safely explore darknet markets on Reddit and engage in discussions with like-minded individuals. Remember to always prioritize your safety and security when accessing these underground communities. Drughub Market specializes in pharmaceuticals with 15,000+ listings, holding a 10% share of the drug trade and $2M monthly volume. Overall, dark-web marketplaces inherently involve substantial risk, and users must thoroughly understand these threats. Although dark-web marketplaces utilize technologies like Tor and I2P to enhance anonymity, these methods are not foolproof.
- Its design is simple and practical, with basic filters, seller ratings at 4.4/5 from 30,000+ reviews, and a no-fuss layout that bets on reliability over looks.
- Next, specify the destination folder (usually Program Files by default) then select install.
- Users access these sites via the Tor Browser, which conceals their identity and location.
- Generate a unique key pair, share your public key, and verify vendors’ keys via their profiles.
Dark market URLs are a crucial aspect of the deep web, a part of the internet that is not indexed by search engines and requires special software to access. These marketplaces are often used for illegal activities, such as buying and selling drugs, weapons, and stolen data. In this article, we’ll take a closer look at dark market URLs, how they work, and what you need to know to stay safe. The Dark Web—a hidden part of the internet accessible only through specialized software like Tor—has become increasingly significant as we enter 2025. It was quite popular for selling a wide range of products and services.

How Do I Dispute A Trade?
Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection. A VPN hides the fact that you’re using Tor, which is blocked in some countries and always raises doubts because of its criminal reputation. Updated February 27, 2025
Scams And Fraud

The darknet is used for anonymous communication, accessing censored information, and protecting privacy. Journalists and activists use it to communicate securely in oppressive regimes. You can access it for legitimate purposes like whistleblowing and freedom of expression. However, it’s also used for illegal activities like drug trafficking, weapon sales, and stolen data trading.
It’s not a secret that ISPs (Internet Service Providers) and the FBI are tracking Tor users. Obviously not all Tor users, but you never know whether someone might be looking into you. The dark web is a decentralized web, which means that the data is stored on many different servers around the world.
What Is The Main Cryptocurrency Used On The Dark Web?
Market is very similar to Hydra, with the market’s logo on the top left, search bar in the center, and image-linked vendor shops arranged in a table on the main page. To access the marketplace on the Tor network and view vendor’s offerings, market visitors must solve a number and text-based captcha. Hydra also featured numerous vendors selling false identification documents. Users could search for vendors selling their desired type of identification document – for example, U.S. passports or drivers’ licenses – and filter or sort by the item’s price. If you browse the dark web using the Tor Browser, your IP address will be hidden from the sites you visit.
The categories are well organized, ranging from drugs and fraud to digital products, guides, and malware.What really sets it apart is its focus on security and usability. It supports PGP encryption, two-factor authentication (2FA), alerts against fake sites (antiphishing), and a verification system for sellers. Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero. All of this has made it one of the most reliable markets still active in 2025. Incognito Market sits at #4 in our 2025 darknet rankings, carving a niche as a privacy-focused trading spot in the anonymous world. Starting in June 2022, it’s grown steadily to 20,000+ listings and $2.8 million in monthly trades through BTC and XMR, holding a 5% share of the darknet scene.
Its 99% escrow success rate resolves disputes in 24 hours for 95% of cases, securing its 20% market share. Incognito leads with mandatory 2FA for its 10,000+ users, introduced post-2023 phishing, reducing breaches by 80%. AES-256 with PGP secures comms, while advanced DDoS protection ensures 93% uptime. Its 95% escrow success rate resolves disputes in 36 hours for 90% of cases, making it a privacy-first security standout in 2025.
The Tor network was created by the US military in the 1990s for anonymous communication between spies over the internet. That effort was never fully realized, but the US military published the code under a free license in 2004. Researchers from the Electronic Frontier Foundation and other groups continued its development and launched the Tor project in 2006 as a tool for journalists, activists, and whistleblowers. Many dark websites are perfectly legal and safe to use and, in many cases, are better for your privacy than clear websites. Alternatively, users can connect in opennet mode, which automatically assigns peers on the network. Unlike darknet mode, opennet uses a handful of centralized servers in addition to the decentralized peer-to-peer network.
If you want to use Tor privately, you can use either a VPN or Tor Bridges (Tor nodes that are not publicly indexed). Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable. As long as users take the necessary precautions, no one knows who anyone else is in the real world. Users’ identities are safe from the prying eyes of governments and corporations.



