
One of the most common types of illicit goods is stolen login credentials, often collected from data breaches. These “credential dumps” allow criminals to access online accounts, steal identities, and commit fraud. Even passive activity on these sites can contribute to criminal networks. For instance, buying fake documents may indirectly support larger operations involving trafficking, extortion, or organized crime.

Why You Need Automated Dark Web Monitoring
Ethically, they must minimize harm, responsibly handle any stolen or sensitive data (often notifying victims or law enforcement), avoid entrapment, and maintain research integrity. Sometimes, you might be hacked by using weak passwords or even just connecting to unsecured Wi-Fi on public networks. And in a world where almost everything we do is online, taking your digital privacy seriously is more important than ever. First things first, always use strong and different passwords for each account you open. But these efforts of law enforcement don’t go in vain; hackers and criminals lose trust if a website or marketplace goes down. On the dark web, you don’t need to be a technical expert to design ransomware, and that’s dangerous.
How To Avoid Phishing Scams And Malware Threats
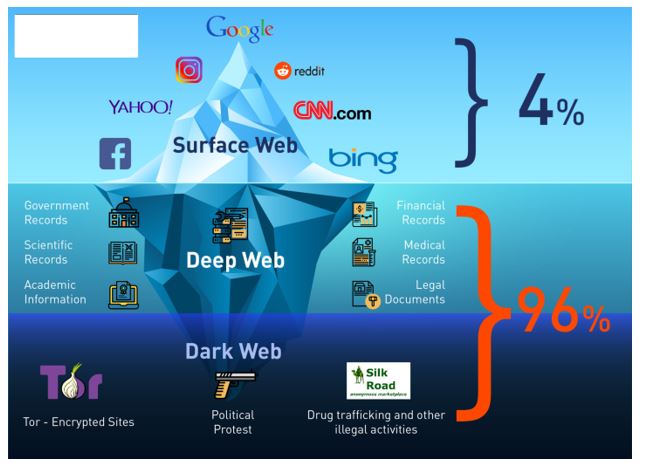
Google considers the majority of the content on the entire web highly irrelevant and useless to its users. That’s why such a large percentage (as much as 94%) of the entire web is not returned in Google Search. First, in the USA, it is a federal offense to use the USPS for any of these transactions. If the buyer or seller gets caught, there are significant legal ramifications. The .onion top-level domain (TLD) name is the dark web’s version of “.com” or “.net”. Unlike traditional TLDs, servers using the onion TLD are more difficult to locate.
I2P uses one-way tunnels, so an eavesdropper can only capture outbound or inbound traffic, not both. The big downside is that your ISP will know you are using Tor, which is cause for concern in some places and will put many people off using this method. In this instance, too, it is important to use a logless VPN and pay with Bitcoin if you can to stay anonymous. The VPN over Tor technique is also susceptible to an end-to-end timing attack, though it’s highly unlikely. If you want to use Tor privately, you can use either a VPN or Tor Bridges (Tor nodes that are not publicly indexed). Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable.
Why Using Trusted Directories And Security Tools Is Important
- It has built a reputation for being a reliable source of stolen credit card data and PII.
- As stated above, we don’t condone any activity—on the dark net or otherwise—that is forbidden by law.
- Now that you understand what the dark web is all about, you might wonder why other people do things on it.
- This is an excellent way for Dark Web users to provide additional privacy protection when accessing the Dark Web.
- The website has a sleek design and interactive user interface, making it the most preferred choice in terms of user experience.
- Fortunately, on July 22, 2025, French police reported arresting a key XSS administrator after a long-running investigation, and the forum was seized.
They take BTC and Monero, with multi-signature escrow and global shipping—vendors swear by it, and I’ve snagged rare stuff (think DMT or niche scripts) without a hitch. Drugs lead the pack—weed, pills, some synthetics—but digital goods like hacked logins are gaining, tying into Telegram’s side gig boom. For 2025, they’re teasing AI-powered search—could make digging through listings a breeze, which I’m hyped for since their catalog’s already hefty.
How To Access Verified Dark Web Sites
Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement.
The only way in is through the use of special software that renders all users anonymous and untraceable. Imagine an underground version of your favorite online marketplace, somewhere hidden, exclusive, and often operating outside legal boundaries. It is similar to an online store, except it’s not the type you’ll find with a quick Google search. These marketplaces are full of risks (security, legal, ethical issues – all of them). But if you still decide to access these websites, for education or research purposes, make sure you stay cautious.
The Top 10 Darknet Marketplaces Of 2025
- Discover how to explore darknet market links safely while ensuring your privacy and security.
- Your real information could be exposed at these nodes, allowing third parties to intercept your dark web activity.
- Onion sites can be safe in terms of privacy protection due to strong encryption, but they also host a significant amount of illegal content and scams.
- Tracking vendor migration—such as from Archetyp to Exodus—provides insight into tactical shifts.
- It can only be used to access the content uploaded to the Freenet, which is a peer-to-peer distributed data store.
- This secure setup is useful for those who want to avoid government surveillance or keep their personal information safe from online threats.
It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. The dark web market changes all the time, but some dark web marketplaces have made a name for themselves as the biggest and busiest spots. These sites attract thousands of users every day, offering all kinds of illegal goods that keep the underground trade going.
The Dark Web: Risks And The Role Of Standards

One notable fact is that the site has changed its domain twice since its formation. Today, Exodus Marketplace works from 3 different domains, two of which are its mirrors. It offers outstanding privacy features and is currently available at a discounted rate. This information can be used to target ads and monitor your internet usage. Second, shutting down or controlling access to the dark web would be a huge undertaking and could have unintended consequences. Finally, many people consider the dark web a necessary tool for privacy and freedom of speech.

There’s more to it than just sharing things such as hacked databases, stolen credentials, exploits, or hacking tools. Moreover, they’re home to hot-red forum rivalries, frequent doxxing attempts, and in-depth dark web discussions among other threat actors. XSS (formerly known as DaMaGeLaB) was one of the longest-serving forums in the deep web. It was a dominant forum that featured a dangerous threat for average users within the Russian-speaking cyber environment. It had a surface web mirror alongside an onion site that users accessed using the Tor browser.

The controlled and professional landscape has led many people to view the forum as the most reliable source. Exploit.In is one of the most visited (and notorious) dark web platforms from long ago, which operates in a Russian-speaking landscape. It’s a major threat to monitor as it operates on both the Tor and the surface web, which makes it accessible from several fronts. If you want to improve your security further, you could also use a VPN at the same time as Tor. For the most security-conscious, you can even install the Tails operating system on a flash drive and run Tor from that. However, any illegal activities conducted on the dark web, such as purchasing illicit goods or engaging in criminal behavior, are still punishable by law.
The market is especially well-known for providing access to freshly compromised data, often obtained from recent breaches and stealer logs. This platform has rapidly become a key player in the fraud market, trading in PII and SSH credentials while making use of both the clear and dark web. In 2022, for example, BidenCash was linked to the breach of over 1.2 million credit card records. FreshTools, founded in 2019, specializes in selling stolen account credentials and data, particularly webmail, RDPs (Remote Desktop Protocols), and cPanels. Its user base is primarily English-speaking, and it appeals to more sophisticated cybercriminals.



