Because it uses direct-pay checkout (no site wallet), users never pre-deposit coins, reducing exit-scam risk. Cybersecurity companies and researchers monitoring darknet markets face legal and ethical restrictions. Legally, they are limited to observing publicly accessible areas using tools like the Tor browser, without engaging in unauthorized access or illegal transactions. STYX MarketSTYX Market, launched in 2023, is all about financial crime. It offers access to hacked bank accounts, credit card data, and cryptocurrency laundering tools. Transactions can be made using Bitcoin or Monero, and the platform keeps users in the loop through an official Telegram channel.
Darknet Credit Card Market
- In addition, mainstream search engines also track your searches and collect personal information.
- It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users.
- To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network.
- For operations security he suggests avoiding storing conversation logs, varying writing styles, avoiding mobile phone-based tracking and leaking false personal details to further obfuscate one’s identity.
- Abacus alone represented nearly 5 per cent of total DNM revenue, underscoring the ongoing scale of underground commerce.
It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime. In 2025, darknet marketplaces primarily accept Monero (XMR) and Bitcoin (BTC).
How To Create A Darknet Market

Track and analyze darknet activities using our advanced cyber threat intelligence platform to stay ahead of emerging threats. Ethically, they must minimize harm, responsibly handle any stolen or sensitive data (often notifying victims or law enforcement), avoid entrapment, and maintain research integrity. One of the most common types of illicit goods is stolen login credentials, often collected from data breaches. These “credential dumps” allow criminals to access online accounts, steal identities, and commit fraud.
Darknet Market Guide Reddit
Here are some of the now-defunct dark web markets that were notorious for cybercrime. WeTheNorth is a Canadian market established in 2021 that also serves international users. It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process.
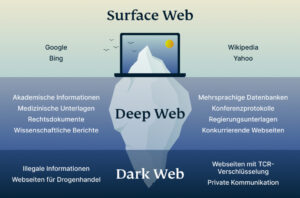
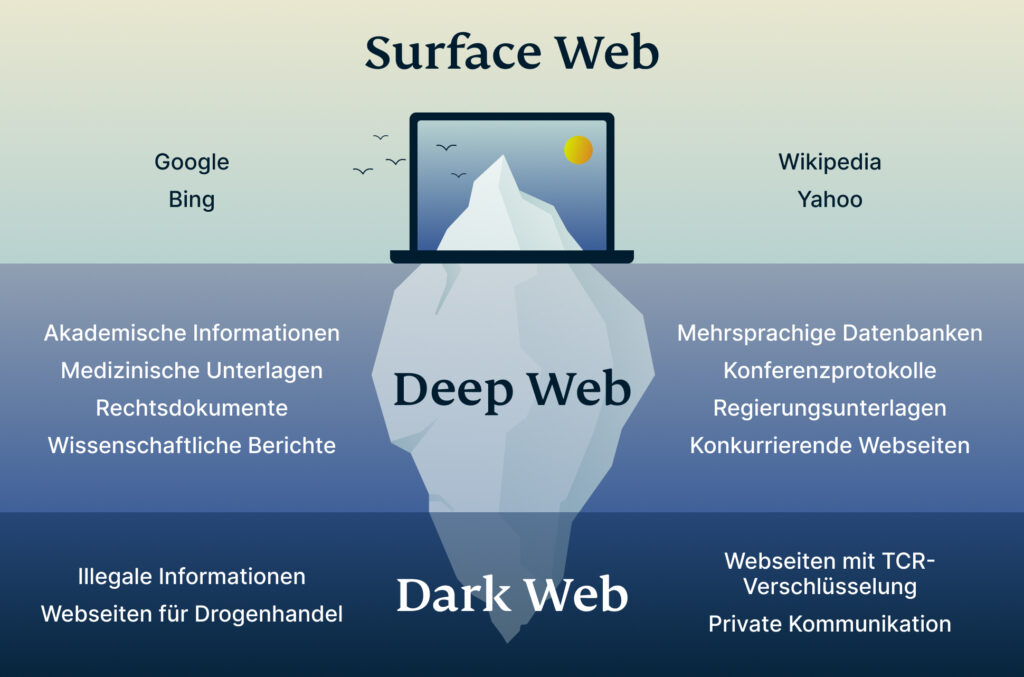
How Is The Darknet Different From The Deep Web?
Know all about Dark web its dangers and how to access it with sale of black market drugs, sale of illegal firearms, illegally acquired users’ database. World Indices Live Complete world stock market coverage with breaking news World Stock Markets Mar 18, 2021 World Market is a new dark net market that. Sometimes the data is used by the entity that carried out the hack, like a ransomware attacker.

STG Energy Cloud Mining Platform: The Wealth Engine For Bitcoin And Solana Investments In 2025
As long as people want to buy and sell illegal stuff online, be it stolen data, narcotics, drugs, or malware, these markets will keep resurfacing, no matter how many times authorities take them down. In total, there were 2,158 vendors who advertised at least one of the 96,672 product listings across the 30 marketplaces. Vendors and product listings were not distributed equally across markets. On average, marketplaces had 109 unique vendor aliases and 3,222 product listings related to stolen data products.
The browser uses onion routing technology to route the internet traffic through multiple relay nodes that provide layered encryption. The layers of encryption hide your data and activity from snooping eyes. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement.
Abacus had recently grown in dominance after Europol’s June takedown of Archetyp Market, handling $6.3 million in monthly sales and controlling over 70% of Bitcoin-enabled Western darknet trade. Before implementing any strategies, you need to seek proper financial, legal and accounting counsel. A handful of markets were responsible for trafficking most of the data. Learn effective strategies for conducting threat hunting in your organization. The MITRE ATT&CK framework provides a comprehensive view of adversary tactics.
Most Popular Darknet Market
For starters, dark web traders can use their access to financial data to identify and capitalize on potential discrepancies between the current market price and the future price of a given asset. Through the use of software programs and custom algorithms, traders can analyze patterns and determine whether or not there is an opportunity for profit. Additionally, by understanding how certain companies’ stocks move, traders can use their insights to trade in a more informed manner. Insider trading has long been a topic of interest in the world of finance, but many are unaware of the potential uses of dark web insider trading.
The History Of Darknet Marketplaces
Für das bandenmäßige Handeltreiben mit Betäubungsmitteln in nicht geringer Menge sieht das Strafgesetzbuch einen Strafrahmen von fünf bis 15 Jahren Freiheitsstrafe pro Tat vor! In this work, researchers directly engaged in 344 transactions with different services including mining pools, exchanges, dark markets and gambling websites. Da ein internationaler Handel mit kriminellen Gütern stattfand, bezahlten die Kunden ihre Ware mit Bitcoins oder Monero.
What Are The Risks Associated With Dark Web Insider Trading?
The quantity, price, and characteristics of the product are all provided. However, the platform lacks an advanced search option and a wallet-free payment option. The ASAP is a moderate design marketplace on the dark web that offers helpful tools like mandatory PGP encryption and two-factor authentication for a safe browsing experience. Like other marketplaces, ASAP Market also requires you to register for an account. If any user is found not complying with the law, strict and immediate action will be taken against them.
Tor2door Market
Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. Then, you can set up 2FA (two-factor authentication) for that extra touch of security in case someone somehow figures out your password. If you ever have to connect to public Wi-Fi, make sure to use a VPN to keep your browsing safe and private. However, the dark web is so complex and vast that if law enforcement takes down one market, it pops up elsewhere.
Who doesn’t like privacy, especially when dealing with the buying and selling of illegal products and services? Therefore, given the nature of anonymity and privacy of the dark web, several stores keep on emerging in the dark despite a continuous crackdown on several others. Discover everything about what is a darknet market, how it works, security threats related to it, and learn how to protect your data online. In exploring the top 10 dark-web marketplaces in 2025, we’ve examined their core operations, diverse use-cases, inherent risks, and evolving trends.
It uses PGP encryption to protect sensitive data and messages, and accepts payments via Monera and Bitcoins to keep you anonymous on this marketplace. The vendors aren’t required to register or apply for a vendor account while using this platform. It ensures the buyer’s identity is kept hidden and accepts payments through cryptocurrencies, including Bitcoin, Litecoin, Ethereum, and Monero. Another dark net marketplace that has grabbed a lot of attention is the Hydra market.
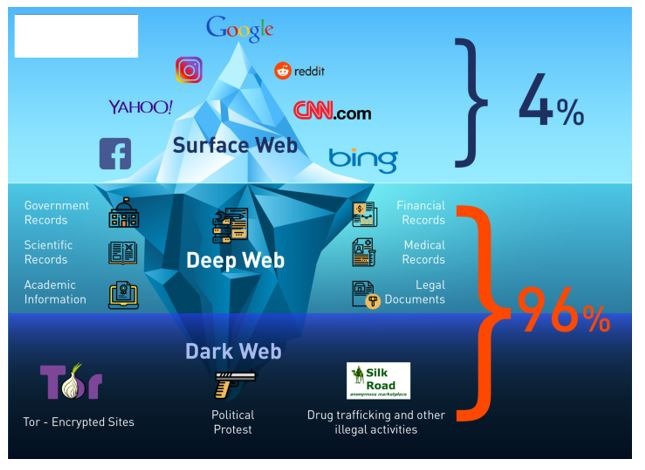
Therefore, you can hire them to perform a task for you, from planting malware to hacking email accounts and even breaking into various social media accounts. The dark web is only accessible through specific software like Tor (The Onion Router). Also, while this huge portion of the internet has a reputation as home to nefarious activities like hacking and drug trafficking, it also harbors legitimate activities like journalists and whistleblowers. The internet is a wide landscape that comprises the surface part – the internet that we all know and the hidden portion. The hidden part of the internet is the larger portion that features over 95% of the entire internet.