Monero is a crypto currency that can be used to conduct transactions anonymously on a peer to peer level without any centralized authority watching over.. The topics you can find vary from literature, programming, science, and….artistic photography. Bear in mind that downloading materials from this site may put you in violation of local copyright laws, so exercise caution should you decide to do so.
Do I Need A VPN To Access The Dark Web Using Tor?
These terms are often confused or misused, but they describe very different layers of the Internet. The dark web offers a fascinating glimpse into a hidden world, but navigating it requires vigilance. For beginners, this guide sets the foundation, and for further exploration, check out our Top Darknet Markets to dive deeper into this ecosystem. We’ve compiled a detailed guide to help you explore the Top Darknet Markets. Discover the most trusted platforms like Anubis Market, and more, complete with their unique features and security measures. In today’s digital era, where information is constantly on the move across all digital platforms, an…
What Is Tor And Why Is It Called “The Onion Router”?
- Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down.
- What’s more concerning is that most of the time, we don’t know about these flaws, and by the time we try to fix them, we come to know it’s too late.
- It is important to verify that the application is indeed published by “The Tor Project, Inc.” to avoid installing potentially malicious imitations.
- Search engines on the dark web are a bit of a contradiction because dark web sites by definition are not indexed by traditional search engines.
- The dark web is designed in such a manner that it hides the identities and locations of its visitors.
It might be because of the poorly maintained site or Tor’s slow speed because of the way it works. Either way, some sites take up to a minute or more to load, so don’t fret. If you’re prompted to connect, click the purple “Connect” button and wait for a few seconds. We already know of one necessary component needed for this – Tor. However, while Tor is great, safe, and whatever you think, it’s not as great as another component – a VPN.
Since your traffic goes through a series of relays, getting encrypted or decrypted along the way, things slow way down. This means Tor is a lousy option for streaming video, online gaming, or downloading files (torrenting). The United States Naval Research Laboratory developed the technological framework for Tor in the mid-1990s. The Onion Routing project, which became Tor, introduced a publicly available version of the software in 2003. Three years later, a not-for-profit research education organization, The Tor Project, was established to manage the network. The enhanced security and anonymity provided by Tor does come at a cost to the end user.
Stay Safe
Many mainstream media organizations monitor whistleblower sites looking for news. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The experience is reminiscent of searching the web in the late 1990s. Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query. Link lists like The Hidden Wiki are another option, but even indices also return a frustrating number of timed-out connections and 404 errors. By following these straightforward steps, you significantly reduce the risk of exposure, protect your digital identity, and ensure a secure and anonymous browsing experience on the Dark Web.

Can Commerce Students Do Cyber Security Courses? A Complete Guide
The dark web, which is what I’m discussing here, is a small subset of the deep web, and refers to websites that are specifically trying to stay out of sight. Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship. By rigorously following these best practices, you can significantly enhance your privacy and security when accessing .onion links and mirrors, ensuring safer and more anonymous experiences on the dark web. According to LMG Security, over 2.7M people have visited the dark web in 2023. What’s more alarming is the estimation that the HALF of those visitors were connected to illicit activities.
Popular Posts
According to Tor, on average about 2.6 million “clients” (users) directly connect to its network each day. Legitimate uses include sensitive communications and law enforcement investigations. Controversially, it is also used to distribute malware, defame individuals, and facilitate illegal activities on the dark web. There are other ways for spies, hackers or other adversaries to target Tor. Lewis points to the “first contact problem”, when an attacker spots when someone moves from non-private tools to private ones, noting it’s been used to identify whistleblowers.
Use A Dedicated Browsing Machine
And yes, unfortunately, those seeking to perform criminal acts also use it. Tor uses an open-source browser that routes data through encrypted layers via nodes, masking the sender’s IP address. Only the first and last nodes can reveal the sender’s identity and message content. VPNs are often recommended as protection in such cases, but Whited disagrees.
onion URL Structure
When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked. These tools scan dark web forums and marketplaces for any signs of your compromised credentials. There is no need to visit darknet marketplaces yourself to know whether your data was leaked. Monero and Bitcoin are two of the most commonly used digital currencies on the dark web markets. Due to being the most popular and the oldest coin, Bitcoin is traceable.

More Ways To Stay Safe On The Dark Web
To reinforce your privacy while on the dark web, consider adding on a VPN like Windscribe as an extra layer of protection. SimplyTranslate is an onion based language translation service using the google translate engine. It’s an easy and simple way to de-couple your internet usage from Google’s monopoly over the web. Without further ado, let’s take a look at some of the best tor and onion links for you to check out, in no particular order. CiviCRM, an open-source software used by the Tor Project to manage donor data and communications, offers full system control to handle donor data securely with confidence. To turn it on, just go to the “Settings” and then the “Tools” section of the NordVPN app and activate “Dark Web Monitoring.” In the end, it’s all about staying one step ahead.
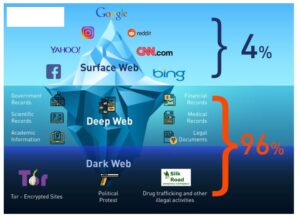
Another reason the Russian Market is so popular is that it’s pretty inexpensive compared to other dark web marketplaces. As noted by Andy Greenberg at Wired, while the deep web makes up approximately 90% of the internet, the dark web makes up only around 0.1% and is designed to provide anonymity for users and site owners. While this is good advice for any type of web browsing, be particularly careful not to offer up any personal details, such as your credit card info or email address. Use cryptocurrency to buy anything, and use a disposable email address for any type of communication on the dark web. Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website.
Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. Onion links have no regular domain names registered under the domain name registry. Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser. Hence, you never know when a popular .onion site is going to vanish, or even die. Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). The best thing is to actually understand how to find the fresh, new links.
It works by first using a VPN and connecting to Tor afterward, hence its name. Just for laughs and giggles, we visited this random pug’s ultimate guide to the dark web. You’ll notice that some websites’ loading times are longer when using Tor. If you don’t know where to start, you can use The Hidden Wiki to find a few dark web domains. Simply copy the URL of the site you want to visit, press Enter, and you’re all set. On top of that, Tor’s nodes can also malfunction because they’re owned by volunteers, which will expose your traffic and sensitive information.