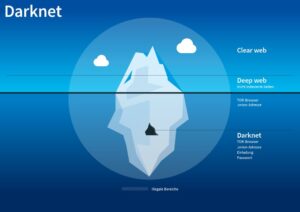
Your activities on the dark web are not entirely shielded from tracking, and relying solely on anonymity can lead to a false sense of security. The dark web draws not only serious cyber criminals but also law enforcement agents aiming to catch them. Many exit nodes are actually operated by law enforcement and scammers. All you need to do is click connect and you are officially connected to the Tor network and can now access dark web websites.
Bitania P2p Platform
Tor is the most popular instance of a darknet,19 and it is often mistakenly thought to be the only online tool that facilitates access to darknets. The rise of cryptocurrencies like Monero and Zcash has further strengthened privacy, making transactions nearly untraceable. Another key player is NebulaTrade, which focuses on user anonymity through advanced Tor routing and zero-knowledge proofs. This market has also introduced AI-driven vendor verification systems, ensuring that only reputable sellers are allowed to operate. NebulaTrade’s emphasis on quality control has made it a preferred choice for buyers seeking consistent and high-quality products.
How To Access Dark Web Websites
Adamant offers blockchain-based secure messaging without needing phone numbers or email addresses. The platform stood out during my testing for its commitment to anonymity — all messages are fully encrypted and stored on a decentralized network. It’s particularly useful for sensitive communications that need to remain private. A 2014 study found that the most common type of content found on Tor, the most popular darknet, was child sexual abuse material. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked.
Unfortunately, many dark web websites are devoted to the illegal trade of leaked personal information. If you’ve ever experienced an uptick in phishing attacks and spam after a data leak or breach, it may be because your personal information has been posted to the dark web. On the dark web, traffic is routed through multiple server nodes that don’t log activity, obscuring the user’s origin and enabling anonymous communication. I personally recommend Tor over VPN because it’s the safer option — the VPN encrypts your traffic and changes your IP address, so the Tor network can’t see them.
- Many free VPN providers lack basic security features and track your online activity, so they don’t offer much privacy.
- Other options include Ahmia and NotEvil, which focus on listing .onion links.
- To do that, you’ll need a dark web search engine like Torch or Ahmia.
- Law enforcers can use custom software to infiltrate the dark web and analyze activities.
Onion Links Directory 2025
You can access it for legitimate purposes like whistleblowing and freedom of expression. However, it’s also used for illegal activities like drug trafficking, weapon sales, and stolen data trading. Law enforcement agencies monitor it for criminal activities, but legitimate users rely on it for privacy protection.
How Do Onion Sites Work?
First — and this is strongly recommended — you should install a Virtual Private Network (VPN). Also, you need to use a privacy-focused browser such as the Tor network to connect via nodes and proxy servers, which are more secure and aim to anonymize traffic requests. The Tor browser is able to access the special domain names, with the suffix .onion, used in the dark web.
Can I Access The Dark Web Without Tor?
The ethos of Hidden Answers lies in the belief that free access to information and unbridled expression are fundamental human rights. By providing a space where questions can be asked and answered without judgment or identification, the platform embodies the principles of free speech and informational freedom. However, the anonymity and lack of oversight also present challenges, such as the potential for misinformation, and illegal activities. Yippy is a search engine that started in 2009, since then it has evolved. To become a leading provider of business learning and knowledge for all types of data users and consumers. Dark markets continually adapt and evolve to stay ahead of law enforcement and security measures.
Are All onion Sites Illegal?
The Intercept is renowned for its fearless and unfiltered journalism. Its writers have been at the forefront of investigative journalism, often delving into topics that mainstream media rarely covers. That said, if ProtonMail doesn’t suit your needs, there are other Dark Web email platforms available, such as RiseUp and Mail2Tor. For example, RiseUp is an invite-only platform, meaning that you will need an invitation to use it.

This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. Today, many organizations exist that are created only to handle these reports anonymously and effectively. They know how to process the information and get it to the correct law enforcement agencies internationally. In some countries, evading government restrictions to seek new political ideologies is punishable. For example, China uses the Great Firewall to block access to Western sites. Accessing blocked content can result in being placed on a watch list or imprisonment.
More On Tor Onions

Reddit style discussion darknet forum, the main place where users migrated after Reddit banned /r/darknetmarkets. TorZon Market, launched in September 2022, supports XMR and BTC payments, features established vendors, and offers a user-friendly platform. Deep Search Engine is a darknet search engine that promotes known scams on the Tor network. Deep Search claims to be built by students who created a new powerful Tor search engine. However, keep in mind that the Tor browser is not officially available for both of these platforms. Tor’s official website recommends using the Orbot app for Android and the Onion Browser app for iPhone to access these websites.
- After that, many other marketplaces kept trying to take its place and become the top dark web market.
- One of the core features of DuckDuckGo is its commitment to not storing user search histories.
- Forums and websites on the dark web are not moderated, so you can never be sure they are free from malware.
- Never log in with your real name or reuse passwords from other accounts.
- Tor works by directing internet traffic through a global network of volunteer nodes.
I Legal And Ethical Considerations
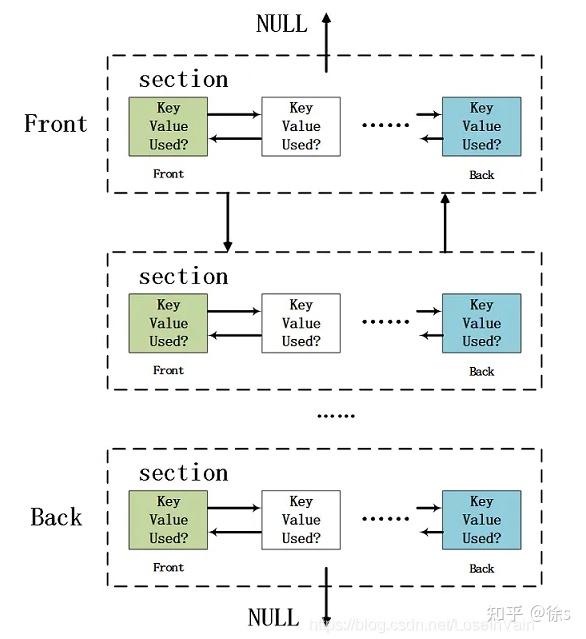
Tor is a free and open-source anonymity tool consisting of thousands of volunteer-run “nodes” around the world. When you connect to the internet through the Tor network, your connection is routed through at least three random nodes, with your data being re-encrypted each time it passes through a node. Email is one of the least secure communication systems; the email providers have access to the contents of your inbox. For evidence, look no further than the way Google automatically adds travel information, meetings, and other diary entries onto your calendar.
The archived page is then assigned a unique URL, which can be used to access the snapshot at any time, independent of the original web page’s status. This feature is especially useful for preserving evidence of web content that may be legally or historically significant. Tor Metrics is committed to transparency and the open dissemination of data while maintaining a strict adherence to privacy principles. It aggregates data in a way that does not compromise user anonymity or the operational security of the network. Sci-Hub, often referred to as a “pirate” academic database, is a groundbreaking online repository that provides free access to millions of research papers and academic articles.