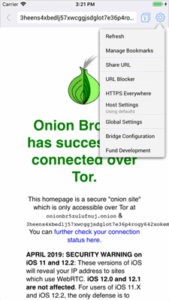
In due course, the framework was remodeled and made public as a secure browser. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction.
- In some authoritarian states, accessing Tor nodes can flag you for surveillance.
- Also, you must log in or have a specific IP address or URL to access the deep web content.
- The invisible web is a treasure trove of information, but it also harbors risks.
- However, the technology that Yippy manages, was created in Carnegie Mellon.
- ZeroBin encrypts and decrypts text in the browser, so their servers have no way of knowing what’s happening on the browser side.
Access The Dark Web Safely
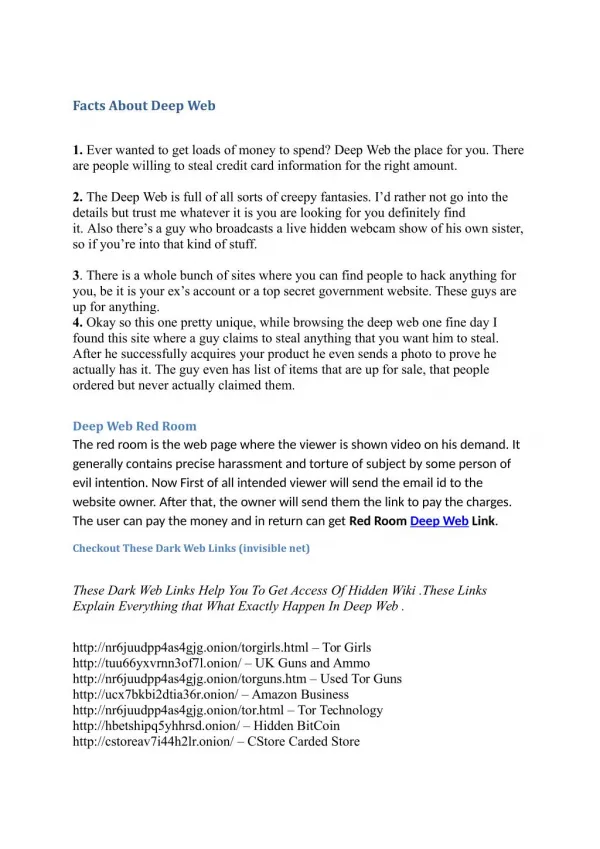
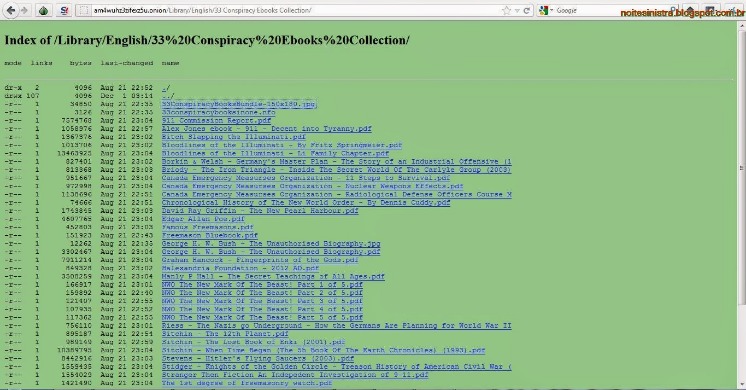
It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications. This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime. Moreover, due to its popularity, many copycats of the Hidden Wiki exist. So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful. Not Evil is a reflection of what the community is looking for and what the community reports as abusive or inappropriate content. Dark web forums are online communities where individuals participate in discussions on a wide range of subjects, from technology and privacy to more illicit matters.
Onion Links: How To Access Them
Riseup is an invite-only email and communications service that doesn’t hold onto any of the data you generate when you use it. It describes itself as a tool for social change and “a project to create democratic alternatives.” Riseup requires you to have the onion link as well as an invitation. The dark web is home to a variety of useful and legitimate resources — educational materials, encrypted email services, anonymous forums — that can’t be found elsewhere. The CIA is contactable on the dark web, providing a completely anonymous way to get in touch with them. However, if you’re communicating with state intelligence agencies, you should use Tor alongside a VPN for maximum privacy.
¿Es Ilegal Visitar Una Página Web En La Deep Web?
Even if someone intercepts the data, they’ll only see an encrypted stream between nodes – not your real IP. Unlike VPNs, Tor node operators don’t keep logs – this has been proven in court, including a major U.S. case against a hosting provider in 2022. A VPN like Surfshark encrypts your internet connection and makes it harder for others to see your real IP address. This adds another, more reliable security layer to all of your online activity.
Las Mejores VPN Para Mantener La Seguridad Y El Anonimato En La Deep Web En 2025
Crypto services use various measures to keep cryptocurrency wallets secure and make sure your Bitcoin is safe. Some, such as Wasabi Wallet, provide an extra layer of security by using onion routing to pass crypto activity through multiple nodes, none of which know the sending and receiving IP addresses. AVG Secure VPN masks your IP address from other internet users, the websites you visit, and even government surveillance. And thanks to ultra-secure, end-to-end encryption, your online activity is obscured. In a world where digital privacy feels as rare as a unicorn, the dark web offers a peculiar sanctuary. Yet, it’s not all cloak and dagger; the dark web is a complex realm with legitimate uses and potential pitfalls.
To distinguish their work from other efforts, they named the project Tor (The Onion Routing). This github page is maintained by voluteers, that makes this page get updated more often – to provide better access to information. It’s a modified Firefox that allows access to the dark web and is configured for higher security. Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal… We also made sure to select only sites that have been around for a considerable amount of time without being taken down or being the subject of any privacy or security scandals. If you wish to access the snapshots of these websites, just type in the domain name, and you will get the results depending on how many records exist on the website.
A Quick Guide On How To Use A VPN With Tor
This tool provides suggestions and enhancements, allowing you to create a polished final product. Agentic empowers you to turn abstract ideas into visually compelling presentations. By leveraging AI-driven content generation, you can create high-quality materials that captivate your audience. This feature enhances the value of your output, making it ideal for both professional and academic applications. PageOn.ai’s intelligent presentation tools ensure your content stands out, improving overall engagement and effectiveness. Another problem with this system is that there’s increasing evidence that law enforcement agencies — such as the FBI — run and operate large number of exit nodes.
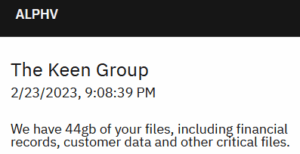
Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. For this reason, you must watch out and avoid opening anything that looks suspicious to you. Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons.
- Unfortunately, it requires you to have an invitation code to create an account.
- Many dark web links could get you mixed up in some kind of criminal activity of another, whether you’re looking for it or not.
- For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions.
- Find all the resources you need to be an Optimove expert, from online courses to technical API documentation.
- These forums are frequently accessed via the top 10 dark web search engines, serving as essential resources for information and networking.
Should I Use Services Like Web2Tor?
These lessons and guides can teach you anything from how to make a bomb to how to hack. Some of this content can be used for good reasons, such as study or teaching. As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with.
The marketplace has an intuitive interface and offers powerful search tools that make it easy for you to find products from both local and international sellers. All vendors are vetted before they are allowed to sell, so it makes sure of trust and quality. Ahmia is a safe alternative search engine for users who prefer the dark web. It also provides insights, helpful statistics, and updates regarding the Tor network. With an impressive database boasting over 122,811 listings and 7,782 vendors, Kilos provides users with a wealth of options to explore.
Your data is encrypted in the Tor browser before reaching the ZeroBin servers. Unfortunately, it requires you to have an invitation code to create an account. This means you have to know someone who is already using the platform. Even without the code, you can visit the security section to get tips on improving your daily life privacy.

NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites. It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web.
A key feature of DuckDuckGo is its strict no-log policy, ensuring user privacy. As a result, the precise number of DuckDuckGo users remains undisclosed. Nevertheless, the company estimates its user base to be around 25 million individuals. The BBC’s international edition Tor version is available on the dark web, giving access to unbiased news in regions where the BBC is blocked or censored. Feather is a free and open source Monero wallet available on most major computer platforms.

For example, some platforms may require additional settings or plugins to operate effectively. Pay attention to reviews that mention ease of use, accuracy of results, and security features. Positive feedback about these aspects indicates a reliable platform. On the other hand, negative reviews may reveal issues like indexing harmful content or poor privacy protection. Use this information to choose a search engine that aligns with your needs and ensures a safe experience on the invisible web. The modular design of AI Blocks simplifies the creation of visually appealing presentations.
Pissmail is the service for you, offering an onion based web service accessible via Tor browser. Without further ado, let’s take a look at some of the best tor and onion links for you to check out, in no particular order. While technically not an onion site, we’re including Sci-Hub (sci-hub.se) as an interesting example of a site you can access via Tor.