
Total darknet market revenue fell from $2.3 billion in 2023 to $2 billion in 2024. Each of our coin data pages has a graph that shows both the current and historic price information for the coin or token. Normally, the graph starts at the launch of the asset, but it is possible to select specific to and from dates to customize the chart to your own needs. The most experienced and professional traders often choose to use the best crypto API on the market. Our API enables millions of calls to track current prices and to also investigate historic prices and is used by some of the largest crypto exchanges and financial institutions in the world.
P2P (Peer-to-Peer) Exchanges
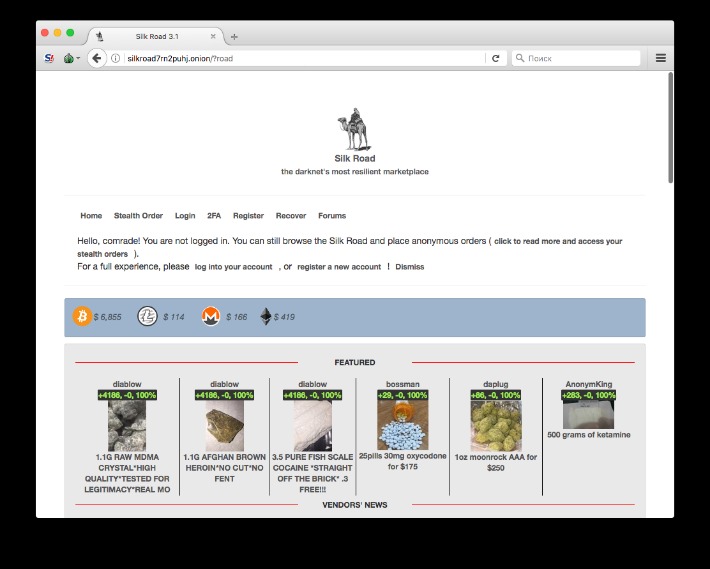
Most of the stolen cryptocurrency from Monkey Drainer was laundered through Tornado Cash. In some cases the fraudsters used intermediary wallets before attempting to cash out stolen funds at three centralized exchanges. Since the demise of Monkey Drainer, others, such as Venom Drainer, have filled the niche. Unlike traditional payment methods cryptocurrencies don’t require personal details like credit card numbers or bank accounts making the transactions more private. ASAP is a tech nerd’s playground—accepting BTC, LTC, ZCash, and Monero, it’s got options for days. Their DeadDrop system’s a standout—vendors stash your goods IRL, no mailing hassles—and wallet-less payments mean no one’s bolting with your cash, a relief after I got burned once by a shady escrow dodge.
Trump Media’s $64 Billion Crypto Push: What It Means For CRO, Politics, And The Future Of Crypto Adoption
- If macroeconomic conditions favor risk-on assets, Ethereum could see strong upward price pressure throughout the year.
- As looping strategies accelerate growth and Horizon positions the protocol to ride the RWA wave, Aave is shaping up as one of DeFi’s most compelling multi-narrative plays.
- On-chain data from BitInfoCharts shows that the daily number of monero transactions has halved from this time last year.
- The ASAP is a moderate design marketplace on the dark web that offers helpful tools like mandatory PGP encryption and two-factor authentication for a safe browsing experience.
- High-risk exchanges and other VASPs are characterized by lax compliance controls or are located in jurisdictions with weak regulatory oversight, which makes them attractive channels for money laundering activities.
In doing so, these forums play a significant role in connecting and driving cybercrime. Cybercrime forums derive their income from registration fees, advertisements, escrow services and account status upgrades. On one hand, it offers privacy for whistleblowers, journalists, and citizens in oppressive countries. On the other hand, it’s notorious for enabling illegal activity, including drug sales, weapons trafficking, counterfeit ID trading, hacking services, and the exchange of stolen personal data.
How To Compare Assets With This Crypto Comparison Tool?
A smaller and more elusive subset of illicit commerce concerns child sexual abuse materials (CSAM). It offers impressive features, including PGP-signed addresses, payment via Monera, sticky and featured listings, and auto shops. In 2017, the website went offline following a law enforcement action taken by the American, Canadian, and Thai authorities, but since August 2021, it’s been operational again.
Set Up Tor Browser
Bitcoin and Monero are the main payment options, reflecting the market’s emphasis on anonymity and decentralized commerce. Cryptocurrencies have revolutionized the global finance environment with financial inclusion, efficiency, and decentralization capabilities. However, these digital assets also present significant risks, becoming tools for illicit activities such as money laundering, terrorist financing, and fraud.
The report documents a noticeable drop, from $2.3 billion in 2023 to $2 billion last year. This decrease may indicate that intensified regulatory efforts and proactive disruption by law enforcement are beginning to impact darknet operations. Centralized exchanges still dominate as the primary method for laundering illicit funds, yet darknet vendors’ growing use of decentralized platforms represents a notable and alarming trend. The rise of NFTs and DeFi platforms has introduced new financial opportunities but also significant risks.

After migrating the funds to the Ethereum blockchain and swapping them from USDC to ETH, the actor sends them to various wallets before depositing them into Tornado Cash. In addition to their primary role in crypto crime – the sale of illicit drugs – darknet markets (DNMs) are also involved in the laundering of proceeds from crime. Over the course of 2022, TRM Labs has witnessed a rise in international criminals using Russian-language DNMs to launder money. Frosties NFT was another NFT project that promised exclusive digital art and collectibles. However, shortly after the project’s launch the two 20-year-old creators shut down its website and Discord servers, removed the liquidity from the trading pool and disappeared with USD 1.1 million of investors’ funds.
Security And Anonymity On The Dark Web

Programmatic money laundering (PML) includes using software to quickly move funds through hundreds or thousands of transactions, in an attempt to obfuscate the illicit origin. One of the most high-profile examples of cryptocurrency-based PML involved the North Korean Military in 2021. In April 2023, a Missouri woman was arrested on charges of assisting with the movement of stolen funds.
Ethereum Supported Platforms
Such content fuels a dangerous cycle of abuse, violence, and exploitation. Understandably, as in the case with most illicit trade markets, you don’t even need to verify your email Awazon. Despite these efforts, dark web operators rebuild quickly, often with better security and decentralized tools. Market takedowns create temporary disruptions, but they rarely dismantle entire networks. Sophisticated players shift operations, adopt new aliases, and resume business within weeks.
The Rise Of Crypto Fraud
Thus, use the best antivirus software that protects against these online threats. The website allows visitors to view all the goods and services on display before they buy something. However, the platform lacks an advanced search option and a wallet-free payment option. The vendors aren’t required to register or apply for a vendor account while using this platform.
Features like multi-signature wallets, end-to-end encrypted messaging, and decentralized hosting environments reduce the risk of detection. Many vendors rotate addresses and aliases regularly to avoid tracking and maintain anonymity. Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures. Additional layers, such as two-factor authentication (2FA), encrypted PGP messaging, and built-in wallet security, significantly enhance protection against theft and hacking. Transactions within these marketplaces typically leverage cryptocurrencies—most commonly Monero, Bitcoin, and privacy-centric digital currencies developed specifically to enhance transaction anonymity.
Unregulated World Of Opinion Trading: What Investors Need To Be Aware Of?
SUEX, a crypto exchange and OTC broker sanctioned by OFAC in 2021, operated as a parasite exchange and was complicit in laundering millions of dollars for Russian ransomware groups. In the case shown above, a single exchange address received funds from 40 different cash-to-crypto services ATMs located all over North America. The same address was reported in multiple public reports and investigations as being used by scammers as an aggregator and off-ramp for stolen funds. In this case, the significant number of transfers from multiple cash-to-crypto service locations to the same address served as the trigger for investigators to identify the suspicious destination address. Infrastructure attacks target the systems, platforms, or services that support the creation, exchange, or storage of cryptocurrencies.
At the heart of Ethereum is the Ethereum Virtual Machine (EVM), an execution environment that processes smart contracts, ensuring that code runs exactly as written without central oversight. This design enables developers to build applications that operate in a trustless and transparent manner, serving use cases in areas such as finance, digital identity, and supply chain management. Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace. Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security.
Such models ensure that the market remains community-controlled and resilient to outside interference. Monero’s ring signatures, stealth addresses, and RingCT obfuscate transaction details—enhancing privacy and hindering traceability The Rise of Monero. Sites such as Abacus and Russian Market accept both currencies to broaden their appeal. If you’ve decided to go with Bitcoin after comparing BTC vs ETH, the most recommended exchange to buy it is Binance.


