
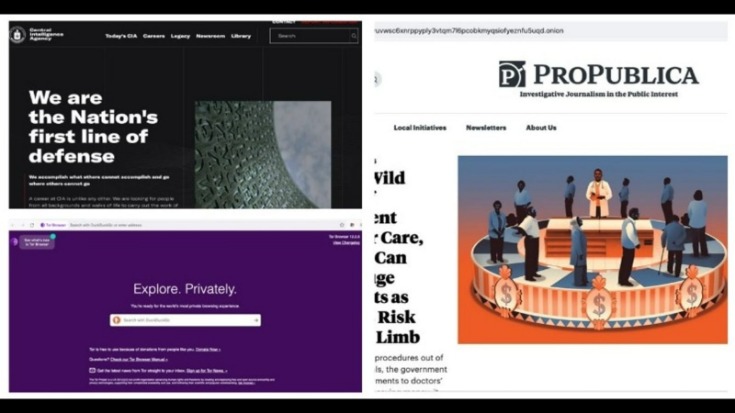
This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. For this reason, you cannot browse through these sites using your default search engine. The biggest and most frustrating part about dark websites is that they live for a short span of time. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies. Using the ProtonMail .onion site offers security and privacy advantages.
How Do I Know If A Site Is Safe?
To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. An easy way to find content on the dark web is to receive a link from someone who already knows about it. No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged.
- The middle node knows the previous node but not your IP address or what you’ve requested online.
- Without a VPN, your ISP can see that you’re using Tor, and the first Tor server (entry node) can see your real IP address.
- We will discuss the setup procedure, ensuring security and anonymity, and offer tips for navigating the dark web safely.
- Whether you are accessing your email account, private backups, or your credit card statements, that data is stored on the deep web.
- Surfing the Dark Web on an iPhone takes a few extra steps compared to Android.
What Services And Tools Are Available On The Dark Web?
You can also use DuckDuckGo to find onion sites across the Tor network. To maximize security, you should avoid logging into personal accounts, such as Facebook and Gmail, via Tor. Although the Tor Browser is designed with strict privacy, logging into personal accounts can expose your real identity. To surf the web privately, you need to connect to the Tor network from your browser.
Words Of Caution When Using Dark Web Sites
Deep web content includes academic research papers, court documents, or medical records. For example, when you sign in to your healthcare provider’s portal to view test results or request prescription refills, you’re accessing the deep web. We also recommend that you use a VPN for Tor, as this will ensure that you add an extra layer of privacy to your connection to Tor. Head over to our page on how to safely access the dark web for some top security tip. This setup is easy to configure, and you don’t need any special settings or features. Just turn on your VPN, wait for the connection to stabilize, and launch Tor.
How Can I Differentiate Legitimate Services From Scams On The Dark Web?
However, its network is still small, and there aren’t many hidden services available yet. Even with Tor and a VPN, you’re not fully protected unless you also lock down your behavior. Most dark web leaks happen when users skip basic safety steps or reveal too much without realizing it. Use the tips below to patch common blind spots and avoid easy-to-make mistakes. Don’t log into any real accounts, reuse usernames, or enter any personal details. Treat every site as untrusted unless you’ve verified it from multiple sources.
Final Verdict: Is The Dark Web Illegal?
To ensure your traffic is properly routed through the Tor network, you’ll also need to install Orbot, which helps secure and anonymize your connection. Tor isn’t available for iOS due to Apple’s restrictions, but you can still access the dark web on your iPhone using the Onion Browser, which is from the Tor Project. This app connects to the Tor network, allowing you to visit .onion sites.
Private Internet Access
After completing these steps, Tor Browser will open, and you will be ready to start browsing the internet anonymously. Tor Browser is pre-configured with privacy settings optimized for secure browsing, so you can enjoy a higher level of anonymity right from the start. It is crucial to approach the dark web with caution and understand the risks involved. Engaging in illegal activities can lead to severe consequences, and exposing personal information or engaging with malicious individuals can compromise your privacy and security.
Simply accessing the dark web and using the Tor browser may already raise government suspicion. Anyone can access the dark web, and it’s not that complicated to do so. Just remember, if you want to explore the dark web, be very careful. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Keep in mind what you’re looking for, find that information, and disconnect from the dark web. As enticing as it might be, don’t follow links to other parts of the dark web.
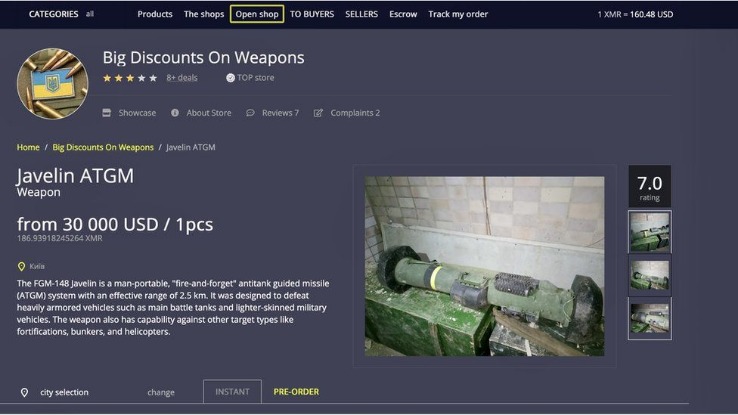
The aim is to reduce your online footprint as much as possible, anonymize your traffic, and disguise your location. Drugs, weapons, and stolen IP and data are all hot businesses on the dark web, with terabytes of information on offer. You could consider the clear or surface web the “top” and visible layer of the internet, easily accessible using a browser such as Safari, Chrome, Edge, or Firefox. Our editors thoroughly review and fact-check every article to ensure that our content meets the highest standards.
This is a trade-off for the increased privacy and anonymity it provides. The top layer is referred to as the clear or “surface web,” which is what you’re accessing while reading this article. The clear web is made up of websites that you can get to via a search engine like Ecosia or Google. Your clear web browser activity can be logged and tracked by advertisers, governments, and your ISP if you’re not using a VPN. Another challenge of finding dark web sites is that they don’t often last long. Many sites become defunct quickly, either because they are shut down due to illegal activity, their founders lose interest, or they change addresses and names to avoid detection.
It uses technology like onion routing to hide users’ identities and encrypt their communications. The dark web is often misunderstood due to the illegal activities that occur within its depths. However, it’s important to note that not everything on the dark web is illegal. Journalists, activists, and individuals concerned about privacy and censorship often use the dark web to communicate securely and anonymously. Nevertheless, caution should always be exercised when venturing into this hidden realm. To access those specific darknet networks, you will need to use the specific browsers developed for them.
On its own, Tor obscures your IP address by bouncing online requests through multiple servers, similar to how a VPN routes your traffic through an external server. Websites you visit via Tor will see the IP address of the exit node, not your actual IP, just like websites see the IP address of your remote server when using a VPN. Tor doesn’t support plugins because they introduce security risks. Malicious actors often target browser plugins to steal website credentials or install malware on unsuspecting devices, so Tor sidesteps these risks altogether.
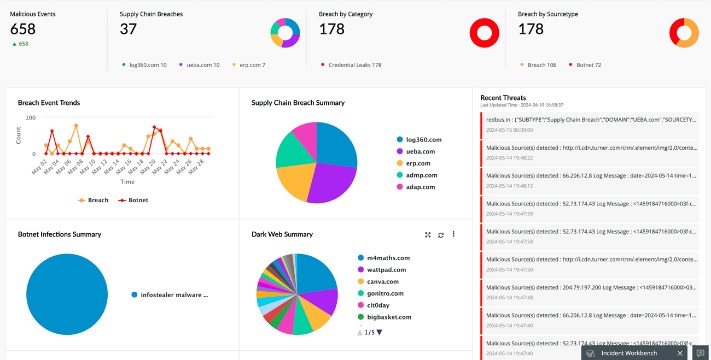
The area of the internet we access daily is known as the clear or surface web. The internet opened the door to a realm of possibilities that permanently changed the business landscape and our personal lives. In a world of bulk data collection, surveillance, and personalized ad tracking, it’s up to us to take control of our personal privacy. Banking trojans and information stealers are quite common on the dark web. One notorious example is the “Godfather” banking bot that infects devices through unsuspecting advertisements to steal SMS messages and transfer money. Another threat is the “Dark Tequila” virus, a backdoor that targets Mexican and Latin American systems in the Spanish language.



